West Chester Tech Training session 7
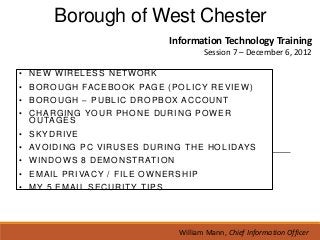
- 1. Borough of West Chester Information Technology Training Session 7 – December 6, 2012 • NEW WIRELESS NETWORK • B O R O U G H FA C E B O O K PA G E ( P O L I C Y R E V I E W ) • BOROUGH – PUBLIC DROPBOX ACCOUNT • CHARGING YOUR PHONE DURING POWER O U TA G E S • SKYDRIVE • AV O I D I N G P C V I R U S E S D U R I N G T H E H O L I D AY S • W I N D O W S 8 D E M O N S T R AT I O N • E M A I L P R I VA C Y / F I L E O W N E R S H I P • MY 5 EMAIL SECURITY TIPS William Mann, Chief Information Officer
- 2. New Wireless Network in Service A new “cloud based” wireless network is in service. Connecting your mobile devices has never been easier. There are 2 difference SSID’s available. A SSID is the name of a wireless local area network (WLAN). All wireless devices on a WLAN must employ the same SSID in order to communicate with each other. 1. “WC-Wireless” is available to all, including guests in the municipal building. The WAP (wireless access key) for this is 4016106962700. 2. “WC-Staff” will be in service shortly to authorized personnel only. This SSID will provide access to our LAN (local area network). http://tinyurl.com/wcboro2012 William Mann, Chief Information Officer
- 3. The Borough of West Chester – Public Dropbox Account The Borough of Chester now has a public Dropbox account. This account is available to anyone who would like access to Borough Council meeting agendas and supporting documents. http://tinyurl.com/wcboro2012 William Mann, Chief Information Officer
- 4. The Borough of West Chester’s official Facebook Page On October 1 we launched our official “Borough of West Chester” Facebook Page. The mission of our Facebook page is to increase the Borough’s presence on the internet and positively interact with out community and visitors. www.facebook.com/WestChesterBorough William Mann, Chief Information Officer
- 5. The Borough of West Chester’s official Facebook Page Facebook Policy Policy of Behavior • Profanity of any kind shall not be permitted on the webpage. • Statements and comments of a harassing or threatening nature shall not be permitted on the webpage. • Illegal activity of any type shall not be permitted on the webpage. • Comments singling out individual employees in a negative or unprofessional manner shall be removed. • Employees and other parties associated with the Borough of West Chester shall not engage in self-promotion. • Unauthorized photos of Borough of West Chester employees are strictly prohibited. William Mann, Chief Information Officer
- 6. The Borough of West Chester’s official Facebook Page Facebook Policy Policy of Behavior continued Any statements or comments of the above nature shall be removed immediately upon discovery by any of the Facebook administrators. Borough of West Chester employees involved in any activity of this nature shall be disciplined by the Borough Manager’s office. Persons who engage in any of the activities described in the “policy of behavior” are subject to being banned from the Borough of West Chester Facebook page. Responding to Comments Employees shall not engage in comments without the prior approval of their department manager. Only the original author of a posting shall respond to comments unless another staff member has been authorized by either the author or the department manager. William Mann, Chief Information Officer
- 7. The Borough of West Chester’s official Facebook Page Facebook Policy Dealing with Criticism One of the greatest fears by some professionals in respect to social media is “the fear of criticism”. Public employees are in the public eye and are supported by the tax payers they serve. Criticism on a professional level must be accepted and anticipated. Criticism on public social media websites of local government services is likely from time to time. If the criticism does not mention individual names of employees and does not violate the “policy of behavior” in Section II the comments shall not be deleted from the website. Should a criticism comment or statement violate the “policy of behavior” in section II the comments shall be removed immediately upon discovery by an administrator and the person making the comment banned from the webpage. Borough of West Chester – Administrative Policy for the Borough of West Chester The “Facebook Team” for the Borough of West Chester includes: Rich Ashenfelder – Department of Recreation – rashenfelder@west-chester.com Judy Benes – Borough Manager’s Office – jbenes@west-chester.com Kathy Brooks – Building & Housing – kbrooks@west-chester.com Meghan Fogarty – Department of Public Works – mfogarty@west-chester.com Jennifer Glick – Department of Finance – jglick@west-chester.com Staci King – Police Department – sking@west-chester.com William Mann – Chief Information Officer – wmann@west-chester.com Hector Mojica – Parking Services – hmojica@west-chester.com Kevin Oakes – Department of Wastewater – koakes@west-chester.com William Mann, Chief Information Officer
- 8. SkyDrive is Microsoft’s “cloud storage” solution which offers 8 GB of free storage in the cloud. I recommend SkyDrive because it easily connects your documents to Microsoft Office allowing you to work on your files regardless of where you are or what type of device you happen to be using. This will become especially true as Windows 8, followed by the upcoming Office 2013 become widely used. You can sign up for a free account at www.skydrive.live.com. William Mann, Chief Information Officer
- 9. Keeping Your PC & Your Information Safe During the Holidays
- 10. Keeping Your PC & Your Information Safe During the Holidays William Mann, Chief Information Officer
- 11. Keeping Your PC & Your Information Safe During the Holidays 2012 Cyber Monday continues the trend. William Mann, Chief Information Officer
- 13. Keeping Your PC & Your Information Safe During the Holidays 1. When shopping online only provide your confidential information to secure sites – as identified by starting with “https” or by viewing the padlock icon in the URL. 2. Consider using a credit card for online purchases as compared with a debit card. Credit cards typically carry limitations of liability (if noted within a reasonable period of time) compared with debit cards where inappropriate or unauthorized use may drain your personal checking account. Your credit card may also offer buyer protection for goods not delivered as compared with your debit card provider. 3. When shopping online, use a gift card or one-time use card that is limited in its value to near or at the amount of the purchase.
- 14. Keeping Your PC & Your Information Safe During the Holidays 4. Be on the lookout for fake (phishing) expeditions where mock websites are pretending to be your financial institution and requesting your personal banking information. 5. When you are using your debit or credit card at the mall or other crowded businesses, be careful of “shoulder surfers” who may be attempting to view your PIN as you type it into the reader. Maintain the anti-virus and anti-adware applications on your personal PC. 6. Be suspicious of on screen advertisements that direct you away from the site and business that you were intending to purchase from. William Mann, Chief Information Officer
- 15. Keeping Your PC & Your Information Safe During the Holidays 7. When in doubt, call the website contact number listed to help ensure you are doing business with a reputable company. Be wary of emails that you are not expecting – even from your friends, colleagues, and family members that contain a holiday greeting. 8. It is common for fraudsters to use address books of email accounts to resend messages to those in the address book, and these messages typically carry malware that is intended to do harm to your computer or glean personal information. 9. Delete “Chain” emails or greeting card emails which frequently carry malware that may place files on your computer unbeknownst to you that can damage your computer or send files or information to thieves. William Mann, Chief Information Officer
- 16. Keeping Your PC & Your Information Safe During the Holidays 10. Do not resend chain emails - even special holiday message emails to your friends, colleagues, or family members. Do not open attachments from emails that you are not expecting – even if it says “Ho-Ho-Ho” or another holiday greeting in the subject line. 11. Do not open attachments from emails that you are not expecting – even if it says “Ho-Ho-Ho” or another holiday greeting in the subject line. And finally and the most important of all… please use common sense. If it sounds to good to be true….. It probably is. William Mann, Chief Information Officer
- 17. Windows 8 Demonstration & Discussion Throughout 2013 you will here allot about the new Windows 8 operating system (OS). Windows 8 comes in 3 flavors. • Windows 8 RT • Windows 8 Pro • Windows 8 Enterprise* * The same as Pro with the exception of Windows Media Center William Mann, Chief Information Officer
- 18. Windows 8 Demonstration & Discussion Throughout 2013 you will here allot about the new Windows 8 operating system (OS). Windows 8 will operate on the following platforms. • PC • Tablets (RT or Pro) • Smartphones William Mann, Chief Information Officer
- 19. Know Your Email Risks and Rights The recent FBI General Petraeus Probe is a reminder that email we use is owned, managed and controlled by your employer. Even if you use your personal email on your organization’s equipment it is subject to search and seizure by your employer. All of this information can be used to hold you liable and end, even in your termination. Email messages while not the only thing that took down the top general in the United States government it played a very large part. William Mann, Chief Information Officer
- 20. 2 Simple Email Rules to Rule Them All I believe that 2 simple email rules will protect you from email trouble with your employer. 1. Never ever send any email message to anyone that you would not say “face to face” to that person. 1. Never ever send any email to anyone that you would not be embarrassed or ashamed of if someone else read it. Did you know? All of the email we send is “discoverable” regardless if it has been deleted or not. All of our email is archived. Once it is sent, it is owned by the Borough of West Chester. William Mann, Chief Information Officer
- 21. File Ownership The ongoing Pertraeus Probe should be a wake up call to everyone. • Any and all files that you create, edit or store on Borough property is owned by the Borough of West Chester and is subject to discovery. • Personal email that is created or stored on Borough property is subject to discovery. • The destruction or deletion of Borough documents and files is strictly restricted. • Employees may be disciplined or terminated for information resulting from discovery. What is Discovery? Discovery is the technical process of searching email and files. Through this process policy & procedure adherence is reviewed. William Mann, Chief Information Officer
- 22. My 5 Tips for Email Security While we are talking about email and before we proceed to the next slide let’s take a minute to look at this. William Mann, Chief Information Officer
- 23. My 5 Tips for Email Security 1. Don’t Write It Down. The first rule of communication is to do it in person if possible and in written form only if necessary. 2. Keep personal and professional communications separate. Email, Instant messages, text and photos that are personal need to be exchanged only using personal accounts & personal hardware. 3. Don’t trust even prominent Cloud providers to protect messages. E-mail services like Google’s are susceptible to hacking and there are well documented cases of users having accounts broken into, emails deleted and unauthorized messages sent. 4. Do not use Facebook as an email or texting service! 5. Remember that your information is only as safe as the recipient’s email or texting service. William Mann, Chief Information Officer
- 24. Do You Remember When Email was a BIG Deal? William Mann, Chief Information Officer
- 25. Thank You for Attending. Our next tech training will be in the Spring. In the meantime be sure to check out the West Chester Tech Blog. William Mann, Chief Information Officer
