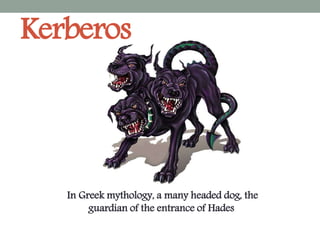
Kerberos-PKI-Federated identity
- 1. Kerberos In Greek mythology, a many headed dog, the guardian of the entrance of Hades
- 2. Example of Kerberos Idea A C B Now I can deal with A by using our shared key
- 3. • Kerberos is a protocol for authenticating service requests between trusted hosts across an untrusted network, such as the internet. • Kerberos is built in to all major operating systems, including Microsoft Windows, Apple OS X, FreeBSD and Linux.
- 4. Kerberos Protocol XYZService KeyDistributionCenter(KDC) 1.Generate Session Key 2. Create XYZ credential ticket a. Encrypt with XYZ service key (Password). b. Create message(Current date time, Session key). 3. Create User Response a. Create message(Current date time, Session XYZ credential ticket ) b. Encrypt with user key (Password) 1.Decrypt the response using user key(password). 2.save the session key to be used for any communication to XYZ service . 3.Pass the service credential ticket to the XYZ service
- 5. KeyDistributionCenter(KDC) XYZservice Kerberos Protocol 1. Decrypt the response using XYZ service key (password). 2. Save the session key to be used for any communication to the user. 3. Send successful response encrypted with the session key .
- 6. 1. First service access is Ticket Granting Service (TGS) service to get Ticket Granting Ticket (TGT) a. Single sign on b. Allow user to use biometric, finger print and smart card . 2. If we considered that user is delegated by the KDC to XYZ service, with the same concept the user can delegate XYZ service to deal with another service on behalf of him. Kerberos Protocol KeyDistribution Center(KDC) Authentication service(AS) Ticket Granting Service (TGS)
- 7. Public Key Infrastructure (PKI) Binds public keys to entities , enables other entities to verify public key bindings, Provides services for management of keys in a distributed system Goals: protect and distribute information that is needed in a widely distributed environment, where the users, resources and stake- holders may all be in different places at different times
- 8. PKI-Public Key Infrastructure-PKI 1.How can we transfer public key /File Format?
- 9. PKI-Public Key Infrastructure-PKI 2. Who Create/Generate this Certificate 1.How can we transfer public key /File Format? 1. How can you trust this certificate ? 2.Does this site really belong to ..? A trust B B trust C Then A will trust C Certificateauthority(CA) Trust TrustedCA Trust Public
- 10. Certificateauthority(CA) TrustedCA PKI-Public Key Infrastructure-PKI Public key 3.Does this certificate really generated by a Trusted CA? Digital signature(DS)
- 11. PKI-Public Key Infrastructure-PKI Certificateauthority(CA) TrustedCA Issue Policy and Methods Distribution policy and Method Certificate Backup
- 12. How to know google chrome certificates
- 14. This page will appear it has all certificates classified Choose any tap you want to see
- 15. Here I choose the first certificate, and what appeared is the certificate itself. It shows the what it is used for, the publisher and dates.
- 16. Alternatives Web of trust An alternative approach to the problem of public authentication of public key information is the web-of-trust scheme, which uses self-signed certificates and a trusted third party for those certificates. Examples : oPGP (Pretty Good Privacy) oOpenPGP
- 17. The web of trust concept was first put by PGP creator Phil Zimmermann in 1992 for PGP PGP company owned the rights to the original PGP encryption software. released in 1991 to ensure the security of files that were posted on internet From 1997 until 2010, the software changed several times until it was Bought by Symantec Corp., who continues to develop the PGP. PGP encryption uses a combination of encryption methodologies such as hashing, data compression, symmetric-key cryptography and public key cryptography. PGP allow the use of e-mail digital signatures for self- publication of public key information, this what make it easy. Zimmerman soon began work on an openPGP (open- source version of PGP) encryption that uses encryption algorithms that had no licensing issues.
- 18. Alternatives Simple Public Key Infrastructure public key certificate format, associated signature and key acquisition protocols are to be simple to understand, implement, and use. The resulting formats and protocols are to be known as the Simple Public Key Infrastructure, or SPKI. The SPKI is intended to provide mechanisms to support security in a wide range of internet applications as electronic mail and WWW documents, payment protocols, and any other application which will require the use of public key certificates.
- 19. What is Digital Identity ? Digital Identity : The electronic representation of an entity within a domain of application. Entity : A person, a group of persons, an organization or even a device that is capable of doing a transaction. Domain Of Application : The area of application where a digital identity has its validity Identifiers :A digital identity is composed of identifiers or attributes. Examples are Date Of Birth, ID. Credentials : It is anything a user can possess. Examples are a password, answer to a question, his eye or his voice
- 20. Federated identity management using the same set of standards across different organizations to manage users identity. With the increased integration of Internet in our life users, suppliers, retailers all are accessing services of many organizations to increase their business and get the best of what is available, but one organization does not trust the identities of another organization. So the user ends up making several user-IDs and passwords. This is very inefficient, costly and not at all user friendly. FIM provides standards that help the identities to cross organizational boundaries and to be shared by many organizations. FIM allows the subscriber to use the same identity to access networks of different organizations. Some of the first adopters of FIM were Boeing, General Motors and Nokia
- 22. Identity Management Evolution : Identity Management (IM) refers to procedure of handling the lifecycle of a digital identity its creation, maintenance and deleting a digital identity. IM has to also deal with authentication procedure and access control policy. Identity Provider (IDP) is a service or an organization that is responsible for authentication of user. Single Sign On (SSO) is a process where user gains access to several services after successful authentication .
- 23. FIM challenges Although progress have been made in FIM but there are some challenges that are faced by FIM. They are as follows : Identity theft : the theft of an identity represents one of the main issues as it remains undetected till the damage has been done. In most of the cases identity theft does not occur at the Identity Provider. It mostly occurs on the users end.
- 24. FIM challenges Privacy guarantee and legal compliance : In some countries there are laws to protect users personal information against bad use. The current FIM have weak definitions in how a user should protect is personal information. A standard is proposed by W3C for websites to tell their practices of personal information collection, use and distribution. These policies should be read by the web browser or the user and must be accepted.
- 25. Peer To Peer (P2P) application : Support Use of P2P applications has increased very fast. FIM use in P2P environment will provide more security but FIM is based on client/server model. *note: client/server model which the client makes a service request and the server fulfills the request, the P2P network model allows each node to function as both a client and server.
- 26. Thank you for your attention !! This presentation by : Wafa Al-salman Sara Al-sughaeir