Class3
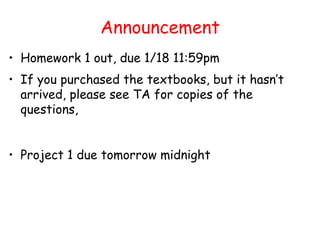
- 1. Announcement • Homework 1 out, due 1/18 11:59pm • If you purchased the textbooks, but it hasn’t arrived, please see TA for copies of the questions, • Project 1 due tomorrow midnight
- 2. Review • Overview of Cryptography • Classical Symmetric Cipher – Substitution Cipher – Transposition Cipher – Product Cipher • Modern Symmetric Ciphers (DES)
- 3. Basic Terminology • plaintext - the original message • ciphertext - the coded message • cipher - algorithm for transforming plaintext to ciphertext • key - info used in cipher known only to sender/receiver • encipher (encrypt) - converting plaintext to ciphertext • decipher (decrypt) - recovering ciphertext from plaintext • cryptography - study of encryption principles/methods • cryptanalysis (codebreaking) - the study of principles/ methods of deciphering ciphertext without knowing key • cryptology - the field of both cryptography and cryptanalysis
- 4. Feistel Cipher Structure • Feistel cipher implements Shannon’s S-P network concept – based on invertible product cipher • Process through multiple rounds which – partitions input block into two halves – perform a substitution on left data half – based on round function of right half & subkey – then have permutation swapping halves
- 5. Feistel Cipher Structure • Feistel cipher implements Shannon’s S-P network concept • Achieve diffusion and confusion
- 6. DES (Data Encryption Standard) • Published in 1977, standardized in 1979. • Key: 64 bit quantity=8-bit parity+56-bit key – Every 8th bit is a parity bit. • 64 bit input, 64 bit output. DES Encryption 64 bit M 64 bit C 56 bits
- 7. DES Top View Permutation Permutation Swap Round 1 Round 2 Round 16 Generate keys Initial Permutation 48-bit K1 48-bit K2 48-bit K16 Swap 32-bit halves Final Permutation 64-bit Output 48-bit K164-bit Input 56-bit Key …...
- 8. Bit Permutation (1-to-1) ……. …….. 1 2 3 4 32 22 6 13 32 3 Input: Output 0 0 1 0 1 1 0 1 1 1 1 bit
- 9. Per-Round Key Generation 28 bits 28 bits 48 bits Ki One round Circular Left Shift Circular Left Shift 28 bits 28 bits Permutation with Discard Initial Permutation of DES key C i-1 D i-1 C i D i Round 1,2,9,16: single shift Others: two bits
- 10. A DES Round 48 bits 32 bits 32 bits Ln 32 bits Rn 32 bits Ln+1 32 bits Rn+1 E S-Boxes P 48 bits Ki One Round Encryption Mangler Function
- 11. Mangler Function 4444444 4 6666666 6 + + +++ ++ + 6666666 6 S8S1 S2 S7S3 S4 S5 S6 4444444 4 Permutation The permutation produces “spread” among the chunks/S-boxes!
- 12. Bits Expansion (1-to-m) ……. …….. 1 2 3 4 5 32 Input: Output 0 0 1 0 1 1 1 2 3 4 5 6 7 8 48 1 0 0 1 0 1 0 1 1 0
- 13. S-Box (Substitute and Shrink) • 48 bits ==> 32 bits. (8*6 ==> 8*4) • 2 bits used to select amongst 4 substitutions for the rest of the 4-bit quantity 2 bits row Si i = 1,…8. I1 I2 I3 I4 I5 I6 O1 O2 O3 O4 4 bits column
- 14. S-Box Example (S-Box 1) 0 1 2 3 4 5 6 7 8 9…. 15 0 14 4 13 1 2 15 11 8 3 1 0 15 7 4 14 2 13 1 10 2 4 1 14 8 13 6 2 11 15 3 15 12 8 2 4 9 1 7 5 Each row and column contain different numbers. Example: input: 100110 output: ???
- 15. DES Standard • Cipher Iterative Action : – Input: 64 bits – Key: 48 bits – Output: 64 bits • Key Generation Box : – Input: 56 bits – Output: 48 bits One round (Total 16 rounds)
- 16. DES Box Summary • Simple, easy to implement: – Hardware/gigabits/second, software/megabits/second • 56-bit key DES may be acceptable for non- critical applications but triple DES (DES3) should be secure for most applications today • Supports several operation modes (ECB CBC, OFB, CFB) for different applications
- 17. Outlines • Strength/weakness of DES, AES • Public Key Cryptography • Modular Arithmetic • RSA
- 18. Avalanche Effect • Key desirable property of encryption alg • Where a change of one input or key bit results in changing more than half output bits • DES exhibits strong avalanche
- 19. Strength of DES – Key Size • 56-bit keys have 256 = 7.2 x 1016 values • Brute force search looks hard • Recent advances have shown is possible – in 1997 on a huge cluster of computers over the Internet in a few months – in 1998 on dedicated hardware called “DES cracker” by EFF in a few days ($220,000) – in 1999 above combined in 22hrs! • Still must be able to recognize plaintext • No big flaw for DES algorithms
- 20. DES Replacement • Triple-DES (3DES) – 168-bit key, no brute force attacks – Underlying encryption algorithm the same, no effective analytic attacks – Drawbacks • Performance: no efficient software codes for DES/3DES • Efficiency/security: bigger block size desirable • Advanced Encryption Standards (AES) – US NIST issued call for ciphers in 1997 – Rijndael was selected as the AES in Oct-2000
- 21. AES • Private key symmetric block cipher • 128-bit data, 128/192/256-bit keys • Stronger & faster than Triple-DES • Provide full specification & design details • Evaluation criteria – security – effort to practically cryptanalysis – cost – computational – algorithm & implementation characteristics
- 22. Outlines • Strength/weakness of DES, AES • Public Key Cryptography • Modular Arithmetic • RSA
- 23. Private-Key Cryptography • Private/secret/single key cryptography uses one key • Shared by both sender and receiver • If this key is disclosed communications are compromised • Also is symmetric, parties are equal • Hence does not protect sender from receiver forging a message & claiming is sent by sender
- 24. Public-Key Cryptography • Probably most significant advance in the 3000 year history of cryptography • Uses two keys – a public & a private key • Asymmetric since parties are not equal • Uses clever application of number theoretic concepts to function • Complements rather than replaces private key crypto
- 25. Public-Key Cryptography • Public-key/two-key/asymmetric cryptography involves the use of two keys: – a public-key, which may be known by anybody, and can be used to encrypt messages, and verify signatures – a private-key, known only to the recipient, used to decrypt messages, and sign (create) signatures • Asymmetric because – those who encrypt messages or verify signatures cannot decrypt messages or create signatures
- 27. Public-Key Characteristics • Public-Key algorithms rely on two keys with the characteristics that it is: – computationally infeasible to find decryption key knowing only algorithm & encryption key – computationally easy to en/decrypt messages when the relevant (en/decrypt) key is known – either of the two related keys can be used for encryption, with the other used for decryption (in some schemes)
- 28. Public-Key Cryptosystems • Two major applications: – encryption/decryption (provide secrecy) – digital signatures (provide authentication)
- 29. Outlines • Strength/weakness of DES, AES • Public Key Cryptography • Modular Arithmetic • RSA
- 30. Modular Arithmetic • Public key algorithms are based on modular arithmetic. • Modular addition. • Modular multiplication. • Modular exponentiation.
- 31. Modular Addition • Addition modulo (mod) K – Poor cipher with (dk+dm) mod K, e.g., if K=10 and dk is the key. • Additive inverse: addition mod K yields 0. • “Decrypt” by adding inverse. + 0 1 2 3 4 5 6 7 8 9 0 0 0 0 0 0 0 0 0 0 0 1 1 2 3 4 5 6 7 8 9 0 2 2 3 4 5 6 7 8 9 0 1 3 3 4 5 6 7 8 9 0 1 2
- 32. Modular Multiplication • Multiplication modulo K • Multiplicative inverse: multiplication mod K yields 1 • Only some numbers have inverse * 0 1 2 3 4 5 6 7 8 9 0 0 0 0 0 0 0 0 0 0 0 1 1 2 3 4 5 6 7 8 9 1 2 0 2 4 6 8 0 2 4 6 8 3 0 3 6 9 2 5 8 1 4 7
- 33. Modular Multiplication • Only the numbers relatively prime to n will have mod n multiplicative inverse • x, m relative prime: no other common factor than 1 – Eg. 8 & 15 are relatively prime - factors of 8 are 1,2,4,8 and of 15 are 1,3,5,15 and 1 is the only common factor
- 34. Totient Function • Totient function ø(n): number of integers less than n relatively prime to n – if n is prime, • ø(n)=n-1 – if n=p∗q, and p, q are primes, p != q • ø(n)=(p-1)(q-1) – E.g., • ø(37) = 36 • ø(21) = (3–1)×(7–1) = 2×6 = 12
- 35. Modular Exponentiation xy 0 1 2 3 4 5 6 7 8 9 0 0 0 0 0 0 0 0 0 0 1 1 1 1 1 1 1 1 1 1 1 2 1 2 4 8 6 2 4 8 6 2 3 1 3 9 7 1 3 9 7 1 3 4 1 4 6 4 6 4 6 4 6 4 5 1 5 5 5 5 5 5 5 5 5 6 1 6 6 6 6 6 6 6 6 6 7 1 7 9 3 1 7 9 3 1 7 8 1 8 4 2 6 8 4 2 6 8 9 1 9 1 9 1 9 1 9 1 9
- 36. Modular Exponentiation • xy mod n = xy mod ø(n) mod n • if y = 1 mod ø(n) then xy mod n = x mod n
- 37. Outlines • Strength/weakness of DES, AES • Public Key Cryptography • Modular Arithmetic • RSA
- 38. RSA (Rivest, Shamir, Adleman) • The most popular one. • Support both public key encryption and digital signature. • Assumption/theoretical basis: – Factoring a big number is hard. • Variable key length (usually 512 bits). • Variable plaintext block size. – Plaintext must be “smaller” than the key. – Ciphertext block size is the same as the key length.
- 39. What Is RSA? • To generate key pair: – Pick large primes (>= 256 bits each) p and q – Let n = p*q, keep your p and q to yourself! – For public key, choose e that is relatively prime to ø(n) =(p-1)(q-1), let pub = <e,n> – For private key, find d that is the multiplicative inverse of e mod ø(n), i.e., e*d = 1 mod ø(n), let priv = <d,n>
- 40. RSA Example 1. Select primes: p=17 & q=11 2. Compute n = pq =17×11=187 3. Compute ø(n)=(p–1)(q-1)=16×10=160 4. Select e : gcd(e,160)=1; choose e=7 5. Determine d: de=1 mod 160 and d < 160 Value is d=23 since 23×7=161= 10×160+1 6. Publish public key KU={7,187} 7. Keep secret private key KR={23,17,11}
- 41. How Does RSA Work? • Given pub = <e, n> and priv = <d, n> – encryption: c = me mod n, m < n – decryption: m = cd mod n – signature: s = md mod n, m < n – verification: m = se mod n • given message M = 88 (nb. 88<187) • encryption: C = 887 mod 187 = 11 • decryption: M = 1123 mod 187 = 88
- 42. Why Does RSA Work? • Given pub = <e, n> and priv = <d, n> – n =p*q, ø(n) =(p-1)(q-1) – e*d = 1 mod ø(n) – xe∗d = x mod n – encryption: c = me mod n – decryption: m = cd mod n = me∗d mod n = m mod n = m (since m < n) – digital signature (similar)
- 43. Is RSA Secure? • Factoring 512-bit number is very hard! • But if you can factor big number n then given public key <e,n>, you can find d, hence the private key by: – Knowing factors p, q, such that, n = p*q – Then ø(n) =(p-1)(q-1) – Then d such that e*d = 1 mod ø(n) • Threat – Moore’s law – Refinement of factorizing algorithms • For the near future, a key of 1024 or 2048 bits needed
- 44. Symmetric (DES) vs. Public Key (RSA) • Exponentiation of RSA is expensive ! • AES and DES are much faster – 100 times faster in software – 1,000 to 10,000 times faster in hardware • RSA often used in combination in AES and DES – Pass the session key with RSA
Notas do Editor
- Briefly review some terminology used throughout the course.
- Horst Feistel, working at IBM Thomas J Watson Research Labs devised a suitable invertible cipher structure in early 70&apos;s. One of Feistel&apos;s main contributions was the invention of a suitable structure which adapted Shannon&apos;s S-P network in an easily inverted structure. Essentially the same h/w or s/w is used for both encryption and decryption, with just a slight change in how the keys are used. One layer of S-boxes and the following P-box are used to form the round function.
- DES finally and definitively proved insecure in July 1998, when the Electronic Frontier Foundation (EFF) announced that it had broken a DES encryption using a special-purpose &quot;DES cracker&quot; machine that was built for less than $250,000. The attack took less than three days. The EFF has published a detailed description of the machine, enabling others to build their own cracker [EFF98].
- The AES candidates are the latest generation of block ciphers, and now we see a significant increase in the block size - from the old standard of 64-bits up to 128-bits; and keys from 128 to 256-bits. In part this has been driven by the public demonstrations of exhaustive key searches of DES. Whilst triple-DES is regarded as secure and well understood, it is slow, especially in s/w.
- So far all the cryptosystems discussed have been private/secret/single key (symmetric) systems. All classical, and modern block and stream ciphers are of this form.
- Will now discuss the radically different public key systems, in which two keys are used. Anyone knowing the public key can encrypt messages or verify signatures, but cannot decrypt messages or create signatures, counter-intuitive though this may seem. It works by the clever use of number theory problems that are easy one way but hard the other. Note that public key schemes are neither more secure than private key (security depends on the key size for both), nor do they replace private key schemes (they are too slow to do so), rather they complement them.
- Stallings Fig 9.1
- Public key schemes utilise problems that are easy (P type) one way but hard (NP type) the other way, eg exponentiation vs logs, multiplication vs factoring. Consider the following analogy using padlocked boxes: traditional schemes involve the sender putting a message in a box and locking it, sending that to the receiver, and somehow securely also sending them the key to unlock the box. The radical advance in public key schemes was to turn this around, the receiver sends an unlocked box to the sender, who puts the message in the box and locks it (easy - and having locked it cannot get at the message), and sends the locked box to the receiver who can unlock it (also easy), having the key. An attacker would have to pick the lock on the box (hard).
- Stallings Fig 9.4 Here see various components of public-key schemes used for both secrecy and authentication. Note that separate key pairs are used for each of these – receiver owns and creates secrecy keys, sender owns and creates authentication keys.
- Here walk through example using “trivial” sized numbers. Selecting primes requires the use of primality tests. Finding d as inverse of e mod ø(n) requires use of Inverse algorithm (see Ch4)