The Secure Communicator: Best Practices for Surviving Heartbleed and Other Threats
Do you understand how you’ve been affected by the Heartbleed bug? Are you worried about maintaining your privacy online? (You should be.) Do you know how to best protect client or company information? Is it safe to use social media? Have you heard of ransomware? Are you worried about identity theft? Most technical communicators know that it’s important to secure their work and online presence, but many don’t know how to do it effectively. Good security can enable—not hinder—your work. Join the presenter as he discusses the steps you can take to adopt a security lifestyle that protects you and enables you to work effectively: Protecting your computer Protecting your reputation Protecting your information Protecting your identity Creating strong and memorable passwords Leveraging cool tools
Recomendados
Mais conteúdo relacionado
Mais de Ben Woelk, CISSP, CPTC
Mais de Ben Woelk, CISSP, CPTC (20)
Último
Último (20)
The Secure Communicator: Best Practices for Surviving Heartbleed and Other Threats
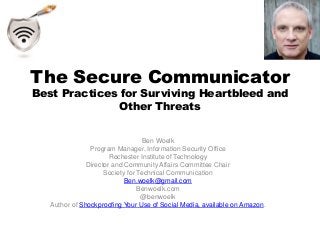
- 1. The Secure Communicator Best Practices for Surviving Heartbleed and Other Threats Ben Woelk Program Manager, Information Security Office Rochester Institute of Technology Director and Community Affairs Committee Chair Society for Technical Communication Ben.woelk@gmail.com Benwoelk.com @benwoelk Author of Shockproofing Your Use of Social Media, available on Amazon.
- 2. Why Worry?
- 3. Threat Landscape http://www.symantec.com/content/en/us/enterprise/images/security_response/SYM-ISTR- SMB-Infograph.jpg
- 9. Adopting a Security Mindset Inside the Twisted Mind of the Security Professional http://www.schneier.com/essay-210.html
- 11. The Basics • Anti-virus • Anti-spyware • Firewalls • Patching
- 15. Passwords
- 16. Passphrase It was a dark and stormy night becomes ItwasaDark215&StormyNight Length > complexity
- 17. Cool Tools • Google Dashboard • Browser Plugins – Netcraft – McAfee Site Advisor – Web of Trust (WoT) • Secunia PSI • Password Safes
- 18. Resources • Goodreads Cyber Security Library • https://www.goodreads.com/search?q=cyber+security+library • Infosec Communicator Blog benwoelk.com • Shockproofing Your Use of Social Media eBook
- 19. Questions (and Maybe Some Answers) Ben Woelk Ben.woelk@gmail.com Benwoelk.com @benwoelk www.linkedin.com/in/benwoelk/
Notas do Editor
- Because it’s getting dangerous out there!
- 2012 Symantec Internet Threat Report You’re vulnerable. What could they want from you? Anoynmizer Identity Theft, Corporate secrets
- Heartbleed Data from server memory was accessible on “secure” connections.
- Wonder Fu! What do I use it for? What could I use it for that wasn’t intended?
- Mail the ants
- Run down the basics
- Encrypted connections (VPN); SSL; trucrypt; encrypted USBs, hard drives. Encrypt dropbox. Correct addressing.
- What info are you posting about yourself. Use multiple passwords. Be careful on social networking sites.
- Reputation management services. Don’t know that they’re worth it. Keep pumping out good content. Google alerts.
- Password vaults. Don’t use the same password for multiple accounts.
- PSI—Personal Software Inspector
