Ns2 2015 2016 ieee project list-(v)_with abstract(S3 Infotech:9884848198)
•Transferir como DOCX, PDF•
0 gostou•495 visualizações
S3 INFOTECH +91 988 48 48 198 # 10/1, Jones Road, Saidapet, Chennai – 15. Ph: 044-3201 7467, 9884848198. www.s3computers.com E-Mail: info@s3computers.com The document lists 10 project titles from IEEE 2015 related to wireless networks and security. The projects address topics such as detecting malicious nodes in mobile ad hoc networks, enhancing security and caching in MANETs, providing multicast connectivity in flexgrid optical networks, and optimizing resource allocation and base station selection in heterogeneous networks.
Denunciar
Compartilhar
Denunciar
Compartilhar
Recomendados
There are number of cluster based routing algorithms in mobile ad hoc networks. Since ad hoc networks are not accompanied by fixed access points, efficient routing is a must for such networks. Clustering approach is applied in mobile ad hoc network because clusters are more easily manageable and are more viable. It consists of segregating the given network into several reasonable clusters by using a clustering algorithm. By performing clustering we elect a worthy node from the cluster as the cluster head in such a way that we strive to reduce the management overheads and thus increasing the efficiency of routing. As for the fact that nodes in mobile ad hoc network have frequent host change and frequent topology change routing plays an important role for maintenance and backup mechanism to stabilize network performance. This paper aims to review the previous research papers and provide a survey on the various cluster based routing protocols in mobile ad hoc network. This paper presents analytical study of cluster based routing algorithms from literature. Index Terms— Ad- hoc networks, Cluster head, Clustering, Protocol, Route selection.Analytical Study of Cluster Based Routing Protocols in MANET

Analytical Study of Cluster Based Routing Protocols in MANETInternational Journal of Computer and Communication System Engineering
IEEE 2015 completed projects ME,M.Tech_ready for delivery(dotnet,java,VLSI,NS2)
More details call : +91.9884848198
www.s3computers.com
info@s3computers.com
10/1, Jones Road,
Saidpet, Chennai-15.
Tamilnadu, India.IEEE 2015 completed projects ME,M.Tech_ready for delivery(dotnet,java,VLSI,NS2)

IEEE 2015 completed projects ME,M.Tech_ready for delivery(dotnet,java,VLSI,NS2)S3 Infotech IEEE Projects
Mais conteúdo relacionado
Mais procurados
There are number of cluster based routing algorithms in mobile ad hoc networks. Since ad hoc networks are not accompanied by fixed access points, efficient routing is a must for such networks. Clustering approach is applied in mobile ad hoc network because clusters are more easily manageable and are more viable. It consists of segregating the given network into several reasonable clusters by using a clustering algorithm. By performing clustering we elect a worthy node from the cluster as the cluster head in such a way that we strive to reduce the management overheads and thus increasing the efficiency of routing. As for the fact that nodes in mobile ad hoc network have frequent host change and frequent topology change routing plays an important role for maintenance and backup mechanism to stabilize network performance. This paper aims to review the previous research papers and provide a survey on the various cluster based routing protocols in mobile ad hoc network. This paper presents analytical study of cluster based routing algorithms from literature. Index Terms— Ad- hoc networks, Cluster head, Clustering, Protocol, Route selection.Analytical Study of Cluster Based Routing Protocols in MANET

Analytical Study of Cluster Based Routing Protocols in MANETInternational Journal of Computer and Communication System Engineering
Mais procurados (10)
Energy and Load Aware Routing Protocol for Internet of Things

Energy and Load Aware Routing Protocol for Internet of Things
ENHANCED PARTICLE SWARM OPTIMIZATION FOR EFFECTIVE RELAY NODES DEPLOYMENT IN ...

ENHANCED PARTICLE SWARM OPTIMIZATION FOR EFFECTIVE RELAY NODES DEPLOYMENT IN ...
A Secure Data Transmission Scheme using Asymmetric Semi-Homomorphic Encryptio...

A Secure Data Transmission Scheme using Asymmetric Semi-Homomorphic Encryptio...
AN EFFICIENT INTRUSION DETECTION SYSTEM WITH CUSTOM FEATURES USING FPA-GRADIE...

AN EFFICIENT INTRUSION DETECTION SYSTEM WITH CUSTOM FEATURES USING FPA-GRADIE...
Analytical Study of Cluster Based Routing Protocols in MANET

Analytical Study of Cluster Based Routing Protocols in MANET
A COMBINATION OF THE INTRUSION DETECTION SYSTEM AND THE OPEN-SOURCE FIREWALL ...

A COMBINATION OF THE INTRUSION DETECTION SYSTEM AND THE OPEN-SOURCE FIREWALL ...
Destaque
IEEE 2015 completed projects ME,M.Tech_ready for delivery(dotnet,java,VLSI,NS2)
More details call : +91.9884848198
www.s3computers.com
info@s3computers.com
10/1, Jones Road,
Saidpet, Chennai-15.
Tamilnadu, India.IEEE 2015 completed projects ME,M.Tech_ready for delivery(dotnet,java,VLSI,NS2)

IEEE 2015 completed projects ME,M.Tech_ready for delivery(dotnet,java,VLSI,NS2)S3 Infotech IEEE Projects
Final year IEEE 2016-2017 PROJECTS TITLES (IEEE 2016 papers) For ME,M.Tech,BE,B.Tech (.net,java,matlab,vlsi,ns2,mech,power elc & power sys)Final year IEEE 2016-2017 PROJECTS TITLES (IEEE 2016 papers) For ME,M.Tech,BE...

Final year IEEE 2016-2017 PROJECTS TITLES (IEEE 2016 papers) For ME,M.Tech,BE...S3 Infotech IEEE Projects
Destaque (17)
Matlab IEEE 2015 2016 ieee project list (S3 Infotech-9884848198)

Matlab IEEE 2015 2016 ieee project list (S3 Infotech-9884848198)
Vlsi 2015 2016 ieee project list-(v)_with abstract

Vlsi 2015 2016 ieee project list-(v)_with abstract
Dotnet 2015 2016 ieee project list-(v)_with abstract

Dotnet 2015 2016 ieee project list-(v)_with abstract
IEEE 2015 completed projects ME,M.Tech_ready for delivery(dotnet,java,VLSI,NS2)

IEEE 2015 completed projects ME,M.Tech_ready for delivery(dotnet,java,VLSI,NS2)
Mca(.net & java) application projects abstracts(v)

Mca(.net & java) application projects abstracts(v)
Final year IEEE 2016-2017 PROJECTS TITLES (IEEE 2016 papers) For ME,M.Tech,BE...

Final year IEEE 2016-2017 PROJECTS TITLES (IEEE 2016 papers) For ME,M.Tech,BE...
Semelhante a Ns2 2015 2016 ieee project list-(v)_with abstract(S3 Infotech:9884848198)
Optical network is an emerging technology for data communication
inworldwide. The information is transmitted from the source to destination
through the fiber optics. All optical network (AON) provides good
transmission transparency, good expandability, large bandwidth, lower bit
error rate (BER), and high processing speed. Link failure and node failure
haveconsistently occurred in the traditional methods. In order to overcome
the above mentioned issues, this paper proposes a robust software defined
switching enabled fault localization framework (SDSFLF) to monitor the
node and link failure in an AON. In this work, a novel faulty node
localization (FNL) algorithm is exploited to locate the faulty node. Then, the
software defined faulty link detection (SDFLD) algorithm that addresses the
problem of link failure. The failures are localized in multi traffic stream
(MTS) and multi agent system (MAS). Thus, the throughput is improved in
SDSFLF compared than other existing methods like traditional routing and
wavelength assignment (RWA), simulated annealing (SA) algorithm, attackaware RWA (A-RWA) convex, longest path first (LPF) ordering, and
biggest source-destination node degree (BND) ordering. The performance of
the proposed algorithm is evaluated in terms of network load, wavelength
utilization, packet loss rate, and burst loss rate. Hence, proposed SDSFLF
assures that high performance is achieved than other traditional techniques.SDSFLF: fault localization framework for optical communication using softwar...

SDSFLF: fault localization framework for optical communication using softwar...International Journal of Reconfigurable and Embedded Systems
Semelhante a Ns2 2015 2016 ieee project list-(v)_with abstract(S3 Infotech:9884848198) (20)
Ieee transactions on networking 2018 Title with Abstract 

Ieee transactions on networking 2018 Title with Abstract
Ieee acm transactions 2018 on networking topics with abstract for final year ...

Ieee acm transactions 2018 on networking topics with abstract for final year ...
SDSFLF: fault localization framework for optical communication using softwar...

SDSFLF: fault localization framework for optical communication using softwar...
Mobile Agents based Energy Efficient Routing for Wireless Sensor Networks

Mobile Agents based Energy Efficient Routing for Wireless Sensor Networks
Reliable and Efficient Data Acquisition in Wireless Sensor Network

Reliable and Efficient Data Acquisition in Wireless Sensor Network
Minimum Process Coordinated Checkpointing Scheme For Ad Hoc Networks 

Minimum Process Coordinated Checkpointing Scheme For Ad Hoc Networks
Reconfigurable High Performance Secured NoC Design Using Hierarchical Agent-b...

Reconfigurable High Performance Secured NoC Design Using Hierarchical Agent-b...
Balancing Trade-off between Data Security and Energy Model for Wireless Senso...

Balancing Trade-off between Data Security and Energy Model for Wireless Senso...
Ncct Ieee Software Abstract Collection Volume 1 50+ Abst

Ncct Ieee Software Abstract Collection Volume 1 50+ Abst
Energy Proficient and Security Protocol for WSN: A Review

Energy Proficient and Security Protocol for WSN: A Review
A Cooperative Cache Management Scheme for IEEE802.15.4 based Wireless Sensor ...

A Cooperative Cache Management Scheme for IEEE802.15.4 based Wireless Sensor ...
Wireless Networks Projects, Network Security Projects, Networking Project

Wireless Networks Projects, Network Security Projects, Networking Project
Best Final Year Projects Latest New Innovative And Ieee 2009 2010 (1)

Best Final Year Projects Latest New Innovative And Ieee 2009 2010 (1)
Software Projects A Sp.Net Projects Ieee Projects Domains

Software Projects A Sp.Net Projects Ieee Projects Domains
Mais de S3 Infotech IEEE Projects
DOTNET/JAVA/MATLAB/VLSI/NS2/EMBEDDED IEEE 2014 PROJECTS FOR ME/BE/B.TECH STUDENTS. FINAL YEAR 2014 PROJECTS FOR CSE/IT/ECE/EEE/ STUDENTS IN CHENNAI (S3 INFOTECH : 09884848198).
Final year IEEE 2014 projects for BE, BTech, ME, MTech &PHD Students (09884848198 : S3 Infotech)
Dear Students,
Greetings from S3 INFOTECH (0988 48 48 198). We are doing Final year (IEEE & APPLICATION) projects in DOTNET, JAVA, MATLAB, ANDROID, VLSI, NS2, EMBEDDED SYSTEMS and POWER ELECTRONICS.
For B.E, M.E, B.Tech, M.Tech, MCA, M.Sc, & PHD Students.
We implement your own IEEE concepts also in ALL Technologies. We are giving support for Journal Arrangement & Publication also.
Send your IEEE base paper to yes3info@gmail.com (or) info@s3computers.com.
To Register your project: www.s3computers.com
We are providing Projects in
• DOT NET
• JAVA / J2EE / J2ME
• EMBEDDED & POWER ELECTRONICS
• MATLAB
• NS2
• VLSI
• NETWORKING
• HADOOP / Bigdata
• Android
• PHP
Vlsi IEEE 2014 titles 2014_2015_CSE/IT/ECE/EEE/ STUDENTS IN CHENNAI (S3 INFO...

Vlsi IEEE 2014 titles 2014_2015_CSE/IT/ECE/EEE/ STUDENTS IN CHENNAI (S3 INFO...S3 Infotech IEEE Projects
DOTNET/JAVA/MATLAB/VLSI/NS2/EMBEDDED IEEE 2014 PROJECTS FOR ME/BE/B.TECH STUDENTS. FINAL YEAR 2014 PROJECTS FOR CSE/IT/ECE/EEE/ STUDENTS IN CHENNAI (S3 INFOTECH : 09884848198).
Final year IEEE 2014 projects for BE, BTech, ME, MTech &PHD Students (09884848198 : S3 Infotech)
Dear Students,
Greetings from S3 INFOTECH (0988 48 48 198). We are doing Final year (IEEE & APPLICATION) projects in DOTNET, JAVA, MATLAB, ANDROID, VLSI, NS2, EMBEDDED SYSTEMS and POWER ELECTRONICS.
For B.E, M.E, B.Tech, M.Tech, MCA, M.Sc, & PHD Students.
We implement your own IEEE concepts also in ALL Technologies. We are giving support for Journal Arrangement & Publication also.
Send your IEEE base paper to yes3info@gmail.com (or) info@s3computers.com.
To Register your project: www.s3computers.com
We are providing Projects in
• DOT NET
• JAVA / J2EE / J2ME
• EMBEDDED & POWER ELECTRONICS
• MATLAB
• NS2
• VLSI
• NETWORKING
• HADOOP / Bigdata
• Android
• PHP
JAVA IEEE 2014 PROJECTS FOR ME/BE/B.TECH STUDENTS. FINAL YEAR 2014 PROJECTS F...

JAVA IEEE 2014 PROJECTS FOR ME/BE/B.TECH STUDENTS. FINAL YEAR 2014 PROJECTS F...S3 Infotech IEEE Projects
Mais de S3 Infotech IEEE Projects (18)
Power electronics ieee 2015 2016 projects list-vel

Power electronics ieee 2015 2016 projects list-vel
Dotnet ieee 2014 BE, B.Tech(cse,IT)-fully completed title list(v)

Dotnet ieee 2014 BE, B.Tech(cse,IT)-fully completed title list(v)
Power elec titles 2014_2015_S3 Infotech: 09884848198 chennai

Power elec titles 2014_2015_S3 Infotech: 09884848198 chennai
Vlsi IEEE 2014 titles 2014_2015_CSE/IT/ECE/EEE/ STUDENTS IN CHENNAI (S3 INFO...

Vlsi IEEE 2014 titles 2014_2015_CSE/IT/ECE/EEE/ STUDENTS IN CHENNAI (S3 INFO...
JAVA IEEE 2014 PROJECTS FOR ME/BE/B.TECH STUDENTS. FINAL YEAR 2014 PROJECTS F...

JAVA IEEE 2014 PROJECTS FOR ME/BE/B.TECH STUDENTS. FINAL YEAR 2014 PROJECTS F...
Ns2 2015 2016 ieee project list-(v)_with abstract(S3 Infotech:9884848198)
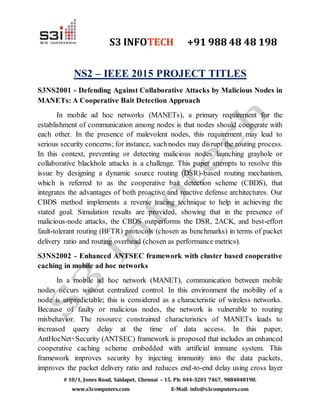
- 1. S3 INFOTECH +91 988 48 48 198 # 10/1, Jones Road, Saidapet, Chennai – 15. Ph: 044-3201 7467, 9884848198. www.s3computers.com E-Mail: info@s3computers.com NS2 – IEEE 2015 PROJECT TITLES S3NS2001 - Defending Against Collaborative Attacks by Malicious Nodes in MANETs: A Cooperative Bait Detection Approach In mobile ad hoc networks (MANETs), a primary requirement for the establishment of communication among nodes is that nodes should cooperate with each other. In the presence of malevolent nodes, this requirement may lead to serious security concerns; for instance, suchnodes may disrupt the routing process. In this context, preventing or detecting malicious nodes launching grayhole or collaborative blackhole attacks is a challenge. This paper attempts to resolve this issue by designing a dynamic source routing (DSR)-based routing mechanism, which is referred to as the cooperative bait detection scheme (CBDS), that integrates the advantages of both proactive and reactive defense architectures. Our CBDS method implements a reverse tracing technique to help in achieving the stated goal. Simulation results are provided, showing that in the presence of malicious-node attacks, the CBDS outperforms the DSR, 2ACK, and best-effort fault-tolerant routing (BFTR) protocols (chosen as benchmarks) in terms of packet delivery ratio and routing overhead (chosen as performance metrics). S3NS2002 - Enhanced ANTSEC framework with cluster based cooperative caching in mobile ad hoc networks In a mobile ad hoc network (MANET), communication between mobile nodes occurs without centralized control. In this environment the mobility of a node is unpredictable; this is considered as a characteristic of wireless networks. Because of faulty or malicious nodes, the network is vulnerable to routing misbehavior. The resource constrained characteristics of MANETs leads to increased query delay at the time of data access. In this paper, AntHocNet+Security (ANTSEC) framework is proposed that includes an enhanced cooperative caching scheme embedded with artificial immune system. This framework improves security by injecting immunity into the data packets, improves the packet delivery ratio and reduces end-to-end delay using cross layer
- 2. S3 INFOTECH +91 988 48 48 198 # 10/1, Jones Road, Saidapet, Chennai – 15. Ph: 044-3201 7467, 9884848198. www.s3computers.com E-Mail: info@s3computers.com design. The issues of node failure and node malfunction are addressed in the cache management. S3NS2003 - Experimental Assessment of ABNO-Driven Multicast Connectivity in Flexgrid Networks The increasing demand of internet services is pushing cloud services providers to increase the capacity of their data centers (DC) and create DC federations, where two or more cloud providers interconnect their infrastructures. As a result of the huge capacity required for the inter-DC network, the flexgrid optical technology can be used. In such scenario, applications can run in DCs placed in geographically distant locations, and hence, multicast-based communication services among their components are required. In this paper, we study two different approaches to provide multicast services in multilayer scenarios assuming that the optical network is based on the flexgrid technology: 1) establishing a point-to-multipoint optical connection (light-tree) for each multicast request, and 2) using a multipurpose virtual network topology (VNT) to serve both unicast and multicast connectivity requests. When that VNT is not able to serve an incoming request as a result of lack of capacity, it is reconfigured to add more resources. A control plane architecture based on the applications-based network operations (ABNO) one, currently being standardized by the IETF, is presented; workflows are proposed and PCEP extensions are studied for the considered approaches. The experimental validation is carried-out on a testbed setup connecting Telefonica, CNIT, and UPC premises. S3NS2004 - Game Theoretic Max-logit Learning Approaches for Joint Base Station Selection and Resource Allocation in Heterogeneous Networks This paper investigates the problem of joint base station selection and resource allocation in an orthogonal frequency division multiple access (OFDMA) heterogeneous cellular network. The original throughput maximization problem is NP-hard and we propose solving it by using game theoretic stochastic learning approaches. To this end, we first transform the original problem into a tractable form, which has a weighted utility function. Then we prove that an exact potential game applies and it exists the best Nash equilibria which is a near optimal solution
- 3. S3 INFOTECH +91 988 48 48 198 # 10/1, Jones Road, Saidapet, Chennai – 15. Ph: 044-3201 7467, 9884848198. www.s3computers.com E-Mail: info@s3computers.com of the original problem when an efficient solution method of the weights is employed. To obtain the optimal solution, we redesign the utility function by leveraging a state space to formulate the original problem into an ordinal state based potential game, which is proved that it exists a recurrent state equilibrium point that maximizes system throughput. Furthermore, we propose two different variants of Max-logit learning algorithm based on these two games respectively: one is a simultaneous learning algorithm with less information exchange, which achieves the best Nash equilibrium point of the exact potential game and the other is an efficient learning algorithm for the ordinal state based potential game, which can converge to the global optimization solution. Finally, numerical results are given to validate those theoretical findings. S3NS2005- A Scalable, Low-Latency, High-Throughput, Optical Interconnect Architecture Based on Arrayed Waveguide Grating Routers This paper proposes, simulates, and experimentally demonstrates an optical interconnect architecture for large-scale computing systems. The proposed architecture, Hierarchical Lightwave Optical Interconnect Network (H-LION), leverages wavelength routing in arrayed waveguide grating routers (AWGRs), and computing nodes (or servers) with embedded routers and wavelength-specific optical I/Os. Within the racks and clusters, the interconnect topology is hierarchical all-to-all exploiting passive AWGRs. For the intercluster communication, the proposed architecture exploits a flat and distributed Thin-CLOS topology based on AWGR-based optical switches. H-LION can scale beyond 100 000 nodes while guaranteeing up to 1.83×saving in number of inter-rack cables, and up to 1.5×saving in number of inter-rack switches, when compared with a legacy three- tier Fat Tree network. Network simulation results show a system-wide network throughput reaching as high as 90% of the total possible capacity in case of synthetic traffic with uniform random distribution. Experiments show 97% intra cluster throughput for uniform random traffic, and error-free intercluster communication at 10 Gb/s. S3NS2006 - Analysis of system trustworthiness based on information flow noninterference theory
- 4. S3 INFOTECH +91 988 48 48 198 # 10/1, Jones Road, Saidapet, Chennai – 15. Ph: 044-3201 7467, 9884848198. www.s3computers.com E-Mail: info@s3computers.com The trustworthiness analysis and evaluation are the bases of the trust chain transfer. In this paper the formal method of trustworthiness analysis of a system based on the noninterference (NI) theory of the information flow is studied. Firstly, existing methods cannot analyze the impact of the system states on the trustworthiness of software during the process of trust chain transfer. To solve this problem, the impact of the system state on trustworthiness of software is investigated, the run-time mutual interference behavior of software entities is described and an interference model of the access control automaton of a system is established. Secondly, based on the intransitive noninterference (INI) theory, a formal analytic method of trustworthiness for trust chain transfer is proposed, providing a theoretical basis for the analysis of dynamic trustworthiness of software during the trust chain transfer process. Thirdly, a prototype system with dynamic trustworthiness on a platform with dual core architecture is constructed and a verification algorithm of the system trustworthiness is provided. Finally, the monitor hypothesis is extended to the dynamic monitor hypothesis, a theorem of static judgment rule of system trustworthiness is provided, which is useful to prove dynamic trustworthiness of a system at the beginning of system construction. Compared with previous work in this field, this research proposes not only a formal analytic method for the determination of system trustworthiness, but also a modeling method and an analysis algorithm that are feasible for practical implementation. S3NS2007- Mobile Sink based Adaptive Immune Energy-Efficient Clustering Protocol for Improving the Lifetime and Stability Period of Wireless Sensor Networks Energy hole problem is a critical issue for data gathering in Wireless Sensor Networks. Sensors near the static sink act as relays for far sensor and thus will deplete their energy very quickly, resulting energy holes in the sensor field. Exploiting the mobility of a sink has been widely accepted as an efficient way to alleviate this problem. However, determining an optimal moving trajectory for a mobile sink is an NP-hard problem. Thus, this paper proposed a Mobile Sink based adaptive Immune Energy-Efficient clustering Protocol (MSIEEP) to alleviate the energy holes. MSIEEP uses the Adaptive Immune Algorithm (AIA) to guide the
- 5. S3 INFOTECH +91 988 48 48 198 # 10/1, Jones Road, Saidapet, Chennai – 15. Ph: 044-3201 7467, 9884848198. www.s3computers.com E-Mail: info@s3computers.com mobile sink based on minimizing the total dissipated energy in communication and overhead control packets. Moreover, AIA is used to find the optimum number of Cluster Heads (CHs) to improve the lifetime and stability period of the network. The performance of MSIEEP is compared with the previously published protocols; namely LEACH, LEACHGA, A-LEACH, rendezvous and MIEEPB using Matlab. Simulation results show that MSIEEP is more reliable and energy efficient as compared to other protocols. Furthermore, it improves the lifetime, the stability and the instability periods over the previous protocols, because it always selects CHs from high energy nodes. Moreover, the mobile sink increases the ability of the proposed protocol to deliver packets to the destination. S3NS2008 - Joint Resource Allocation for Throughput Enhancement in Cognitive Radio Femto cell Networks In cognitive radio femto cell network (CRFN), secondary users (SUs) cooperatively sense a spectrum band to decide the presence of primary network. However, this sensing overhead generally degrades the throughput performance. The prior work, to resolve this problem, proposed algorithms either to decrease the time spent in sensing or to decrease the number of SUs participating in sensing. In this paper, we propose a joint resource allocation (RA) strategy considering the time and energy consumed for spectrum sensing to maximize the throughput while satisfying the target detection performance in CRFN. Furthermore, to reduce the resources used in spectrum sensing additionally, we also adopt the right censored order statistics based cooperative spectrum sensing scheme, which produces the criterion for deciding the set of reporting SUs. By so jointly designing the time and energy for sensing, the proposed joint RA scheme provides the improvement of spectral efficiency. Through simulation results, it is shown that the proposed joint RA scheme exhibits the enhanced performance over the conventional ones in terms of total throughput of secondary networks. S3NS2009 - A survey on the privacy-preserving data aggregation in wireless sensor networks Wireless sensor networks (WSNs) consist of a great deal of sensor nodes with limited power, computation, storage, sensing and communication capabilities.
- 6. S3 INFOTECH +91 988 48 48 198 # 10/1, Jones Road, Saidapet, Chennai – 15. Ph: 044-3201 7467, 9884848198. www.s3computers.com E-Mail: info@s3computers.com Data aggregation is a very important technique, which is designed to substantially reduce the communication overhead and energy expenditure of sensor node during the process of data collection in a WSNs. However, privacy-preservation is more challenging especially in data aggregation, where the aggregators need to perform some aggregation operations on sensing data it received. We present a state-of-the art survey of privacy-preserving data aggregation in WSNs. At first, we classify the existing privacy- preserving data aggregation schemes into different categories by the core privacy-preserving techniques used in each scheme. And then compare and contrast different algorithms on the basis of performance measures such as the privacy protection ability, communication consumption, power consumption and data accuracy etc. Furthermore, based on the existing work, we also discuss a number of open issues which may intrigue the interest of researchers for future work. S3NS20010 - Energy Detection Technique for Adaptive Spectrum Sensing The increasing scarcity in the available spectrum for wireless communication is one of the current bottlenecks impairing further deployment of services and coverage. The proper exploitation of white spaces in the radio spectrum requires fast, robust, and accurate methods for their detection. This paper proposes a new strategy to detect adaptively white spaces in the radio spectrum. Such strategy works in Cognitive Radio (CR) networks whose nodes perform spectrum sensing based on energy detection in a cooperative way or not. The main novelty of the proposal is the use of a cost-function that depends upon a single parameter which, by itself, contains the aggregate information about the presence or absence of primary users. The detection of white spaces based on this parameter is able to improve significantly the deflection coefficient associated with the detector, as compared to other state-of-the-art algorithms. In fact, simulation results show that the proposed algorithm outperforms by far other competing algorithms. For example, our proposal can yield a probability of miss-detection 20 times smaller than that of an optimal soft-combiner solution in a cooperative setup with a predefined probability of false alarm of 0.1.
