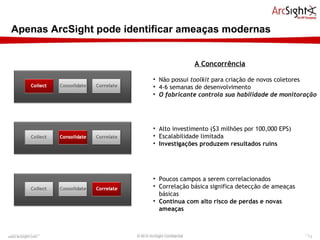
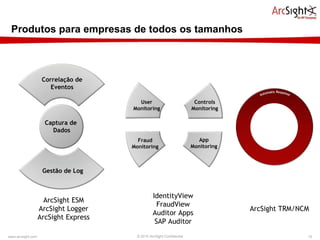
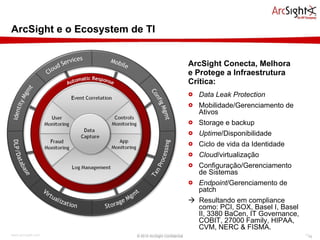
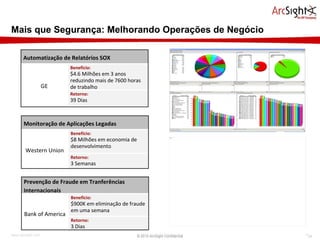
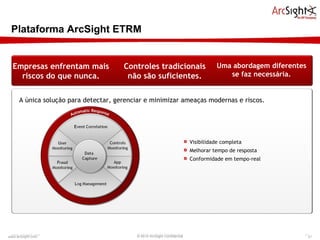
O documento descreve a plataforma ArcSight de gerenciamento de riscos e ameaças (ETRM), destacando que monitorar está mais desafiador devido a novas ameaças. A ArcSight permite visibilidade completa ao detectar sistemas, ameaças, dados, violações e usuários privilegiados na rede. Sua plataforma coleta eventos de qualquer ativo para análise e identificar comportamentos anômalos rapidamente.