Public Key Cryptography: A Practical Approach
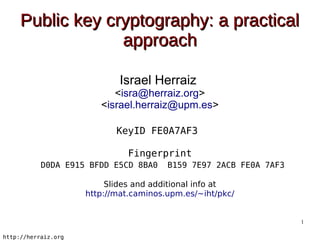
- 1. Public key cryptography: a practical approach Israel Herraiz <isra@herraiz.org> <israel.herraiz@upm.es> KeyID FE0A7AF3 Fingerprint D0DA E915 BFDD E5CD 8BA0 B159 7E97 2ACB FE0A 7AF3 Slides and additional info at http://mat.caminos.upm.es/~iht/pkc/ 1 http://herraiz.org
- 2. Privacy in electronic communicatios Can we ensure privacy in electronic communications? 2 http://herraiz.org
- 3. Reaching Google 1 10.8.0.1 (10.8.0.1) 2 192.168.1.1 (192.168.1.1) 3 62.81.125.179.static.user.ono.com (62.81.125.179) 4 10.115.49.217 (10.115.49.217) 5 10.127.151.49 (10.127.151.49) 6 10.127.10.137 (10.127.10.137) 7 10.127.10.133 (10.127.10.133) 8 10.127.3.82 (10.127.3.82) 9 213.242.71.21 (213.242.71.21) 10 ae-5-5.ebr1.Paris1.Level3.net (4.69.141.42) 11 ae-45-45.ebr1.London1.Level3.net (4.69.143.101) 12 ae-1-51.edge3.London1.Level3.net (4.69.139.73) 13 unknown.Level3.net (212.113.15.186) 14 209.85.255.78 (209.85.255.78) 15 66.249.95.173 (66.249.95.173) 16 216.239.49.45 (216.239.49.45) 17 * * * 18 ww-in-f147.1e100.net (209.85.229.147) 3 http://herraiz.org
- 4. Reaching Google 1 10.8.0.1 (10.8.0.1) 2 192.168.1.1 (192.168.1.1) Getafe 3 62.81.125.179.static.user.ono.com (62.81.125.179) 4 10.115.49.217 (10.115.49.217) 5 10.127.151.49 (10.127.151.49) Barcelona 6 10.127.10.137 (10.127.10.137) 7 10.127.10.133 (10.127.10.133) 8 10.127.3.82 (10.127.3.82) 9 213.242.71.21 (213.242.71.21) Minneapolis 10 ae-5-5.ebr1.Paris1.Level3.net (4.69.141.42) Paris 11 ae-45-45.ebr1.London1.Level3.net (4.69.143.101) 12 ae-1-51.edge3.London1.Level3.net (4.69.139.73) London 13 unknown.Level3.net (212.113.15.186) 14 209.85.255.78 (209.85.255.78) Atlanta 15 66.249.95.173 (66.249.95.173) New York 16 216.239.49.45 (216.239.49.45) Los Angeles 17 * * * 18 ww-in-f147.1e100.net (209.85.229.147) Atlanta 4 http://herraiz.org
- 5. Hops while attempting to reach Google 5 http://herraiz.org
- 6. Is it that bad? What kind of private Information can be captured? 6 http://herraiz.org
- 7. Non-cyphered information ● Geolocalization ● Using your IP address ● Web browser and operating system ● Any info written in a form ● Including passwords ● Cookies ● Have a look and take care – http://www.youtube.com/watch?v=yyLdxO6xvh8 – http://www.youtube.com/watch?v=1FgKL2ywrX0 7 http://herraiz.org
- 8. Is it important? ● Strong PK crypto illegal in France up to 2004 ● PK implementations in software considered weapons in the US ● Software export restrictions in EU and US http://en.wikipedia.org/wiki/Cryptography_law http://en.wikipedia.org/wiki/Key_disclosure_law http://en.wikipedia.org/wiki/Phil_Zimmermann http://en.wikipedia.org/wiki/Export_of_cryptography_in_the_United_States#History 8 http://herraiz.org
- 9. Solution Enforce cyphering using public key cryptography 9 http://herraiz.org
- 10. Cryptography ● Traditionally, cyphering was done using a password and an algorithm ● Symmetric approach ● Password shared by both peers ● Public key cryptography ● Insecure channel ● Private and secure communication without any previous physical contact 10 http://herraiz.org
- 11. Public key cryptography (PKP) Pub Pri Pub Pri 11 http://herraiz.org
- 12. Public key cryptography Pub Pri Pub Pri Keyserver Pub Pub 12 http://herraiz.org
- 13. Criptografía de clave pública Hi there! Pub Pri Pub Pri Keyserver Pub Pub 13 http://herraiz.org
- 14. Public key cryptography Pub 0F231A5 Pub Pri Pub Pri Keyserver Pub Pub 14 http://herraiz.org
- 15. Public key cryptography Pub 0F231A5 Pub Pri Pub Pri Keyserver Pub Pub 15 http://herraiz.org
- 16. Public key cryptography Hi there! Pub Pri Pub Pri Keyserver Pub Pub 16 http://herraiz.org
- 17. How does it work? ● PKP Algorithms ● Prime number factorization ● From a mathematical point of view, all messages can be decrypted ● From a computational point of view, decrypting a message without the private key takes too long – Key length is a crucial property 17 http://herraiz.org
- 18. Public key sample -----BEGIN PGP PUBLIC KEY BLOCK----- Version: GnuPG v2.0.19 (GNU/Linux) JeP5F/eRS9G8EE1fObRRW6mRf+bGSeluFEMiOi3UB/5P0GBx8iM0QIjezR0R+2n8 bMjuJmWHTjvEeplnx9iual4J4BT/9FznFs7o4tFVVfYBacFrhWjQyAf2xoP3gyn3 5OlV55VHVB+oidXUVNSNHZbXwrd1sH42x7x8o17PDFJrWjiq4kAb2EfSOIuSS6na K9Y06bqh3yRbVtRdZOuCLcY8QJwt/mx//uQqG6NuSvYhx1QyC6g==XuDESOIuSSa mQINBEtUTeQBEACejdGQhscmsDXM7xG2/ZYFpMQg/GmPlJ85uJJUkLr2T+5Rw8Xv VfZjNZkMwsq94BGFrBxu477tKhQ5wiUBBz/jJ01a39Wrazgp21fvEon2T0Vay45t 2BYbU4AF815UL6o74YlW5SLdAofwylZS8pX4CKjGAB0T+fDiwkAepQl45nzX0ulv -----END PGP PUBLIC KEY BLOCK----- 18 http://herraiz.org
- 19. Private key sample -----BEGIN PGP PRIVATE KEY BLOCK----- Version: GnuPG v2.0.19 (GNU/Linux) mQINBEtUTeQBEACejdGQhscmsDXM7xG2/ZYFpMQg/GmPlJ85uJJUkLr2T+5Rw8Xv JeP5F/eRS9G8EE1fObRRW6mRf+bGSeluFEMiOi3UB/5P0GBx8iM0QIjezR0R+2n8 VfZjNZkMwsq94BGFrBxu477tKhQ5wiUBBz/jJ01a39Wrazgp21fvEon2T0Vay45t 2BYbU4AF815UL6o74YlW5SLdAofwylZS8pX4CKjGAB0T+fDiwkAepQl45nzX0ulv bMjuJmWHTjvEeplnx9iual4J4BT/9FznFs7o4tFVVfYBacFrhWjQyAf2xoP3gyn3 5OlV55VHVB+oidXUVNSNHZbXwrd1sH42x7x8o17PDFJrWjiq4kAb2EfSOIuSS6na K9Y06bqh3yRbVtRdZOuCLcY8QJwt/mx//uQqG6NuSvYhx1QyC6g==XuDESOIuSSa -----END PGP PRIVATE KEY BLOCK----- 19 http://herraiz.org
- 20. Keyservers ● Internet hosts that contain public keys ● Federated services ● All servers contain all the public keys in the world ● Public keyserver in Spain thanks to RedIRIS ● URL: pgp.rediris.es 20 http://herraiz.org
- 21. Message signing Hi there! Pub Pri Pub Pri Keyserver Pub Pub 21 http://herraiz.org
- 22. Message signing Created with the private key Hi there! Pub Pri Pub Pri Keyserver Pub Pub 22 http://herraiz.org
- 23. Message signing Hi there! Pub Pri Pub Pri Keyserver Pub Pub 23 http://herraiz.org
- 24. Signing and encrypting Hi there! Pub Pri Pub Pri Keyserver Pub Pub 24 http://herraiz.org
- 25. Signing and encrypting Pub FAD43A Pub Pri Pub Pri Keyserver Pub Pub 25 http://herraiz.org
- 26. Signing and encrypting Pub FAD43A Pub Pri Pub Pri Keyserver Pub Pub 26 http://herraiz.org
- 27. Signing and encrypting Hi there! Pub Pri Pub Pri Keyserver Pub Pub 27 http://herraiz.org
- 28. Signing and encrypting Hi there! Pub Pri Pub Pri Keyserver Pub Pub 28 http://herraiz.org
- 29. Identity certification How do you know that public keys belong to their legitimate owners? Public key Can we ensure that the Barack Obama key does belong to Barack Obama? 29 http://herraiz.org
- 30. Identity certification Certificate Authorities Trust chain 30 http://herraiz.org
- 31. Public key signing ● Public keys are plain text documents that can be cryptographically signed ● Mutual public signing adds identity certification to PKP schemes 31 http://herraiz.org
- 32. Public key signing Barack Obama Pub Pri Pub Pri Keyserver Pub Pub 32 http://herraiz.org
- 33. Public key signing Barack Obama Key FE0A7AF2 Name Barack Obama Fingerprint D0DA E915 BFDD E5CD 8BA0 B159 7E97 2ACB FE0A 7AF2 Pub Pri Pub Pri Keyserver Pub Pub 33 http://herraiz.org
- 34. Public key signing Barack Obama Key FE0A7AF2 Name Barack Obama Fingerprint D0DA E915 BFDD E5CD 8BA0 B159 7E97 2ACB FE0A 7AF2 Pub Pri Pub Pri Keyserver Pub Pub 34 http://herraiz.org
- 35. Public key signing Show me your passport Barack Obama Key FE0A7AF2 Name Barack Obama Fingerprint D0DA E915 BFDD E5CD 8BA0 B159 7E97 2ACB FE0A 7AF2 Pub Pri Pub Pri Keyserver Pub Pub 35 http://herraiz.org
- 36. Public key signing Show me your passport Barack Obama Key FE0A7AF2 Name Barack Obama Fingerprint Passport D0DA E915 BFDD E5CD 8BA0 Barack B159 7E97 2ACB FE0A 7AF2 Obama Pub Pri Pub Pri Keyserver Pub Pub 36 http://herraiz.org
- 37. Public key signing Pub Key FE0A7AF2 Barack Obama Name Barack Obama D0DA E915 BFDD E5CD 8BA0 Fingerprint B159 7E97 2ACB FE0A 7AF2 D0DA E915 BFDD E5CD 8BA0 B159 7E97 2ACB FE0A 7AF2 Download key FE0A7AF2 Pub Pri Keyserver Pub Pub 37 http://herraiz.org
- 38. Public key signing Pub Key FE0A7AF2 Barack Obama Name Barack Obama D0DA E915 BFDD E5CD 8BA0 Fingerprint B159 7E97 2ACB FE0A 7AF2 D0DA E915 BFDD E5CD 8BA0 B159 7E97 2ACB FE0A 7AF2 Pub Pri Keyserver Pub Pub 38 http://herraiz.org
- 39. Public key signing Pub Key FE0A7AF2 Barack Obama Name Barack Obama D0DA E915 BFDD E5CD 8BA0 Fingerprint B159 7E97 2ACB FE0A 7AF2 D0DA E915 BFDD E5CD 8BA0 B159 7E97 2ACB FE0A 7AF2 Pub Pri Keyserver Pub Pub 39 http://herraiz.org
- 40. Public key signing Barack Obama Key signing is often mutual Pub Pri Pub Pri Keyserver Pub Pub 40 http://herraiz.org
- 41. Public key signing Barack Obama Trust chain Pub Pub Is he Barack Pub Obama? 41 http://herraiz.org
- 42. Signing party 42 http://herraiz.org
- 43. Take away PK Cryptog. Each user creates Secure comms. a public-private through key pair insec. channels Trust chain Keyservers Identity cert. contain every through key in the world public key signing 43 http://herraiz.org
