UNIVERSIDAD METROPOLITANA
•
0 gostou•154 visualizações
Denunciar
Compartilhar
Denunciar
Compartilhar
Baixar para ler offline
Recomendados
- Security is a concept similar to being cautious
or alert against any danger. Network security is the condition of
being protected against any danger or loss. Thus safety plays a
important role in bank transactions where disclosure of any data
results in big loss. We can define networking as the combination
of two or more computers for the purpose of resource sharing.
Resources here include files, database, emails etc. It is the
protection of these resources from unauthorized users that
brought the development of network security. It is a measure
incorporated to protect data during their transmission and also
to ensure the transmitted is protected and authentic.
Security of online bank transactions here has been
improved by increasing the number of bits while establishing the
SSL connection as well as in RSA asymmetric key encryption
along with SHA1 used for digital signature to authenticate the
userIMPLEMENTATION OF METHODS FOR TRANSACTION IN SECURE ONLINE BANKING

IMPLEMENTATION OF METHODS FOR TRANSACTION IN SECURE ONLINE BANKINGInternational Journal of Technical Research & Application
Recomendados
- Security is a concept similar to being cautious
or alert against any danger. Network security is the condition of
being protected against any danger or loss. Thus safety plays a
important role in bank transactions where disclosure of any data
results in big loss. We can define networking as the combination
of two or more computers for the purpose of resource sharing.
Resources here include files, database, emails etc. It is the
protection of these resources from unauthorized users that
brought the development of network security. It is a measure
incorporated to protect data during their transmission and also
to ensure the transmitted is protected and authentic.
Security of online bank transactions here has been
improved by increasing the number of bits while establishing the
SSL connection as well as in RSA asymmetric key encryption
along with SHA1 used for digital signature to authenticate the
userIMPLEMENTATION OF METHODS FOR TRANSACTION IN SECURE ONLINE BANKING

IMPLEMENTATION OF METHODS FOR TRANSACTION IN SECURE ONLINE BANKINGInternational Journal of Technical Research & Application
IMPROVEMENT OF SUPPLY CHAIN MANAGEMENT BY MATHEMATICAL PROGRAMMING APPROACHIMPROVEMENT OF SUPPLY CHAIN MANAGEMENT BY MATHEMATICAL PROGRAMMING APPROACH

IMPROVEMENT OF SUPPLY CHAIN MANAGEMENT BY MATHEMATICAL PROGRAMMING APPROACHInternational Journal of Technical Research & Application
- Nanoparticles NiFe2-xTbxO4 (x=0.00, 0.04, 0.08,
0.12) ferrite was prepared by solgel combution method. The
samples were characterized with X-ray diffraction and TEM
measurements. The effect of Tb3+ cations substitution on
structure of prepared nanoparticles was investigated. From the
analysis, the system was found to be inverse spinel cubic
structure. The lattice parameter (a) changes increases with Tb
doping content. Room temperature DC electrical resistivity
decreases. Dielectric properties have been studied in the
frequency range of 1 kHz to 5 MHz. Permittivity and tangent
loss (tanδ) decreases with the substitution of Tb3+ in parent
crystal structure.STRUCTURAL AND DIELECTRIC STUDIES OF TERBIUM SUBSTITUTED NICKEL FERRITE NANOP...

STRUCTURAL AND DIELECTRIC STUDIES OF TERBIUM SUBSTITUTED NICKEL FERRITE NANOP...International Journal of Technical Research & Application
- This experiment was conducted to study the
chronological relationships between estrus onset, time of LH
surge and ovulation time in does synchronized with chronogest
or CIDR. Forty six desert goats were divided into 2 groups (A,
and B). Induction of oestrous was carried out using
intravaginal sponges impregnated with 40 mg fluorgestone and
CIDR for group A and B respectively. At time of sponge or
CIDR removal, the animals were injected with 300IU eCG.
There was no significant difference in the estrus onset, estrous
duration, ovulation time and time of LH surge in does
synchronized with either chronogest or CIDR. Ovulation was
detected 54 hours post sponges or CIDR removal. LH surge
occurred 28 hours post removal of sponge or CIDR. No
significant difference was detected with regard to the time
taken from oestrus onset to ovulation time (25.4 and 23.5 hours
respectively). Also, there was no significant difference in the
time taken from LH surge to ovulation time in does
synchronized with chronogest and CIDR (25.6 and 25.3 hours)
respectively. In conclusion, findings observed pertaining to
estrous onset, time of ovulation and the time of onset of the LH
peak could be of value in timing AI or mating for maximum
conception in goat breeding programs when CIDR or sponges
were used with 300IU eCG.CHRONOLOGICAL RELATIONSHIPS BETWEEN ESTRUS ONSET, TIME OF LH SURGE AND OVULAT...

CHRONOLOGICAL RELATIONSHIPS BETWEEN ESTRUS ONSET, TIME OF LH SURGE AND OVULAT...International Journal of Technical Research & Application
The abnormal condition of electrical activity of
the heart given by ECG (Electrocardiogram) shows the cardiac
diseases affecting the human being. The P, QRS, T wave shape,
amplitude and time intervals between its various peaks contains
useful information about the nature of disease.
This paper presents wavelet technique to analyze ECG signal.
Discrete Wavelet Transform (DWT) is employed as noise
removal and feature extraction tool to achieve efficient design.
Daubechies wavelet of order 10 has been designed using Verilog
Hardware Description Language (HDL) and ModelSim Altera
6.4a is used as simulator. MIT-BIH database has been used for
the analysisANALYSIS OF ECG WITH DB10 WAVELET USING VERILOG HDL

ANALYSIS OF ECG WITH DB10 WAVELET USING VERILOG HDLInternational Journal of Technical Research & Application
The software industry has had significant progress
in recent years. The entire life of software includes two phases:
Production and Maintenance. Software maintenance cost is
increasingly growing and estimates showed that about 90%, if
software life cost is related to its maintenance phase. Extraction
and considering the factors affecting software maintenance cost
help to estimate the cost and reduce it by controlling the factors.
Cost estimation of maintenance phase is necessary to predict the
reliability, improve the productivity, project planning, controlling
and adaptability of the software. Though there are various models
to estimate the maintenance cost of traditional software like
COCOMO, SLIM, Function Point etc., but till now there is no
such model to estimate the maintenance cost using fourth
generation language environment. Software maintenance will
continue to exist in the fourth generation environment, as systems
will still be required to evolve. In this kind of situation there is
needed to develop a model to estimate the maintenance cost using
fourth generation environment. We propose a systematic
approach and development for software maintenance cost
estimation model using fourth generation language environment
on the basis of COCOMO II. This model is based on three
parameters: SMCE with Fourth Generation Language
Environment, ACT (Annual Change Traffic), Technical and NonTechnical
factors which affect the maintenance cost. The
favorable results closely matching and it can be achieved by using
model implementation.
DEVELOPMENT OF A SOFTWARE MAINTENANCE COST ESTIMATION MODEL: 4 TH GL PERSPECTIVE

DEVELOPMENT OF A SOFTWARE MAINTENANCE COST ESTIMATION MODEL: 4 TH GL PERSPECTIVEInternational Journal of Technical Research & Application
Protecting the private data from publishing has
become a requisite in today's world of data. This solves the
problem of divulging the sensitive data when it is mined.
Amongst the prevailing privacy models, ϵ-differential privacy
outfits one of the strongest privacy guarantees. In this paper,
we address the problem of private data publishing on vertically
partitioned data, where different attributes exist for same set of
individuals. This operation is simulated between two parties. In
specific, we present an algorithm with differentially private
data release for vertically partitioned data between two parties
in the semi-honest adversary model. First step towards
achieving this is to present a two party protocol for exponential
mechanism. By the same token, a two-party algorithm that
releases differentially private data in a secure way following
secure multiparty computation is implemented. A set of
investigational results on the real-life data indicate that the
proposed algorithm can effectively safeguard the information
for a data mining task.ϵ-DIFFERENTIAL PRIVACY MODEL FOR VERTICALLY PARTITIONED DATA TO SECURE THE PR...

ϵ-DIFFERENTIAL PRIVACY MODEL FOR VERTICALLY PARTITIONED DATA TO SECURE THE PR...International Journal of Technical Research & Application
Mais conteúdo relacionado
Destaque
IMPROVEMENT OF SUPPLY CHAIN MANAGEMENT BY MATHEMATICAL PROGRAMMING APPROACHIMPROVEMENT OF SUPPLY CHAIN MANAGEMENT BY MATHEMATICAL PROGRAMMING APPROACH

IMPROVEMENT OF SUPPLY CHAIN MANAGEMENT BY MATHEMATICAL PROGRAMMING APPROACHInternational Journal of Technical Research & Application
- Nanoparticles NiFe2-xTbxO4 (x=0.00, 0.04, 0.08,
0.12) ferrite was prepared by solgel combution method. The
samples were characterized with X-ray diffraction and TEM
measurements. The effect of Tb3+ cations substitution on
structure of prepared nanoparticles was investigated. From the
analysis, the system was found to be inverse spinel cubic
structure. The lattice parameter (a) changes increases with Tb
doping content. Room temperature DC electrical resistivity
decreases. Dielectric properties have been studied in the
frequency range of 1 kHz to 5 MHz. Permittivity and tangent
loss (tanδ) decreases with the substitution of Tb3+ in parent
crystal structure.STRUCTURAL AND DIELECTRIC STUDIES OF TERBIUM SUBSTITUTED NICKEL FERRITE NANOP...

STRUCTURAL AND DIELECTRIC STUDIES OF TERBIUM SUBSTITUTED NICKEL FERRITE NANOP...International Journal of Technical Research & Application
- This experiment was conducted to study the
chronological relationships between estrus onset, time of LH
surge and ovulation time in does synchronized with chronogest
or CIDR. Forty six desert goats were divided into 2 groups (A,
and B). Induction of oestrous was carried out using
intravaginal sponges impregnated with 40 mg fluorgestone and
CIDR for group A and B respectively. At time of sponge or
CIDR removal, the animals were injected with 300IU eCG.
There was no significant difference in the estrus onset, estrous
duration, ovulation time and time of LH surge in does
synchronized with either chronogest or CIDR. Ovulation was
detected 54 hours post sponges or CIDR removal. LH surge
occurred 28 hours post removal of sponge or CIDR. No
significant difference was detected with regard to the time
taken from oestrus onset to ovulation time (25.4 and 23.5 hours
respectively). Also, there was no significant difference in the
time taken from LH surge to ovulation time in does
synchronized with chronogest and CIDR (25.6 and 25.3 hours)
respectively. In conclusion, findings observed pertaining to
estrous onset, time of ovulation and the time of onset of the LH
peak could be of value in timing AI or mating for maximum
conception in goat breeding programs when CIDR or sponges
were used with 300IU eCG.CHRONOLOGICAL RELATIONSHIPS BETWEEN ESTRUS ONSET, TIME OF LH SURGE AND OVULAT...

CHRONOLOGICAL RELATIONSHIPS BETWEEN ESTRUS ONSET, TIME OF LH SURGE AND OVULAT...International Journal of Technical Research & Application
The abnormal condition of electrical activity of
the heart given by ECG (Electrocardiogram) shows the cardiac
diseases affecting the human being. The P, QRS, T wave shape,
amplitude and time intervals between its various peaks contains
useful information about the nature of disease.
This paper presents wavelet technique to analyze ECG signal.
Discrete Wavelet Transform (DWT) is employed as noise
removal and feature extraction tool to achieve efficient design.
Daubechies wavelet of order 10 has been designed using Verilog
Hardware Description Language (HDL) and ModelSim Altera
6.4a is used as simulator. MIT-BIH database has been used for
the analysisANALYSIS OF ECG WITH DB10 WAVELET USING VERILOG HDL

ANALYSIS OF ECG WITH DB10 WAVELET USING VERILOG HDLInternational Journal of Technical Research & Application
The software industry has had significant progress
in recent years. The entire life of software includes two phases:
Production and Maintenance. Software maintenance cost is
increasingly growing and estimates showed that about 90%, if
software life cost is related to its maintenance phase. Extraction
and considering the factors affecting software maintenance cost
help to estimate the cost and reduce it by controlling the factors.
Cost estimation of maintenance phase is necessary to predict the
reliability, improve the productivity, project planning, controlling
and adaptability of the software. Though there are various models
to estimate the maintenance cost of traditional software like
COCOMO, SLIM, Function Point etc., but till now there is no
such model to estimate the maintenance cost using fourth
generation language environment. Software maintenance will
continue to exist in the fourth generation environment, as systems
will still be required to evolve. In this kind of situation there is
needed to develop a model to estimate the maintenance cost using
fourth generation environment. We propose a systematic
approach and development for software maintenance cost
estimation model using fourth generation language environment
on the basis of COCOMO II. This model is based on three
parameters: SMCE with Fourth Generation Language
Environment, ACT (Annual Change Traffic), Technical and NonTechnical
factors which affect the maintenance cost. The
favorable results closely matching and it can be achieved by using
model implementation.
DEVELOPMENT OF A SOFTWARE MAINTENANCE COST ESTIMATION MODEL: 4 TH GL PERSPECTIVE

DEVELOPMENT OF A SOFTWARE MAINTENANCE COST ESTIMATION MODEL: 4 TH GL PERSPECTIVEInternational Journal of Technical Research & Application
Protecting the private data from publishing has
become a requisite in today's world of data. This solves the
problem of divulging the sensitive data when it is mined.
Amongst the prevailing privacy models, ϵ-differential privacy
outfits one of the strongest privacy guarantees. In this paper,
we address the problem of private data publishing on vertically
partitioned data, where different attributes exist for same set of
individuals. This operation is simulated between two parties. In
specific, we present an algorithm with differentially private
data release for vertically partitioned data between two parties
in the semi-honest adversary model. First step towards
achieving this is to present a two party protocol for exponential
mechanism. By the same token, a two-party algorithm that
releases differentially private data in a secure way following
secure multiparty computation is implemented. A set of
investigational results on the real-life data indicate that the
proposed algorithm can effectively safeguard the information
for a data mining task.ϵ-DIFFERENTIAL PRIVACY MODEL FOR VERTICALLY PARTITIONED DATA TO SECURE THE PR...

ϵ-DIFFERENTIAL PRIVACY MODEL FOR VERTICALLY PARTITIONED DATA TO SECURE THE PR...International Journal of Technical Research & Application
Destaque (20)
IMPROVEMENT OF SUPPLY CHAIN MANAGEMENT BY MATHEMATICAL PROGRAMMING APPROACH

IMPROVEMENT OF SUPPLY CHAIN MANAGEMENT BY MATHEMATICAL PROGRAMMING APPROACH
STRUCTURAL AND DIELECTRIC STUDIES OF TERBIUM SUBSTITUTED NICKEL FERRITE NANOP...

STRUCTURAL AND DIELECTRIC STUDIES OF TERBIUM SUBSTITUTED NICKEL FERRITE NANOP...
CHRONOLOGICAL RELATIONSHIPS BETWEEN ESTRUS ONSET, TIME OF LH SURGE AND OVULAT...

CHRONOLOGICAL RELATIONSHIPS BETWEEN ESTRUS ONSET, TIME OF LH SURGE AND OVULAT...
ANALYSIS OF ECG WITH DB10 WAVELET USING VERILOG HDL

ANALYSIS OF ECG WITH DB10 WAVELET USING VERILOG HDL
DEVELOPMENT OF A SOFTWARE MAINTENANCE COST ESTIMATION MODEL: 4 TH GL PERSPECTIVE

DEVELOPMENT OF A SOFTWARE MAINTENANCE COST ESTIMATION MODEL: 4 TH GL PERSPECTIVE
ϵ-DIFFERENTIAL PRIVACY MODEL FOR VERTICALLY PARTITIONED DATA TO SECURE THE PR...

ϵ-DIFFERENTIAL PRIVACY MODEL FOR VERTICALLY PARTITIONED DATA TO SECURE THE PR...
UNIVERSIDAD METROPOLITANA
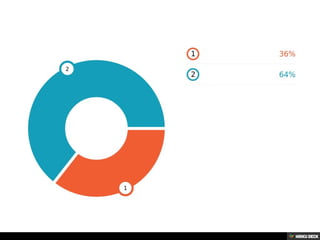
- 1. Bar chart Data point: 42 Data point: 76
