Internet of Things & Smart Cities Intro
•
0 gostou•1,717 visualizações
Slides from the DISHA session at Emertxe hosted by Dr. C.P. Ravikumar(Director, Technical Talent Development, Texas Instruments, India)
Denunciar
Compartilhar
Denunciar
Compartilhar
Baixar para ler offline
Recomendados
Hardware Challenges for the IoT

The document discusses hardware challenges for Internet of Things (IoT) applications. Some key challenges discussed include choosing the right communication protocol (WiFi vs RF), power consumption, security, and resources like CPU and memory. While WiFi provides direct internet connectivity, RF technologies have advantages in terms of range, price, and power efficiency. The choice depends on the specific use case. IoT gateways can help address challenges by providing connectivity between different protocols and enhancing security. Standardization may help but there is no single solution - approaches need to be use case specific. The document promotes the Flyport prototyping platform as a solution and offers a demonstration of its capabilities.
Internet of Things (IOT) - Demo - Part I

IOT is all about connecting anytime, anything, anywhere. In this bigger concept, embedded devices interfacing with heterogeneous equipment with help of sensor interface plays a key role. This is a demo talks about two interesting use cases built using Emertxe's PIC platform.
Building careers in embedded

Embedded systems domain offers great career opportunity for fresh engineers. Team Emertxe had a seminar session at MVJ college of engineering, Bangalore by sharing details about the same topic.
Building careers in IoT

IoT is definitely getting popular day-by-day where no company can afford to ignore. Benefits offered by IoT for both B2B and B2C companies are obvious. For many traditional businesses which didn’t come into the digital world (PC era) are now leapfrogging directly into cloud centric IoT era. IoT based based solutions being seriously considered and deployed in traditional industries like chemical manufacturing, water treatment plants, leather manufacturing etc... As time passes, more industries and business are flocking into IoT. These businesses stand to gain benefits in terms of improved operational efficiency, better productivity and better manpower management. Similar advantages are clearly seen in B2C industries as well. An average consumer benefiting by interacting with devices that are getting smart - Smart Home, Smart City etc..Irrespective of that type of Business (B2B or B2C), it is imperative that their existing manpower and new recruits (freshers) should be skilled in the IoT related technologies to harness benefits in a tangible fashion.
Addressing the Challenges of IoT Design

The document discusses the challenges of designing Internet of Things (IoT) devices. IoT designs combine multiple complex design domains including sensors, analog and digital signal processing, radio connectivity, and interfaces to the internet. Integrating all these elements together into a single IoT product places a high demand on engineering teams. The diagram shows the typical components of an IoT device that must be integrated, including sensors, analog and digital conversion/processing, a microcontroller, radio connectivity, and links to the internet and cloud services.
Tracing the evolution - Open source & Embedded systems

Open Source is a very powerful weapon using which products can be built from the scratch. Rich tool chain, Cross platform support, Debugging facilities, Project management tools etc. makes it all the more suitable for Embedded systems. This presentation traces the evolution of open source and points how products can be built from the scratch using Open Source.
IoT : Whats in it for me? 

The Internet-Of-Things (IoT) is no longer a hype, but a reality. Connecting ANY devices, ANY place, ANY thing will transform the way we live. However from an engineers point of view how can he gain benefit from this? Here are some of the key technology trends that will play an important role.
Introduction to Embedded System

An introductory presentation to Embedded Systems. Ideal for beginners to get started with Embedded fundamentals.
Recomendados
Hardware Challenges for the IoT

The document discusses hardware challenges for Internet of Things (IoT) applications. Some key challenges discussed include choosing the right communication protocol (WiFi vs RF), power consumption, security, and resources like CPU and memory. While WiFi provides direct internet connectivity, RF technologies have advantages in terms of range, price, and power efficiency. The choice depends on the specific use case. IoT gateways can help address challenges by providing connectivity between different protocols and enhancing security. Standardization may help but there is no single solution - approaches need to be use case specific. The document promotes the Flyport prototyping platform as a solution and offers a demonstration of its capabilities.
Internet of Things (IOT) - Demo - Part I

IOT is all about connecting anytime, anything, anywhere. In this bigger concept, embedded devices interfacing with heterogeneous equipment with help of sensor interface plays a key role. This is a demo talks about two interesting use cases built using Emertxe's PIC platform.
Building careers in embedded

Embedded systems domain offers great career opportunity for fresh engineers. Team Emertxe had a seminar session at MVJ college of engineering, Bangalore by sharing details about the same topic.
Building careers in IoT

IoT is definitely getting popular day-by-day where no company can afford to ignore. Benefits offered by IoT for both B2B and B2C companies are obvious. For many traditional businesses which didn’t come into the digital world (PC era) are now leapfrogging directly into cloud centric IoT era. IoT based based solutions being seriously considered and deployed in traditional industries like chemical manufacturing, water treatment plants, leather manufacturing etc... As time passes, more industries and business are flocking into IoT. These businesses stand to gain benefits in terms of improved operational efficiency, better productivity and better manpower management. Similar advantages are clearly seen in B2C industries as well. An average consumer benefiting by interacting with devices that are getting smart - Smart Home, Smart City etc..Irrespective of that type of Business (B2B or B2C), it is imperative that their existing manpower and new recruits (freshers) should be skilled in the IoT related technologies to harness benefits in a tangible fashion.
Addressing the Challenges of IoT Design

The document discusses the challenges of designing Internet of Things (IoT) devices. IoT designs combine multiple complex design domains including sensors, analog and digital signal processing, radio connectivity, and interfaces to the internet. Integrating all these elements together into a single IoT product places a high demand on engineering teams. The diagram shows the typical components of an IoT device that must be integrated, including sensors, analog and digital conversion/processing, a microcontroller, radio connectivity, and links to the internet and cloud services.
Tracing the evolution - Open source & Embedded systems

Open Source is a very powerful weapon using which products can be built from the scratch. Rich tool chain, Cross platform support, Debugging facilities, Project management tools etc. makes it all the more suitable for Embedded systems. This presentation traces the evolution of open source and points how products can be built from the scratch using Open Source.
IoT : Whats in it for me? 

The Internet-Of-Things (IoT) is no longer a hype, but a reality. Connecting ANY devices, ANY place, ANY thing will transform the way we live. However from an engineers point of view how can he gain benefit from this? Here are some of the key technology trends that will play an important role.
Introduction to Embedded System

An introductory presentation to Embedded Systems. Ideal for beginners to get started with Embedded fundamentals.
Next Generation Skills for IoT

Industry 4.0 is all about connecting everything. Popularly known as Internet-Of-Things, this new phenomenon is changing the way we live. What are the skills required for fresh engineers and working professionals to harness the potential of IoT? How to make a career out of it? As a part of India Electronics Week 2018, team Emertxe shared details about the same in form of this presentation. Read on!
Why Gateways are Important in Your IoT Architecture

Constructing the IoT Solution. Learn why gateways are important to your IoT architecture and the components, requirements, benchmarks and benefits.
MATLAB Electronics Projects Research Topics

This document lists electronics projects that can be done using Matlab, including an RFID indoor positioning system, an auto switching magnetic door lock system, and a microcontroller based face recognition system. It discusses key fields like embedded systems, power electronics, and RFID. Major electronic domains covered are digital systems, hybrid microcircuits, semiconductor technology, embedded systems, and agri electronics. Contact information is provided to learn more.
Internet of things : Beginners view

The document provides an introduction to IoT from the perspective of Emertxe, an IT finishing school focused on embedded systems. It discusses the evolution of computing towards connecting non-digital devices through IoT. IoT blurs technological lines through the combination of hardware, sensors, connectivity and applications. The trends driving IoT include falling costs, widespread internet access, and open source software and hardware. IoT provides opportunities for careers in areas like embedded systems, and students are encouraged to build on fundamentals, gain hands-on experience, and continue learning.
Soldatos io t-academy-cosmote-231117-v-final

The document discusses edge computing and 5G networks for IoT applications. It notes that using cloud computing alone has limitations like wasted bandwidth, high latency, inefficient storage, and limited flexibility for privacy. Edge computing processes data at network edges using devices like gateways and small data centers to address these issues. The document also explores several EU-funded projects applying edge computing for applications in manufacturing and autonomous vehicles. It outlines how 5G networks can further support IoT by enabling more data and lower latency connectivity.
Skilling Entry Level Engineers in IoT - A Practical Approach

Skilling Entry Level Engineers in IoT - A Practical ApproachEmertxe Information Technologies Pvt Ltd
This document discusses an approach to skill entry level engineers in IoT. It outlines a multi-phase program that begins with building strong foundations in algorithms, data structures, and programming. Students are continuously assessed and receive feedback to improve. They are helped to identify their strengths and passions. Domain skills in IoT, embedded systems, and full stack development are then developed through hands-on projects. Constant mentoring and continuous improvement of the system helps ensure students are prepared for jobs in IoT. Key results include reduced hiring costs, high placement rates, and positive student outcomes.IOT beginnners

The document discusses various topics related to Internet of Things (IoT) including IoT concepts to master, embedded systems, Arduino boards, analog and digital input/output, serial communication, cloud platforms, IoT protocols like MQTT and CoAP. It provides an overview of getting started with Arduino, interfacing sensors like PIR, and communicating with cloud platforms.
Solving connectivity for the Internet of Things - Telenor Group Technology Fair

Presentation I gave during Telenor Technology fair on 25th November
The video: blog.telenor.io/video/2015/12/08/solving-connectivity-iot.html
3.pillars of embedded io t and physical devices

This document discusses the key concepts and components of embedded IoT and physical devices. It describes the four pillars of IoT as M2M, RFID, WSN and SCADA. It then explains the Device-Connect-Manage model and provides examples of IoT physical devices like the Raspberry Pi. The document outlines the basic building blocks of an IoT device and covers interfaces and programming of the Raspberry Pi.
Lab introduction

This document discusses Internet of Things (IoT) technologies and applications. It begins by describing enabling technologies like open source platforms, wireless connectivity, cheap sensors and processors, and big data/cloud computing. It then discusses common IoT applications in areas like wearables, e-health, smart homes/offices, industry, and environment. The document also provides an overview of typical IoT architectures, components, communication protocols, operating systems, and development tools and platforms. It concludes with examples of IoT demo applications and a proposed step-by-step approach for learning and developing IoT systems.
Ppt on six month training on embedded system & IOT

the embedded system is a basic building block of IOT. so in this ppt, i have shared my training experience
Arduino in TinyML with Edge Impulse

This document provides an overview of TinyML and how to implement it using Edge Impulse and the Nano 33 BLE Sense board. It defines key ML concepts and discusses TinyML applications. It then explains the Edge Impulse platform for data collection, model training and testing, and deployment to microcontroller boards. Finally, it demonstrates a practical TinyML workflow using the Nano 33 BLE Sense board with Edge Impulse to collect sensor data and train, test, and deploy a model on the board.
Building IoT with Arduino Day One 

Day one presentation of the Building Internet of things with Arduino training held at the University of Dodoma Tanzania.
Arduino TinyML & IoT

An introduction to Sensa showcasing how it can be used to optimize TinyML & IoT Pipelines.
Tutorial & Demo on Using Sensa for the Data collection Stage in the Tiny-Machine-Learning Pipeline.
Installation and Getting Started with the AIfES library on the Arduino Board for AI applications.
An end-to-end application showcasing a regression TinyML program with the help of Sensa and AIfES.
Introduction To Embedded Systems

This document provides an overview of embedded systems and trends in three paragraphs:
It defines an embedded system as any electronic device that incorporates a microprocessor to perform dedicated tasks. It discusses the history of embedded systems from early military and calculator applications to today where they are ubiquitous. It lists some common applications of embedded systems like ATMs, phones, vehicles, industrial equipment, and medical devices.
IoT Levels and Deployment Templates

The document describes 6 levels of IoT systems with increasing complexity. Level 1 has a single device that performs all functions. Level 2 has local analysis and cloud storage. Level 3 has cloud storage, analysis and applications. Level 4 has multiple analyzing nodes. Level 5 uses a coordinator node. Level 6 has independent nodes that communicate with the cloud. Each level is illustrated with an example system like home automation, smart irrigation or weather monitoring. The document also lists some common IoT issues as security, privacy, interoperability, legal compliance, and economic challenges.
Conectividad inalámbrica para Internet de las cosas(Telecomunicaciones)

The document discusses wireless connectivity technologies for IoT applications. It reviews predominant wireless standards, including their technical concepts, tradeoffs for selection. Wi-Fi is described as the standard for Internet connectivity, integrated with TCP/IP. It has widespread deployment in homes, offices and public areas. While complex, Wi-Fi and TCP/IP integration into silicon is now enabling more IoT devices to connect to the Internet wirelessly.
Building IoT devices with ARM mbed - RISE Manchester

This document discusses building Internet of Things (IoT) devices using ARM mbed. It addresses three common problems in building smart devices: how to build them, how to connect them, and how to manage them. ARM mbed is presented as a solution to streamline development across multiple device platforms through its online IDE, code sharing capabilities, and libraries. Connectivity options for IoT like Bluetooth LE, WiFi, and cellular networks are reviewed. ARM's mbed Device Connector is demonstrated as a way to manage devices regardless of connection protocol through features like encryption and firmware updates. The presentation aims to help developers build their first connected device by walking through an example Bluetooth LE project.
I learning lot

1) The document proposes an IoT-based home automation system that monitors environmental conditions, controls devices, and detects and corrects faults automatically.
2) It collects sensor data to understand the environment and detect device issues. A home PC monitors sensors and controls devices, reporting problems to the cloud server.
3) The cloud server applies data mining to notify the appropriate technician via SMS/email when issues arise based on registered service providers. This allows for flexible, energy efficient home automation with self-learning capabilities.
Anatomy of a network

The document summarizes the network configuration of Dodgeville High School from the perspective of a teacher returning after a 4 year absence. The key points are:
1) The network uses a star topology with Ethernet cables running from each classroom PC through the ceiling to hubs in the network administrator's office.
2) There are 6 servers including 2 Novell servers for student/teacher data and 4 Windows servers for other functions like the library catalog.
3) Software runs locally on each PC rather than from a server for faster performance. Files are stored on user directories on the file server.
4) The school has 2 networked printers and internet access that is filtered through the servers via a 40MB connection provided
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC) is a bi monthly open access peer-reviewed journal provides excellent international forum for sharing knowledge and results in theory, methodology and applications of Ad Hoc & Ubiquitous computing. Current information age is witnessing a dramatic use of digital and electronic devices in the workplace and beyond. Ubiquitous Computing presents a rather arduous requirement of robustness, reliability and availability to the end user. Ad hoc, Sensor & Ubiquitous computing has received a significant and sustained research interest in terms of designing and deploying large scale and high performance computational applications in real life.
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC) 

International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC) is a bi monthly open access peer-reviewed journal provides excellent international forum for sharing knowledge and results in theory, methodology and applications of Ad Hoc & Ubiquitous computing. Current information age is witnessing a dramatic use of digital and electronic devices in the workplace and beyond. Ubiquitous Computing presents a rather arduous requirement of robustness, reliability and availability to the end user. Ad hoc, Sensor & Ubiquitous computing has received a significant and sustained research interest in terms of designing and deploying large scale and high performance computational applications in real life.
Mais conteúdo relacionado
Mais procurados
Next Generation Skills for IoT

Industry 4.0 is all about connecting everything. Popularly known as Internet-Of-Things, this new phenomenon is changing the way we live. What are the skills required for fresh engineers and working professionals to harness the potential of IoT? How to make a career out of it? As a part of India Electronics Week 2018, team Emertxe shared details about the same in form of this presentation. Read on!
Why Gateways are Important in Your IoT Architecture

Constructing the IoT Solution. Learn why gateways are important to your IoT architecture and the components, requirements, benchmarks and benefits.
MATLAB Electronics Projects Research Topics

This document lists electronics projects that can be done using Matlab, including an RFID indoor positioning system, an auto switching magnetic door lock system, and a microcontroller based face recognition system. It discusses key fields like embedded systems, power electronics, and RFID. Major electronic domains covered are digital systems, hybrid microcircuits, semiconductor technology, embedded systems, and agri electronics. Contact information is provided to learn more.
Internet of things : Beginners view

The document provides an introduction to IoT from the perspective of Emertxe, an IT finishing school focused on embedded systems. It discusses the evolution of computing towards connecting non-digital devices through IoT. IoT blurs technological lines through the combination of hardware, sensors, connectivity and applications. The trends driving IoT include falling costs, widespread internet access, and open source software and hardware. IoT provides opportunities for careers in areas like embedded systems, and students are encouraged to build on fundamentals, gain hands-on experience, and continue learning.
Soldatos io t-academy-cosmote-231117-v-final

The document discusses edge computing and 5G networks for IoT applications. It notes that using cloud computing alone has limitations like wasted bandwidth, high latency, inefficient storage, and limited flexibility for privacy. Edge computing processes data at network edges using devices like gateways and small data centers to address these issues. The document also explores several EU-funded projects applying edge computing for applications in manufacturing and autonomous vehicles. It outlines how 5G networks can further support IoT by enabling more data and lower latency connectivity.
Skilling Entry Level Engineers in IoT - A Practical Approach

Skilling Entry Level Engineers in IoT - A Practical ApproachEmertxe Information Technologies Pvt Ltd
This document discusses an approach to skill entry level engineers in IoT. It outlines a multi-phase program that begins with building strong foundations in algorithms, data structures, and programming. Students are continuously assessed and receive feedback to improve. They are helped to identify their strengths and passions. Domain skills in IoT, embedded systems, and full stack development are then developed through hands-on projects. Constant mentoring and continuous improvement of the system helps ensure students are prepared for jobs in IoT. Key results include reduced hiring costs, high placement rates, and positive student outcomes.IOT beginnners

The document discusses various topics related to Internet of Things (IoT) including IoT concepts to master, embedded systems, Arduino boards, analog and digital input/output, serial communication, cloud platforms, IoT protocols like MQTT and CoAP. It provides an overview of getting started with Arduino, interfacing sensors like PIR, and communicating with cloud platforms.
Solving connectivity for the Internet of Things - Telenor Group Technology Fair

Presentation I gave during Telenor Technology fair on 25th November
The video: blog.telenor.io/video/2015/12/08/solving-connectivity-iot.html
3.pillars of embedded io t and physical devices

This document discusses the key concepts and components of embedded IoT and physical devices. It describes the four pillars of IoT as M2M, RFID, WSN and SCADA. It then explains the Device-Connect-Manage model and provides examples of IoT physical devices like the Raspberry Pi. The document outlines the basic building blocks of an IoT device and covers interfaces and programming of the Raspberry Pi.
Lab introduction

This document discusses Internet of Things (IoT) technologies and applications. It begins by describing enabling technologies like open source platforms, wireless connectivity, cheap sensors and processors, and big data/cloud computing. It then discusses common IoT applications in areas like wearables, e-health, smart homes/offices, industry, and environment. The document also provides an overview of typical IoT architectures, components, communication protocols, operating systems, and development tools and platforms. It concludes with examples of IoT demo applications and a proposed step-by-step approach for learning and developing IoT systems.
Ppt on six month training on embedded system & IOT

the embedded system is a basic building block of IOT. so in this ppt, i have shared my training experience
Arduino in TinyML with Edge Impulse

This document provides an overview of TinyML and how to implement it using Edge Impulse and the Nano 33 BLE Sense board. It defines key ML concepts and discusses TinyML applications. It then explains the Edge Impulse platform for data collection, model training and testing, and deployment to microcontroller boards. Finally, it demonstrates a practical TinyML workflow using the Nano 33 BLE Sense board with Edge Impulse to collect sensor data and train, test, and deploy a model on the board.
Building IoT with Arduino Day One 

Day one presentation of the Building Internet of things with Arduino training held at the University of Dodoma Tanzania.
Arduino TinyML & IoT

An introduction to Sensa showcasing how it can be used to optimize TinyML & IoT Pipelines.
Tutorial & Demo on Using Sensa for the Data collection Stage in the Tiny-Machine-Learning Pipeline.
Installation and Getting Started with the AIfES library on the Arduino Board for AI applications.
An end-to-end application showcasing a regression TinyML program with the help of Sensa and AIfES.
Introduction To Embedded Systems

This document provides an overview of embedded systems and trends in three paragraphs:
It defines an embedded system as any electronic device that incorporates a microprocessor to perform dedicated tasks. It discusses the history of embedded systems from early military and calculator applications to today where they are ubiquitous. It lists some common applications of embedded systems like ATMs, phones, vehicles, industrial equipment, and medical devices.
IoT Levels and Deployment Templates

The document describes 6 levels of IoT systems with increasing complexity. Level 1 has a single device that performs all functions. Level 2 has local analysis and cloud storage. Level 3 has cloud storage, analysis and applications. Level 4 has multiple analyzing nodes. Level 5 uses a coordinator node. Level 6 has independent nodes that communicate with the cloud. Each level is illustrated with an example system like home automation, smart irrigation or weather monitoring. The document also lists some common IoT issues as security, privacy, interoperability, legal compliance, and economic challenges.
Conectividad inalámbrica para Internet de las cosas(Telecomunicaciones)

The document discusses wireless connectivity technologies for IoT applications. It reviews predominant wireless standards, including their technical concepts, tradeoffs for selection. Wi-Fi is described as the standard for Internet connectivity, integrated with TCP/IP. It has widespread deployment in homes, offices and public areas. While complex, Wi-Fi and TCP/IP integration into silicon is now enabling more IoT devices to connect to the Internet wirelessly.
Building IoT devices with ARM mbed - RISE Manchester

This document discusses building Internet of Things (IoT) devices using ARM mbed. It addresses three common problems in building smart devices: how to build them, how to connect them, and how to manage them. ARM mbed is presented as a solution to streamline development across multiple device platforms through its online IDE, code sharing capabilities, and libraries. Connectivity options for IoT like Bluetooth LE, WiFi, and cellular networks are reviewed. ARM's mbed Device Connector is demonstrated as a way to manage devices regardless of connection protocol through features like encryption and firmware updates. The presentation aims to help developers build their first connected device by walking through an example Bluetooth LE project.
I learning lot

1) The document proposes an IoT-based home automation system that monitors environmental conditions, controls devices, and detects and corrects faults automatically.
2) It collects sensor data to understand the environment and detect device issues. A home PC monitors sensors and controls devices, reporting problems to the cloud server.
3) The cloud server applies data mining to notify the appropriate technician via SMS/email when issues arise based on registered service providers. This allows for flexible, energy efficient home automation with self-learning capabilities.
Anatomy of a network

The document summarizes the network configuration of Dodgeville High School from the perspective of a teacher returning after a 4 year absence. The key points are:
1) The network uses a star topology with Ethernet cables running from each classroom PC through the ceiling to hubs in the network administrator's office.
2) There are 6 servers including 2 Novell servers for student/teacher data and 4 Windows servers for other functions like the library catalog.
3) Software runs locally on each PC rather than from a server for faster performance. Files are stored on user directories on the file server.
4) The school has 2 networked printers and internet access that is filtered through the servers via a 40MB connection provided
Mais procurados (20)
Why Gateways are Important in Your IoT Architecture

Why Gateways are Important in Your IoT Architecture
Skilling Entry Level Engineers in IoT - A Practical Approach

Skilling Entry Level Engineers in IoT - A Practical Approach
Solving connectivity for the Internet of Things - Telenor Group Technology Fair

Solving connectivity for the Internet of Things - Telenor Group Technology Fair
Ppt on six month training on embedded system & IOT

Ppt on six month training on embedded system & IOT
Conectividad inalámbrica para Internet de las cosas(Telecomunicaciones)

Conectividad inalámbrica para Internet de las cosas(Telecomunicaciones)
Building IoT devices with ARM mbed - RISE Manchester

Building IoT devices with ARM mbed - RISE Manchester
Semelhante a Internet of Things & Smart Cities Intro
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC) is a bi monthly open access peer-reviewed journal provides excellent international forum for sharing knowledge and results in theory, methodology and applications of Ad Hoc & Ubiquitous computing. Current information age is witnessing a dramatic use of digital and electronic devices in the workplace and beyond. Ubiquitous Computing presents a rather arduous requirement of robustness, reliability and availability to the end user. Ad hoc, Sensor & Ubiquitous computing has received a significant and sustained research interest in terms of designing and deploying large scale and high performance computational applications in real life.
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC) 

International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC) is a bi monthly open access peer-reviewed journal provides excellent international forum for sharing knowledge and results in theory, methodology and applications of Ad Hoc & Ubiquitous computing. Current information age is witnessing a dramatic use of digital and electronic devices in the workplace and beyond. Ubiquitous Computing presents a rather arduous requirement of robustness, reliability and availability to the end user. Ad hoc, Sensor & Ubiquitous computing has received a significant and sustained research interest in terms of designing and deploying large scale and high performance computational applications in real life.
International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC)

The document is a call for papers for the International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC). The journal publishes peer-reviewed articles bi-monthly on topics related to ad hoc and ubiquitous computing, including sensor networks, mobile computing, and wireless communication. Authors are invited to submit original, unpublished papers by June 12, 2021. Notification of acceptance will be provided by July 12, 2021, with final manuscripts due by July 20, 2021.
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC) 

The document is a call for papers for the International Journal of Ad hoc, Sensor & Ubiquitous Computing. The journal publishes peer-reviewed articles on topics related to ad hoc and ubiquitous computing, including sensor networks, mobile ad hoc networks, and wireless sensor networks. Authors are invited to submit original papers by July 17, 2021. Notification of acceptance will be provided by August 17, 2021, and final manuscripts will be due by August 25, 2021.
International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC) is a bi monthly open access peer-reviewed journal provides excellent international forum for sharing knowledge and results in theory, methodology and applications of Ad Hoc & Ubiquitous computing. Current information age is witnessing a dramatic use of digital and electronic devices in the workplace and beyond. Ubiquitous Computing presents a rather arduous requirement of robustness, reliability and availability to the end user. Ad hoc, Sensor & Ubiquitous computing has received a significant and sustained research interest in terms of designing and deploying large scale and high performance computational applications in real life.
International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC) is a bi monthly open access peer-reviewed journal provides excellent international forum for sharing knowledge and results in theory, methodology and applications of Ad Hoc & Ubiquitous computing. Current information age is witnessing a dramatic use of digital and electronic devices in the workplace and beyond. Ubiquitous Computing presents a rather arduous requirement of robustness, reliability and availability to the end user. Ad hoc, Sensor & Ubiquitous computing has received a significant and sustained research interest in terms of designing and deploying large scale and high performance computational applications in real life.
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC) 

International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC) is a bi monthly open access peer-reviewed journal provides excellent international forum for sharing knowledge and results in theory, methodology and applications of Ad Hoc & Ubiquitous computing. Current information age is witnessing a dramatic use of digital and electronic devices in the workplace and beyond. Ubiquitous Computing presents a rather arduous requirement of robustness, reliability and availability to the end user. Ad hoc, Sensor & Ubiquitous computing has received a significant and sustained research interest in terms of designing and deploying large scale and high performance computational applications in real life.
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC) is a bi monthly open access peer-reviewed journal provides excellent international forum for sharing knowledge and results in theory, methodology and applications of Ad Hoc & Ubiquitous computing. Current information age is witnessing a dramatic use of digital and electronic devices in the workplace and beyond. Ubiquitous Computing presents a rather arduous requirement of robustness, reliability and availability to the end user. Ad hoc, Sensor & Ubiquitous computing has received a significant and sustained research interest in terms of designing and deploying large scale and high performance computational applications in real life.
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC) is a bi monthly open access peer-reviewed journal provides excellent international forum for sharing knowledge and results in theory, methodology and applications of Ad Hoc & Ubiquitous computing. Current information age is witnessing a dramatic use of digital and electronic devices in the workplace and beyond. Ubiquitous Computing presents a rather arduous requirement of robustness, reliability and availability to the end user. Ad hoc, Sensor & Ubiquitous computing has received a significant and sustained research interest in terms of designing and deploying large scale and high performance computational applications in real life.
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC) is a bi monthly open access peer-reviewed journal provides excellent international forum for sharing knowledge and results in theory, methodology and applications of Ad Hoc & Ubiquitous computing. Current information age is witnessing a dramatic use of digital and electronic devices in the workplace and beyond. Ubiquitous Computing presents a rather arduous requirement of robustness, reliability and availability to the end user. Ad hoc, Sensor & Ubiquitous computing has received a significant and sustained research interest in terms of designing and deploying large scale and high performance computational applications in real life.
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)

The document is a call for papers for the International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC). It provides details about the journal, including that it is a bi-monthly peer-reviewed journal covering topics related to ad hoc computing, sensor networks, and ubiquitous computing. Authors are invited to submit original papers by July 31, 2021, with notification of acceptance by August 25, 2021 and final manuscripts due by August 30, 2021. The journal aims to provide an international forum for sharing knowledge and results in ad hoc, sensor, and ubiquitous computing.
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC) is a bi monthly open access peer-reviewed journal provides excellent international forum for sharing knowledge and results in theory, methodology and applications of Ad Hoc & Ubiquitous computing. Current information age is witnessing a dramatic use of digital and electronic devices in the workplace and beyond. Ubiquitous Computing presents a rather arduous requirement of robustness, reliability and availability to the end user. Ad hoc, Sensor & Ubiquitous computing has received a significant and sustained research interest in terms of designing and deploying large scale and high performance computational applications in real life.
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC) 

International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC) is a bi monthly open access peer-reviewed journal provides excellent international forum for sharing knowledge and results in theory, methodology and applications of Ad Hoc & Ubiquitous computing. Current information age is witnessing a dramatic use of digital and electronic devices in the workplace and beyond. Ubiquitous Computing presents a rather arduous requirement of robustness, reliability and availability to the end user. Ad hoc, Sensor & Ubiquitous computing has received a significant and sustained research interest in terms of designing and deploying large scale and high performance computational applications in real life.
Multi-Robot Sensor Relocation to Enhance Connectivity in a WSN

Ensuring connectivity in Wireless Sensor Networks (WSN) is a challenging issue, especially in hazardous areas (like battlefield). Many applications of WSN require an important level of connectivity in the network to detect a given event (like detection Intrusion) and forward it to the ”sink” node in order to alert users. For these risky areas the deterministic deployment is not usually guaranteed and the network is composed by a set of disconnected Islands. We present in our work two strategies to relocate sensors in order to improve the connectivity using mobile Robots. These two solutions are called Multi-Robot Island-based Relocation (MRIBR) and Multi-Robot Grid-Based Island-based Relocation (MRGIR). Through several simulations, we show that MRGIR outperforms MRIBR. Our study can be used especially to make a tradeoff between the number of deployed sensors and the numbers of the used mobile robots, according to the quality needed for the application.
International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC) is a bi monthly open access peer-reviewed journal provides excellent international forum for sharing knowledge and results in theory, methodology and applications of Ad Hoc & Ubiquitous computing. Current information age is witnessing a dramatic use of digital and electronic devices in the workplace and beyond. Ubiquitous Computing presents a rather arduous requirement of robustness, reliability and availability to the end user. Ad hoc, Sensor & Ubiquitous computing has received a significant and sustained research interest in terms of designing and deploying large scale and high performance computational applications in real life.
International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC) 

International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC) is a bi monthly open access peer-reviewed journal provides excellent international forum for sharing knowledge and results in theory, methodology and applications of Ad Hoc & Ubiquitous computing. Current information age is witnessing a dramatic use of digital and electronic devices in the workplace and beyond. Ubiquitous Computing presents a rather arduous requirement of robustness, reliability and availability to the end user. Ad hoc, Sensor & Ubiquitous computing has received a significant and sustained research interest in terms of designing and deploying large scale and high performance computational applications in real life.
International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC) is a bi monthly open access peer-reviewed journal provides excellent international forum for sharing knowledge and results in theory, methodology and applications of Ad Hoc & Ubiquitous computing. Current information age is witnessing a dramatic use of digital and electronic devices in the workplace and beyond. Ubiquitous Computing presents a rather arduous requirement of robustness, reliability and availability to the end user. Ad hoc, Sensor & Ubiquitous computing has received a significant and sustained research interest in terms of designing and deploying large scale and high performance computational applications in real life.
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC) is a bi monthly open access peer-reviewed journal provides excellent international forum for sharing knowledge and results in theory, methodology and applications of Ad Hoc & Ubiquitous computing. Current information age is witnessing a dramatic use of digital and electronic devices in the workplace and beyond. Ubiquitous Computing presents a rather arduous requirement of robustness, reliability and availability to the end user. Ad hoc, Sensor & Ubiquitous computing has received a significant and sustained research interest in terms of designing and deploying large scale and high performance computational applications in real life.
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC) is a bi monthly open access peer-reviewed journal provides excellent international forum for sharing knowledge and results in theory, methodology and applications of Ad Hoc & Ubiquitous computing. Current information age is witnessing a dramatic use of digital and electronic devices in the workplace and beyond. Ubiquitous Computing presents a rather arduous requirement of robustness, reliability and availability to the end user. Ad hoc, Sensor & Ubiquitous computing has received a significant and sustained research interest in terms of designing and deploying large scale and high performance computational applications in real life.
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC) is a bi monthly open access peer-reviewed journal provides excellent international forum for sharing knowledge and results in theory, methodology and applications of Ad Hoc & Ubiquitous computing. Current information age is witnessing a dramatic use of digital and electronic devices in the workplace and beyond. Ubiquitous Computing presents a rather arduous requirement of robustness, reliability and availability to the end user. Ad hoc, Sensor & Ubiquitous computing has received a significant and sustained research interest in terms of designing and deploying large scale and high performance computational applications in real life.
Semelhante a Internet of Things & Smart Cities Intro (20)
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC) 

International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)
International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC)
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC) 

International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)
International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC)
International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC)
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC) 

International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC) 

International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)
Multi-Robot Sensor Relocation to Enhance Connectivity in a WSN

Multi-Robot Sensor Relocation to Enhance Connectivity in a WSN
International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC)
International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC) 

International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC)
International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, sensor & Ubiquitous Computing (IJASUC)
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)
International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)

International Journal of Ad hoc, Sensor & Ubiquitous Computing (IJASUC)
Mais de Emertxe Information Technologies Pvt Ltd
10_isxdigit.pdf

The document discusses implementing a function to check if a character is a hexadecimal digit. It explains that a hexadecimal digit ranges from 0-9, A-F, a-f in the ASCII table. It provides examples of inputting different characters and checking if they are hexadecimal digits or not. The sample execution section is empty. It lists functions as the prerequisite for understanding how to create a custom function to check for hexadecimal digits.
01_student_record.pdf

The document provides an example program to implement a student record system using an array of structures. It involves reading the number of students and subjects, student names and marks for each subject, calculating averages and grades. The program displays menus to view all student details or a particular student's details based on roll number or name. It demonstrates declaring a structure for student records, reading input into an array of structures, calculating averages and grades, and printing the student records with options to search by roll number or name.
02_swap.pdf

This document discusses writing a macro called swap(t,x,y) that swaps two arguments of any data type t. It asks the user to input a data type and two values of that type, then swaps the values and displays the output. It explains how to swap two integers by using a temporary variable and applying the same concept to arguments of any type t by using macros. The objective is to understand macro preprocessing in C.
01_sizeof.pdf

This document discusses defining a macro called SIZEOF to return the size of a data type without using the sizeof operator. It explains that by taking the difference of the addresses of a variable and the variable plus one, cast to char pointers, you can get the size in bytes. An example is provided using an integer variable x, showing how taking the difference of (&x+1) and &x after casting to char pointers returns the size of an int, which is 4 bytes. Background on macros and pointers is provided. The objective is stated as understanding macro usage in preprocessing.
07_product_matrix.pdf

The document describes a C program to multiply two matrices. It explains that the program takes input of rows and columns for Matrix A and B, reads in the element values, and checks that the column of the first matrix equals the row of the second before calculating the product. An example is provided where the matrices can be multiplied, producing the output matrix, and another where they cannot due to mismatched dimensions. Requirements for the program include pointers, 2D arrays, and dynamic memory allocation.
06_sort_names.pdf

The document describes an assignment to read in an unspecified number (n) of names of up to 20 characters each, sort the names alphabetically, and print the sorted list. It provides examples of reading in 3 names ("Arunachal", "Bengaluru", "Agra"), sorting them using a custom string comparison function, and printing the sorted list ("Agra", "Arunachal", "Bengaluru"). Pre-requisites for the assignment include functions, dynamic arrays, and pointers. The objective is to understand how to use functions, arrays and pointers to complete the task.
05_fragments.pdf

This document provides instructions for an assignment to implement fragments using an array of pointers. It asks the student to write a program that reads the number of rows and columns for each row, reads the elements for each row, calculates the average for each row, sorts the rows based on average, and prints the results. It includes examples that show reading input values, storing them in an array using pointers, calculating averages, sorting rows, and sample output. The prerequisites are listed as pointers, functions, and dynamic memory allocation, and the objective is stated as understanding dynamic memory allocation and arrays of pointers.
04_magic_square.pdf

The document describes an algorithm to generate a magic square of size n×n. It takes the integer n as input from the user and outputs the n×n magic square. A magic square is an arrangement of distinct numbers in a square grid where the sum of each row, column and diagonal is equal. The algorithm uses steps like starting from the middle of the grid and moving element by element in a pattern, wrapping around when reaching the boundaries.
03_endianess.pdf

This document discusses endianness and provides an example program to convert between little endian and big endian formats. It defines endianness as the order of bytes in memory, and describes little endian as having the least significant byte at the lowest memory address and big endian as the opposite. An example shows inputting a 2-byte number in little endian format and outputting it in big endian. Pre-requisites of pointers and the objective of understanding endianness representations are also stated.
02_variance.pdf

The document provides steps to calculate variance of an array using dynamic memory allocation in C. It explains what variance is, shows an example to calculate variance of a sample array by finding the mean, deviations from mean, squaring the deviations and calculating the average of squared deviations. The key steps are: 1) Read array size and elements, 2) Calculate mean, 3) Find deviations from mean, 4) Square the deviations and store in another array, 5) Calculate average of squared deviations to get variance.
01_memory_manager.pdf

This document provides examples for an assignment to create a menu-driven program that stores and manipulates different data types (char, int, float, double) in dynamically allocated memory. It allocates 8 consecutive bytes to store the variables and uses flags to track which data types are stored. The menu allows the user to add, display, and remove elements as well as exit the program. Examples demonstrate initializing the flags, adding/removing elements, updating the flags, and displaying only elements whose flags are set. The objective is to understand dynamic memory allocation using pointers.
09_nrps.pdf

The document discusses generating non-repetitive pattern strings (NRPS) of length n using k distinct characters. It explains that an NRPS has a pattern that is not repeated consecutively. It provides steps to check if a string is an NRPS, including comparing characters and resetting a count if characters do not match. It also describes how to create an NRPS by starting with an ordered pattern and then copying subsequent characters to generate new patterns without repetition until the string reaches the desired length n. Sample inputs and outputs are provided.
11_pangram.pdf

The document discusses how to check if a string is a pangram, which is a sentence containing all 26 letters of the English alphabet. It provides an example of implementing the algorithm to check for a pangram by initializing an array to track letter occurrences, iterating through the input string to mark letters in the array, and checking if all letters are marked to determine if it is a pangram.
10_combinations.pdf

The document explains how to print all possible combinations of a given string by swapping characters. It provides an example of generating all six combinations of the string "ABC" through a step-by-step process of swapping characters. It also lists the prerequisites as strings, arrays, and pointers and the objective as understanding string manipulations.
08_squeeze.pdf

The document describes an assignment to write a program that squeezes characters from one string (s1) that match characters in a second string (s2). It provides examples of input/output and step-by-step demonstrations of the program removing matching characters from s1. It also lists prerequisites of functions, arrays, and pointers and the objective of understanding these concepts as they relate to strings.
07_strtok.pdf

The document discusses implementing the strtok() string tokenization function. It explains that strtok() breaks a string into tokens based on delimiters. The document then provides pseudocode to implement a custom strtok() function by iterating through the string, overwriting delimiter characters with null terminators to create tokens, and returning a pointer to each token. Sample input/output is provided. The objective is stated as understanding string functions, with prerequisites of strings, storage classes, and pointers.
06_reverserec.pdf

The document provides details on an assignment to write a program that recursively reverses a given string without using static variables, global variables, or loops. It includes the input, output, and examples of reversing the strings "Extreme" and "hello world". It also provides sample execution and pre-requisites of strings and recursive functions, with the objective being to understand reversing a string recursively.
05_reverseiter.pdf

The document provides code and examples for reversing a string using an iterative method in C++. It explains taking in a string as input, declaring output and input strings of the same length, and swapping the first and last characters, second and second to last, and so on through multiple iterations until the string is reversed. Examples show reversing the strings "Extreme" to "emertxE" and "hello world" to "dlrow olleh" through this iterative swap process. Pre-requisites of strings and loops are noted, with the objective stated as understanding string reversal using an iterative approach.
Mais de Emertxe Information Technologies Pvt Ltd (20)
Último
TrustArc Webinar - 2024 Global Privacy Survey

How does your privacy program stack up against your peers? What challenges are privacy teams tackling and prioritizing in 2024?
In the fifth annual Global Privacy Benchmarks Survey, we asked over 1,800 global privacy professionals and business executives to share their perspectives on the current state of privacy inside and outside of their organizations. This year’s report focused on emerging areas of importance for privacy and compliance professionals, including considerations and implications of Artificial Intelligence (AI) technologies, building brand trust, and different approaches for achieving higher privacy competence scores.
See how organizational priorities and strategic approaches to data security and privacy are evolving around the globe.
This webinar will review:
- The top 10 privacy insights from the fifth annual Global Privacy Benchmarks Survey
- The top challenges for privacy leaders, practitioners, and organizations in 2024
- Key themes to consider in developing and maintaining your privacy program
5th LF Energy Power Grid Model Meet-up Slides

5th Power Grid Model Meet-up
It is with great pleasure that we extend to you an invitation to the 5th Power Grid Model Meet-up, scheduled for 6th June 2024. This event will adopt a hybrid format, allowing participants to join us either through an online Mircosoft Teams session or in person at TU/e located at Den Dolech 2, Eindhoven, Netherlands. The meet-up will be hosted by Eindhoven University of Technology (TU/e), a research university specializing in engineering science & technology.
Power Grid Model
The global energy transition is placing new and unprecedented demands on Distribution System Operators (DSOs). Alongside upgrades to grid capacity, processes such as digitization, capacity optimization, and congestion management are becoming vital for delivering reliable services.
Power Grid Model is an open source project from Linux Foundation Energy and provides a calculation engine that is increasingly essential for DSOs. It offers a standards-based foundation enabling real-time power systems analysis, simulations of electrical power grids, and sophisticated what-if analysis. In addition, it enables in-depth studies and analysis of the electrical power grid’s behavior and performance. This comprehensive model incorporates essential factors such as power generation capacity, electrical losses, voltage levels, power flows, and system stability.
Power Grid Model is currently being applied in a wide variety of use cases, including grid planning, expansion, reliability, and congestion studies. It can also help in analyzing the impact of renewable energy integration, assessing the effects of disturbances or faults, and developing strategies for grid control and optimization.
What to expect
For the upcoming meetup we are organizing, we have an exciting lineup of activities planned:
-Insightful presentations covering two practical applications of the Power Grid Model.
-An update on the latest advancements in Power Grid -Model technology during the first and second quarters of 2024.
-An interactive brainstorming session to discuss and propose new feature requests.
-An opportunity to connect with fellow Power Grid Model enthusiasts and users.
Generating privacy-protected synthetic data using Secludy and Milvus

During this demo, the founders of Secludy will demonstrate how their system utilizes Milvus to store and manipulate embeddings for generating privacy-protected synthetic data. Their approach not only maintains the confidentiality of the original data but also enhances the utility and scalability of LLMs under privacy constraints. Attendees, including machine learning engineers, data scientists, and data managers, will witness first-hand how Secludy's integration with Milvus empowers organizations to harness the power of LLMs securely and efficiently.
AI 101: An Introduction to the Basics and Impact of Artificial Intelligence

Imagine a world where machines not only perform tasks but also learn, adapt, and make decisions. This is the promise of Artificial Intelligence (AI), a technology that's not just enhancing our lives but revolutionizing entire industries.
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Simplify your search for a reliable Python development partner! This list presents the top 10 trusted US providers offering comprehensive Python development services, ensuring your project's success from conception to completion.
Programming Foundation Models with DSPy - Meetup Slides

Prompting language models is hard, while programming language models is easy. In this talk, I will discuss the state-of-the-art framework DSPy for programming foundation models with its powerful optimizers and runtime constraint system.
20240609 QFM020 Irresponsible AI Reading List May 2024

Everything I found interesting about the irresponsible use of machine intelligence in May 2024
Skybuffer SAM4U tool for SAP license adoption

Manage and optimize your license adoption and consumption with SAM4U, an SAP free customer software asset management tool.
SAM4U, an SAP complimentary software asset management tool for customers, delivers a detailed and well-structured overview of license inventory and usage with a user-friendly interface. We offer a hosted, cost-effective, and performance-optimized SAM4U setup in the Skybuffer Cloud environment. You retain ownership of the system and data, while we manage the ABAP 7.58 infrastructure, ensuring fixed Total Cost of Ownership (TCO) and exceptional services through the SAP Fiori interface.
Building Production Ready Search Pipelines with Spark and Milvus

Spark is the widely used ETL tool for processing, indexing and ingesting data to serving stack for search. Milvus is the production-ready open-source vector database. In this talk we will show how to use Spark to process unstructured data to extract vector representations, and push the vectors to Milvus vector database for search serving.
Fueling AI with Great Data with Airbyte Webinar

This talk will focus on how to collect data from a variety of sources, leveraging this data for RAG and other GenAI use cases, and finally charting your course to productionalization.
20240607 QFM018 Elixir Reading List May 2024

Everything I found interesting about the Elixir programming ecosystem in May 2024
Salesforce Integration for Bonterra Impact Management (fka Social Solutions A...

Sidekick Solutions uses Bonterra Impact Management (fka Social Solutions Apricot) and automation solutions to integrate data for business workflows.
We believe integration and automation are essential to user experience and the promise of efficient work through technology. Automation is the critical ingredient to realizing that full vision. We develop integration products and services for Bonterra Case Management software to support the deployment of automations for a variety of use cases.
This video focuses on integration of Salesforce with Bonterra Impact Management.
Interested in deploying an integration with Salesforce for Bonterra Impact Management? Contact us at sales@sidekicksolutionsllc.com to discuss next steps.
Columbus Data & Analytics Wednesdays - June 2024

Columbus Data & Analytics Wednesdays, June 2024 with Maria Copot 20
Taking AI to the Next Level in Manufacturing.pdf

Read Taking AI to the Next Level in Manufacturing to gain insights on AI adoption in the manufacturing industry, such as:
1. How quickly AI is being implemented in manufacturing.
2. Which barriers stand in the way of AI adoption.
3. How data quality and governance form the backbone of AI.
4. Organizational processes and structures that may inhibit effective AI adoption.
6. Ideas and approaches to help build your organization's AI strategy.
Best 20 SEO Techniques To Improve Website Visibility In SERP

Boost your website's visibility with proven SEO techniques! Our latest blog dives into essential strategies to enhance your online presence, increase traffic, and rank higher on search engines. From keyword optimization to quality content creation, learn how to make your site stand out in the crowded digital landscape. Discover actionable tips and expert insights to elevate your SEO game.
HCL Notes and Domino License Cost Reduction in the World of DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-and-domino-license-cost-reduction-in-the-world-of-dlau/
The introduction of DLAU and the CCB & CCX licensing model caused quite a stir in the HCL community. As a Notes and Domino customer, you may have faced challenges with unexpected user counts and license costs. You probably have questions on how this new licensing approach works and how to benefit from it. Most importantly, you likely have budget constraints and want to save money where possible. Don’t worry, we can help with all of this!
We’ll show you how to fix common misconfigurations that cause higher-than-expected user counts, and how to identify accounts which you can deactivate to save money. There are also frequent patterns that can cause unnecessary cost, like using a person document instead of a mail-in for shared mailboxes. We’ll provide examples and solutions for those as well. And naturally we’ll explain the new licensing model.
Join HCL Ambassador Marc Thomas in this webinar with a special guest appearance from Franz Walder. It will give you the tools and know-how to stay on top of what is going on with Domino licensing. You will be able lower your cost through an optimized configuration and keep it low going forward.
These topics will be covered
- Reducing license cost by finding and fixing misconfigurations and superfluous accounts
- How do CCB and CCX licenses really work?
- Understanding the DLAU tool and how to best utilize it
- Tips for common problem areas, like team mailboxes, functional/test users, etc
- Practical examples and best practices to implement right away
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Discover how MongoDB Atlas and vector search technology can revolutionize your application's search capabilities. This comprehensive presentation covers:
* What is Vector Search?
* Importance and benefits of vector search
* Practical use cases across various industries
* Step-by-step implementation guide
* Live demos with code snippets
* Enhancing LLM capabilities with vector search
* Best practices and optimization strategies
Perfect for developers, AI enthusiasts, and tech leaders. Learn how to leverage MongoDB Atlas to deliver highly relevant, context-aware search results, transforming your data retrieval process. Stay ahead in tech innovation and maximize the potential of your applications.
#MongoDB #VectorSearch #AI #SemanticSearch #TechInnovation #DataScience #LLM #MachineLearning #SearchTechnology
Último (20)
Generating privacy-protected synthetic data using Secludy and Milvus

Generating privacy-protected synthetic data using Secludy and Milvus
AI 101: An Introduction to the Basics and Impact of Artificial Intelligence

AI 101: An Introduction to the Basics and Impact of Artificial Intelligence
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Your One-Stop Shop for Python Success: Top 10 US Python Development Providers
Programming Foundation Models with DSPy - Meetup Slides

Programming Foundation Models with DSPy - Meetup Slides
20240609 QFM020 Irresponsible AI Reading List May 2024

20240609 QFM020 Irresponsible AI Reading List May 2024
Building Production Ready Search Pipelines with Spark and Milvus

Building Production Ready Search Pipelines with Spark and Milvus
Salesforce Integration for Bonterra Impact Management (fka Social Solutions A...

Salesforce Integration for Bonterra Impact Management (fka Social Solutions A...
Best 20 SEO Techniques To Improve Website Visibility In SERP

Best 20 SEO Techniques To Improve Website Visibility In SERP
HCL Notes and Domino License Cost Reduction in the World of DLAU

HCL Notes and Domino License Cost Reduction in the World of DLAU
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf
Nordic Marketo Engage User Group_June 13_ 2024.pptx

Nordic Marketo Engage User Group_June 13_ 2024.pptx
Internet of Things & Smart Cities Intro
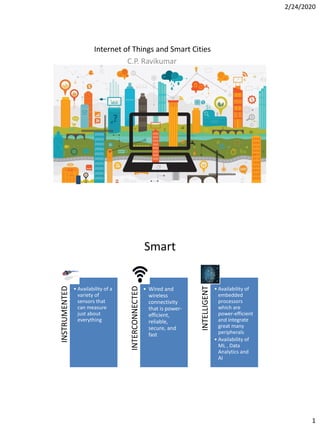
- 1. 2/24/2020 1 Internet of Things and Smart Cities C.P. Ravikumar Smart INSTRUMENTED • Availability of a variety of sensors that can measure just about everything INTERCONNECTED • Wired and wireless connectivity that is power- efficient, reliable, secure, and fast INTELLIGENT • Availability of embedded processors which are power-efficient and integrate great many peripherals • Availability of ML , Data Analytics and AI
- 2. 2/24/2020 2 Cities are growing in size and number Quality of life • traffic congestion • air quality Basic amenities • potable water, electricity • slums, hygiene Safety and security • crime, mental health and security • natural disasters Need to improve resource utilization MEASURE ANALYZE RECOMMEND ENFORCE
- 3. 2/24/2020 3 IoT in the S curve Evolution of IoT
- 4. 2/24/2020 4 Example of the automobile
- 5. 2/24/2020 5 A typical IoT Architecture IoT Architecture
- 6. 2/24/2020 6
- 7. 2/24/2020 7 • Ultrasonic sensing technology uses soundwaves rather than mechanical components to measure gas and water flow rates Smart sensors
- 8. 2/24/2020 8 • 30 GHz - 300 GHz range • Smaller antenna • Higher resolution mmWave Sensors for higher accuracy Smart factories Industry 4.0 Real-time control applications need time-bound communication
- 9. 2/24/2020 9 • India’s problems are different – – Larger population, crowded cities, difficult to scale – No clear boundary between urban/sub-urban/rural regions – Access to smart phones/laptops/computers is limited – Great diversity in languages and customs – IT-awareness is still building – Access to 24x7 power is not available – Law and social norms are different Need an Indian Perspective Where there are challenges, there are opportunities Garbage Disposal • Smart Garbage Disposal • Garbage metering • Intelligent pickup
