Security in Pervasive Computing Environments
•
0 gostou•388 visualizações
a brief presentation on several approaches to managing security in pervasive computing environments. Won\'t make any damn sense without my notes, which are: not attached
Denunciar
Compartilhar
Denunciar
Compartilhar
Baixar para ler offline
Recomendados
Mais conteúdo relacionado
Destaque
Destaque (15)
2011 June - Singapore GTUG presentation. App Engine program update + intro to Go

2011 June - Singapore GTUG presentation. App Engine program update + intro to Go
2011 aug-gdd-mexico-city-high-replication-datastore

2011 aug-gdd-mexico-city-high-replication-datastore
Rapid web development using tornado web and mongodb

Rapid web development using tornado web and mongodb
Semelhante a Security in Pervasive Computing Environments
Cryptography is where security engineering meets mathematics.The field of studyrelated to encoded
information comes from Greek word for ”secret writing” is cryptography.The art and science of hiding information
by embedding it in some otherdata is Steganography. The secret communication is carried through many
sourceslike image, audio and video files. This technique mainly proposes data hiding by embeddingthe message of
interest using geometric style of cryptographic algorithm,thus providing high security. Wavelet transform
algorithms are used to perform preprocessing of images.
Keywords —Cryptography, Steganography, Geometrical way of embedding, Wavelet transforms,DCT[IJET-V1I6P4] Authors: Bhatia Shradha, Doshi Jaina,Jadhav Preeti, Shah Nikita![[IJET-V1I6P4] Authors: Bhatia Shradha, Doshi Jaina,Jadhav Preeti, Shah Nikita](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[IJET-V1I6P4] Authors: Bhatia Shradha, Doshi Jaina,Jadhav Preeti, Shah Nikita](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[IJET-V1I6P4] Authors: Bhatia Shradha, Doshi Jaina,Jadhav Preeti, Shah NikitaIJET - International Journal of Engineering and Techniques
Semelhante a Security in Pervasive Computing Environments (20)
VINT Symposium 2012: Recorded Future | Luciano Floridi

VINT Symposium 2012: Recorded Future | Luciano Floridi
2020-04-29 SIT Insights in Technology - Serguei Beloussov

2020-04-29 SIT Insights in Technology - Serguei Beloussov
[IJET-V1I6P4] Authors: Bhatia Shradha, Doshi Jaina,Jadhav Preeti, Shah Nikita![[IJET-V1I6P4] Authors: Bhatia Shradha, Doshi Jaina,Jadhav Preeti, Shah Nikita](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[IJET-V1I6P4] Authors: Bhatia Shradha, Doshi Jaina,Jadhav Preeti, Shah Nikita](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[IJET-V1I6P4] Authors: Bhatia Shradha, Doshi Jaina,Jadhav Preeti, Shah Nikita
ICIS Final Panel - The Rise of ICT-distributed collective intelligence

ICIS Final Panel - The Rise of ICT-distributed collective intelligence
Último
Enterprise Knowledge’s Urmi Majumder, Principal Data Architecture Consultant, and Fernando Aguilar Islas, Senior Data Science Consultant, presented "Driving Behavioral Change for Information Management through Data-Driven Green Strategy" on March 27, 2024 at Enterprise Data World (EDW) in Orlando, Florida.
In this presentation, Urmi and Fernando discussed a case study describing how the information management division in a large supply chain organization drove user behavior change through awareness of the carbon footprint of their duplicated and near-duplicated content, identified via advanced data analytics. Check out their presentation to gain valuable perspectives on utilizing data-driven strategies to influence positive behavioral shifts and support sustainability initiatives within your organization.
In this session, participants gained answers to the following questions:
- What is a Green Information Management (IM) Strategy, and why should you have one?
- How can Artificial Intelligence (AI) and Machine Learning (ML) support your Green IM Strategy through content deduplication?
- How can an organization use insights into their data to influence employee behavior for IM?
- How can you reap additional benefits from content reduction that go beyond Green IM?
Driving Behavioral Change for Information Management through Data-Driven Gree...

Driving Behavioral Change for Information Management through Data-Driven Gree...Enterprise Knowledge
💉💊+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHABI}}+971581248768
+971581248768 Mtp-Kit (500MG) Prices » Dubai [(+971581248768**)] Abortion Pills For Sale In Dubai, UAE, Mifepristone and Misoprostol Tablets Available In Dubai, UAE CONTACT DR.Maya Whatsapp +971581248768 We Have Abortion Pills / Cytotec Tablets /Mifegest Kit Available in Dubai, Sharjah, Abudhabi, Ajman, Alain, Fujairah, Ras Al Khaimah, Umm Al Quwain, UAE, Buy cytotec in Dubai +971581248768''''Abortion Pills near me DUBAI | ABU DHABI|UAE. Price of Misoprostol, Cytotec” +971581248768' Dr.DEEM ''BUY ABORTION PILLS MIFEGEST KIT, MISOPROTONE, CYTOTEC PILLS IN DUBAI, ABU DHABI,UAE'' Contact me now via What's App…… abortion Pills Cytotec also available Oman Qatar Doha Saudi Arabia Bahrain Above all, Cytotec Abortion Pills are Available In Dubai / UAE, you will be very happy to do abortion in Dubai we are providing cytotec 200mg abortion pill in Dubai, UAE. Medication abortion offers an alternative to Surgical Abortion for women in the early weeks of pregnancy. We only offer abortion pills from 1 week-6 Months. We then advise you to use surgery if its beyond 6 months. Our Abu Dhabi, Ajman, Al Ain, Dubai, Fujairah, Ras Al Khaimah (RAK), Sharjah, Umm Al Quwain (UAQ) United Arab Emirates Abortion Clinic provides the safest and most advanced techniques for providing non-surgical, medical and surgical abortion methods for early through late second trimester, including the Abortion By Pill Procedure (RU 486, Mifeprex, Mifepristone, early options French Abortion Pill), Tamoxifen, Methotrexate and Cytotec (Misoprostol). The Abu Dhabi, United Arab Emirates Abortion Clinic performs Same Day Abortion Procedure using medications that are taken on the first day of the office visit and will cause the abortion to occur generally within 4 to 6 hours (as early as 30 minutes) for patients who are 3 to 12 weeks pregnant. When Mifepristone and Misoprostol are used, 50% of patients complete in 4 to 6 hours; 75% to 80% in 12 hours; and 90% in 24 hours. We use a regimen that allows for completion without the need for surgery 99% of the time. All advanced second trimester and late term pregnancies at our Tampa clinic (17 to 24 weeks or greater) can be completed within 24 hours or less 99% of the time without the need surgery. The procedure is completed with minimal to no complications. Our Women's Health Center located in Abu Dhabi, United Arab Emirates, uses the latest medications for medical abortions (RU-486, Mifeprex, Mifegyne, Mifepristone, early options French abortion pill), Methotrexate and Cytotec (Misoprostol). The safety standards of our Abu Dhabi, United Arab Emirates Abortion Doctors remain unparalleled. They consistently maintain the lowest complication rates throughout the nation. Our Physicians and staff are always available to answer questions and care for women in one of the most difficult times in their lives. The decision to have an abortion at the Abortion Cl+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...

+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...?#DUbAI#??##{{(☎️+971_581248768%)**%*]'#abortion pills for sale in dubai@
Último (20)
Driving Behavioral Change for Information Management through Data-Driven Gree...

Driving Behavioral Change for Information Management through Data-Driven Gree...
Understanding Discord NSFW Servers A Guide for Responsible Users.pdf

Understanding Discord NSFW Servers A Guide for Responsible Users.pdf
Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...

Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...
+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...

+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...
Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...

Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...
[2024]Digital Global Overview Report 2024 Meltwater.pdf![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[2024]Digital Global Overview Report 2024 Meltwater.pdf
From Event to Action: Accelerate Your Decision Making with Real-Time Automation

From Event to Action: Accelerate Your Decision Making with Real-Time Automation
Advantages of Hiring UIUX Design Service Providers for Your Business

Advantages of Hiring UIUX Design Service Providers for Your Business
Tata AIG General Insurance Company - Insurer Innovation Award 2024

Tata AIG General Insurance Company - Insurer Innovation Award 2024
Apidays New York 2024 - Scaling API-first by Ian Reasor and Radu Cotescu, Adobe

Apidays New York 2024 - Scaling API-first by Ian Reasor and Radu Cotescu, Adobe
Boost Fertility New Invention Ups Success Rates.pdf

Boost Fertility New Invention Ups Success Rates.pdf
HTML Injection Attacks: Impact and Mitigation Strategies

HTML Injection Attacks: Impact and Mitigation Strategies
Security in Pervasive Computing Environments
- 1. Bruce Sterling, When Blobjects Rule The Earth, SIGGRAPH, Los Angeles, 2004 retreived 18/08/08, from http://www.viridiandesign.org/notes/401-450/00422_the_spime.html
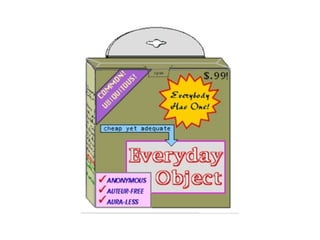
- 2. So, how do you deal with privacy concerns in a pervasive computing environment?
- 3. The Virtual Wall model
- 4. Virtual Walls: Protecting Digital Privacy in Pervasive Environments A. Kapadia, T. Henderson, J.J. Fielding David Kotz Proceedings of the 5th International Conference on Pervasive Computing, number 4480 in LNCS, pages 162- 179, Toronto, Canada, May 2007. Springer-Verlag.
