Protect Sensitive Consumer Data With Governance Across Devices and Clouds
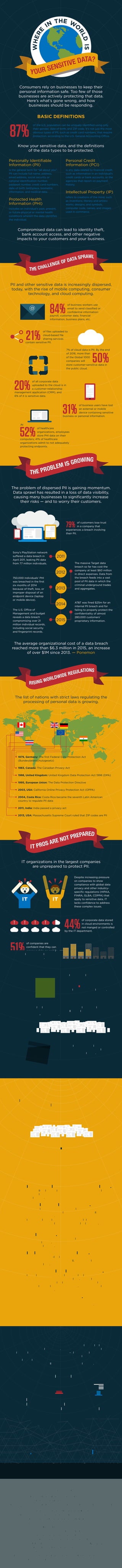
- 1. Consumers rely on businesses to keep their personal information safe. Too few of those businesses are actively protecting that data. Here’s what’s gone wrong, and how businesses should be responding. Know your sensitive data, and the definitions of the data types to be protected. Compromised data can lead to identity theft, bank account access, and other negative impacts to your customers and your business. PII and other sensitive data is increasingly dispersed, today, with the rise of mobile computing, consumer technology, and cloud computing. The average organizational cost of a data breach reached more than $6.3 million in 2015, an increase of over $1M since 2013. — Ponemon The problem of dispersed PII is gaining momentum. Data sprawl has resulted in a loss of data visibility, causing many businesses to significantly increase their risks — and to worry their customers. Personally Identifiable Information (PII) is the general term for “all about you”. PII can include full name, address, email address, social security or national identification number, passport number, credit card numbers, date of birth, birthplace, biometric information, and medical data. Protected Health Information (PHI) includes an individual’s past, present, or future physical or mental health conditions wherein the data identifies the individual. Personal Credit Information (PCI) is any data related to financial credit, such as information in an individual’s credit cards or bank accounts, or the agencies that report on payment history. Intellectual Property (IP) refers to creations of the mind, such as inventions; literary and artistic works; designs; and symbols, computer code, names, and images used in commerce. of business workers use email to send classified or confidential information: payroll, customer data, financial information, business plans, etc. 84% of files uploaded to cloud-based file sharing services contain sensitive PII. 21% of all corporate data uploaded to the cloud is in a customer-relationship management application (CRM), and 6% of it is sensitive data. 20% BASIC DEFINITIONS of healthcare organizations, employees store PHI data on their computers; 41% of healthcare organizations admit to not adequately protecting endpoints. 52% of business users have lost an external or mobile device containing sensitive business or personal information. 31% 50%of the Global 1000 companies will store customer-sensitive data in the public cloud. 7% of cloud data is PII. By the end of 2016, more than @ At WHERE IN THE W O RLDIS YOUR SENSITIVE DATA? THE CHALLENGE OF DATA SPRAWL THE PROBLEM IS GROWING RISING WORLDWIDE REGULATIONS WHAT YOU CAN DO HOW DRUVA CAN HELP IT PROS ARE NOT PREPARED Sony’s PlayStation network suffered a data breach in April 2011, leaking PII data from 77 million individuals. The massive Target data breach so far has cost the company at least $60 million in direct expenses. Data from the breach feeds into a vast pool of PII data in which the criminal underground trades and aggregates. AT&T was fined $25m for an internal PII breach and for failing to properly protect the confidentiality of almost 280,000 customers’ proprietary information. 750,000 individuals’ PHI was breached in the first six months of 2014 because of theft, loss, or improper disposal of an endpoint device (laptop or mobile device). The U.S. Office of Management and budget reveals a data breach compromising over 21 million individual records, including social security and fingerprint records. of customers lose trust in a company that experiences a breach involving their PII. 79% 2011 2012 2013 2014 2015 1 2 3 4 5 6 of the U.S. population can be uniquely identified using only their gender, date of birth, and ZIP code. It’s not just the most obvious types of PII, such as credit card numbers, that require protection, according to the U.S. General Accounting Office.87% 1979, Germany: The first Federal Data Protection Act (Bundesdatenschutzgesetz) 1983, Canada: The Canadian Privacy Act 1988, United Kingdom: United Kingdom Data Protection Act 1998 (DPA) 1995, European Union: The Data Protection Directive 2003, USA: California Online Privacy Protection Act (OPPA) 2004, Costa Rica: Costa Rica became the seventh Latin American country to regulate PII data 2011, India: India passed a privacy act 2013, USA: Massachusetts Supreme Court ruled that ZIP codes are PII The list of nations with strict laws regulating the processing of personal data is growing. IT organizations in the largest companies are unprepared to protect PII. Identify and Take Action Against Data Risks Across Mobile and Distributed Data Businesses can take steps to get ahead of the risks and to reduce their exposure: Druva's converged data protection brings datacenter class availability and governance to the mobile workforce. Druva’s inSync proactive compliance solution delivers new, enhanced governance-related capabilities that equip organizations to stay on top of their data, where it’s located and how it’s handled, while at the same time ensuring the integrity of that data if its authenticity is called into question during litigation. The new enhanced data governance capabilities include: Learn more about Druva’s proactive compliance capabilities at druva.com/proactivecompliance Despite increasing pressure on companies to show compliance with global data privacy and other industry- specific regulations (HIPAA, FINRA, GLBA, COPPA) that apply to sensitive data, IT lacks confidence to address these complex issues. Centralized visibility Automated data monitoring for compliance Data governance for Legal and Compliance http://resources.ipswitchft.com/rs/ipswitch2/images/eBook%20-%20Are%20employees%20putting%20your%20company%27s%20data% 20at%20risk.pdf https://www.netskope.com/blog/netskope-cloud-report-look-compromised-credentials - Gartner, June 2015 https://www.skyhighnetworks.com/cloud-university/is-the-cloud-secure/Brief Stolen and Lost devices are Putting Personal healthcare information at Risk: It’s time For Healthcare ciSos to close the Faucet of Data loss From endpoints - Forrester, 2015 http://www.darkreading.com/attacks-and-breaches/sony-data-breach-cleanup-to-cost-$171-million/d/d-id/1097898? http://www.oracle.com/us/corporate/profit/big-ideas/010312-data-1917731.html http://www.ponemon.org/blog/ponemon-institute-releases-2014-cost-of-data-breach-global-analysis http://www.csrps.com/faqs-0 http://www.visionpayments.com/faq/personally-identifiable-information/ http://www.hhs.gov/ocr/privacy/hipaa/administrative/breachnotificationrule/breachtool.html http://www.tomsguide.com/us/target-neiman-marcus-data-breach-faq,news-18199.html http://www.eweek.com/security/personal-information-on-enterprise-devices-carries-security-risks.html http://www.dhs.gov/sites/default/files/publications/privacy/Guidance/handbookforsafeguardingsensitivePII_march_2012_webversion.pdf http://www.informationisbeautiful.net/visualizations/worlds-biggest-data-breaches-hacks http://www.bbc.com/news/business-25525621 http://blogs.wsj.com/cio/2015/07/10/the-morning-download-outdated-tech-infrastructure-led-to-massive-opm-breach/ Verizon 2015 Data Breach Investigations Report INTELLECTUAL PROPERTY THEFT Sources: of corporate data stored in cloud environments is not manged or controlled by the IT department. 44% of legal preservation requests now included mobile device data; an often manually complicated and error-prone process.26% Identify and locate sensitive personal data. such as PII, PHI, and PCI to ensure your enterprise is compliant with regulations and that sensitive data is not somewhere it should not be. Centralize visibility of your data. Gain visibility of important and anomalous user data and events by bringing endpoints and cloud data into your overall data governance initiatives. A unified view of data across dispersed locations helps the IT department more easily locate and govern data by source, compliance risk type, risk level, and user. Find out who can access customer and employee data. Use federated search across business locations to identify and thus control access. Search the extended network for data, owners, and locations. Implement secure technologies. Demand data center-level performance even when the data you seek is outside the corporate firewall. Ensure mobile devices adhere to policies. Retain data only as long as it’s needed. IT should team up with compliance and legal departments to better understand data retention policies. Keep only what you need to keep based on legal requirements, and purge old data that's no longer relevant to the business. The more you hold, the more risk of exposure. Automate risk identification. Pay attention to business processes: understand, identify, and act on data risks across the dispersed data environment. In 2013, Barclays Bank was fined after it was discovered the bank failed to keep critical records. $3.75M of companies are confident that they can preserve data on mobile devices for litigation, regulatory, or investigative requirements. 51% Insider and privilege misuse was responsible for 12% of IP theft.12%
