Firewall and Types of firewall
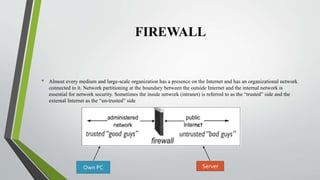
- 1. FIREWALL • Almost every medium and large-scale organization has a presence on the Internet and has an organizational network connected to it. Network partitioning at the boundary between the outside Internet and the internal network is essential for network security. Sometimes the inside network (intranet) is referred to as the “trusted” side and the external Internet as the “un-trusted” side Own PC Server
- 2. TYPES OF FIREWALL • Firewall is a network device that isolates organization’s internal network from larger outside network/Internet. It can be a hardware, software, or combined system/both that prevents unauthorized access to or from internal network. All data packets entering or leaving the internal network pass through the firewall, which examines each packet and blocks those that do not meet the specified security criteria.
- 3. Cont.… Firewall is categorized into three basic types: • Packet filter (Stateless & Stateful) • Application-level gateway • Circuit-level gateway
- 4. Network Layer or Packet Filtering Firewall The first type of network firewall was the packet filter which would look at network addresses and ports of the packet to determine if that packet should be allowed or blocked. In this type of firewall deployment, the internal network is connected to the external network/Internet via a router firewall. The firewall inspects and filters data packet-by packet. Packet-filtering firewalls allow or block the packets mostly based on criteria such as source and/or destination IP addresses, protocol, source and/or destination port numbers, and various other parameters within the IP header.
- 5. Cont.… • Filtering rules are based on information contained in a network packet: • Source IP address: The IP address of the system that originated the IP packet (e.g.,192.178.1.1) • Destination IP address: The IP address of the system the IP packet is trying to reach (e.g.,192.168.1.2) • Source and destination transport-level address: The transport level {(e.g., Transmission Control Protocol (TCP) or User Datagram Protocol (UDP)} port number, which defines applications such as SNMP or TELNET • IP protocol field: It’s work on a transport protocol which is transfer of data between end system using the services of the network layer. • Interface: For a router with three or more ports, which interface of the router the packet came from or which interface of the router the packet is destined.
- 6. Network Layer firewall generally fall into two sub-categories: Stateful: • Stateful firewall can watch traffic streams from end-to-end. They are aware of communication paths and can implement various IP security functions such as tunnels and encryption. If a packet does not match an exiting connection, it will be evaluated according to the ruleset for new connections. If a packet matches an existing connection based on comparison with firewall’s state table, it will be allowed to pass without further processing. Stateless: • Stateless firewalls require less memory , and can be faster for simple filters that require less time to filter than to look up a session. They may also be necessary for filtering stateless network protocols that have no concept of a session. However, they cannot make more complex decisions based on what stage communications between hosts have reached.
- 8. Application-level Gateways • Application-level gateways tend to be more secure than packet filters. Rather than trying to deal with the numerous possible combinations that are to be allowed and forbidden at the TCP and IP level, the application-level gateway need only scrutinize a few allowable applications. In addition, it is easy to log and audit all incoming traffic at the application level.
- 9. Application-level Gateways TErminal NETworkFileTransfer Protocol Simple MailTransfer ProtocolHypertextTransfer Protocol
- 10. Circuit-Level Gateway • Circuit-level gateway work at the session layer of the OSI model, or as a “shim-layer” between the application layer and the transport layer of the TCP/IP stack. • A circuit-level gateway does not permit an end-to-end TCP connection; rather, the gateway sets up two TCP connections, one between itself and a TCP user on an inner host and one between itself and a TCP user on an outside host. Once the two connections are established, the gateway typically relays TCP segments from one connection to the other without examining the contents. • A typical use of circuit-level gateways is a situation in which the system administrator trusts the internal users. The gateway can be configured to support application-level or proxy service on inbound connections and circuit-level functions for outbound connections.
- 12. Proxies • A proxy server may act as a firewall by responding to input packets in the manner of an application, while blocking other packets. A proxy server is a gateway from one network to another for a specific network application, in the sense that it functions as a proxy on behalf of the network user. • Proxies make tempering with an internal system from external network more difficult, so that misuse of one internal system would not necessarily cause a security reach exploitable from outside the firewall.Conversely, intruders may hijack a publicly reachable system and use it as proxy for their own purpose; the proxy then masquerades as that system to other internal machines.While use of internal address spaces enhances security, crackers may still employ method such as IP spoofing to attempt to pass packets to a target network.
- 13. NAT (Network AddressTranslation) • Firewall often have network address translation(NAT) functionally, and the host protected behind a firewall commonly have address in the “private address range”, as defined in RFC 1918. firewall often have such functionality to hide the true address of protected hosts. Originally, the NAT function was developed to address the limited number of IPv4 routable addresses that could be used or assigned to companies or individuals as well as reduce both the amount and therefore cost of obtaining enough public addresses for every computer in an organization. Although NAT on its own is not considered a security feature, hiding the addresses devices has become an often used defence against network. (ex: VPN)
