Ch03 2
•Transferir como PPT, PDF•
0 gostou•335 visualizações
Denunciar
Compartilhar
Denunciar
Compartilhar
Recomendados
Mais conteúdo relacionado
Mais procurados
Mais procurados (13)
Destaque
Semelhante a Ch03 2
Semelhante a Ch03 2 (20)
Mais de IDRIS USMANI
Último
Último (20)
Long journey of Ruby Standard library at RubyKaigi 2024

Long journey of Ruby Standard library at RubyKaigi 2024
Introduction to FIDO Authentication and Passkeys.pptx

Introduction to FIDO Authentication and Passkeys.pptx
Event-Driven Architecture Masterclass: Integrating Distributed Data Stores Ac...

Event-Driven Architecture Masterclass: Integrating Distributed Data Stores Ac...
Using IESVE for Room Loads Analysis - UK & Ireland

Using IESVE for Room Loads Analysis - UK & Ireland
Extensible Python: Robustness through Addition - PyCon 2024

Extensible Python: Robustness through Addition - PyCon 2024
How Red Hat Uses FDO in Device Lifecycle _ Costin and Vitaliy at Red Hat.pdf

How Red Hat Uses FDO in Device Lifecycle _ Costin and Vitaliy at Red Hat.pdf
Your enemies use GenAI too - staying ahead of fraud with Neo4j

Your enemies use GenAI too - staying ahead of fraud with Neo4j
Microsoft CSP Briefing Pre-Engagement - Questionnaire

Microsoft CSP Briefing Pre-Engagement - Questionnaire
Simplified FDO Manufacturing Flow with TPMs _ Liam at Infineon.pdf

Simplified FDO Manufacturing Flow with TPMs _ Liam at Infineon.pdf
1111 ChatGPT Prompts PDF Free Download - Prompts for ChatGPT

1111 ChatGPT Prompts PDF Free Download - Prompts for ChatGPT
Event-Driven Architecture Masterclass: Challenges in Stream Processing

Event-Driven Architecture Masterclass: Challenges in Stream Processing
Introduction to FDO and How It works Applications _ Richard at FIDO Alliance.pdf

Introduction to FDO and How It works Applications _ Richard at FIDO Alliance.pdf
Hyatt driving innovation and exceptional customer experiences with FIDO passw...

Hyatt driving innovation and exceptional customer experiences with FIDO passw...
ASRock Industrial FDO Solutions in Action for Industrial Edge AI _ Kenny at A...

ASRock Industrial FDO Solutions in Action for Industrial Edge AI _ Kenny at A...
The Value of Certifying Products for FDO _ Paul at FIDO Alliance.pdf

The Value of Certifying Products for FDO _ Paul at FIDO Alliance.pdf
Linux Foundation Edge _ Overview of FDO Software Components _ Randy at Intel.pdf

Linux Foundation Edge _ Overview of FDO Software Components _ Randy at Intel.pdf
Ch03 2
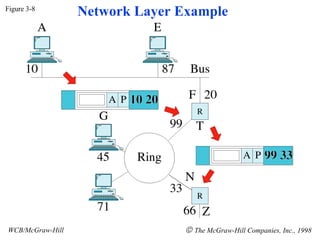
- 1. Figure 3-8 WCB/McGraw-Hill The McGraw-Hill Companies, Inc., 1998 Network Layer Example
- 2. Figure 3-8-continued WCB/McGraw-Hill The McGraw-Hill Companies, Inc., 1998 Network Layer Example
- 3. Figure 3-9 WCB/McGraw-Hill The McGraw-Hill Companies, Inc., 1998 Transport Layer
- 4. Figure 3-10 WCB/McGraw-Hill The McGraw-Hill Companies, Inc., 1998 Transport Layer Example
- 5. Figure 3-10-continued WCB/McGraw-Hill The McGraw-Hill Companies, Inc., 1998 Transport Layer Example
- 6. Figure 3-11 WCB/McGraw-Hill The McGraw-Hill Companies, Inc., 1998 Session Layer
- 7. Figure 3-12 WCB/McGraw-Hill The McGraw-Hill Companies, Inc., 1998 Presentation Layer
- 8. Figure 3-13 WCB/McGraw-Hill The McGraw-Hill Companies, Inc., 1998 Application Layer
- 9. Figure 3-14 WCB/McGraw-Hill The McGraw-Hill Companies, Inc., 1998 Summary of Layer Functions
