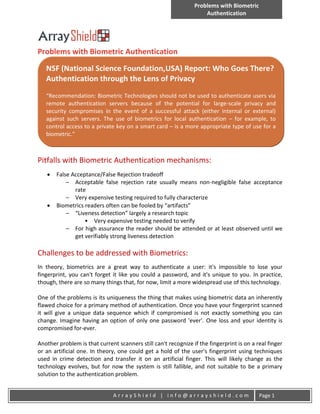
Problems with biometric authentication
- 1. Problems with Biometric Authentication Problems with Biometric Authentication NSF (National Science Foundation,USA) Report: Who Goes There? Authentication through the Lens of Privacy “Recommendation: Biometric Technologies should not be used to authenticate users via remote authentication servers because of the potential for large-scale privacy and security compromises in the event of a successful attack (either internal or external) against such servers. The use of biometrics for local authentication – for example, to control access to a private key on a smart card – is a more appropriate type of use for a biometric.” Pitfalls with Biometric Authentication mechanisms: False Acceptance/False Rejection tradeoff – Acceptable false rejection rate usually means non-negligible false acceptance rate – Very expensive testing required to fully characterize Biometrics readers often can be fooled by “artifacts” – “Liveness detection” largely a research topic • Very expensive testing needed to verify – For high assurance the reader should be attended or at least observed until we get verifiably strong liveness detection Challenges to be addressed with Biometrics: In theory, biometrics are a great way to authenticate a user: it's impossible to lose your fingerprint, you can't forget it like you could a password, and it's unique to you. In practice, though, there are so many things that, for now, limit a more widespread use of this technology. One of the problems is its uniqueness the thing that makes using biometric data an inherently flawed choice for a primary method of authentication. Once you have your fingerprint scanned it will give a unique data sequence which if compromised is not exactly something you can change. Imagine having an option of only one password 'ever'. One loss and your identity is compromised for-ever. Another problem is that current scanners still can't recognize if the fingerprint is on a real finger or an artificial one. In theory, one could get a hold of the user's fingerprint using techniques used in crime detection and transfer it on an artificial finger. This will likely change as the technology evolves, but for now the system is still fallible, and not suitable to be a primary solution to the authentication problem. ArrayShield | info@arrayshield.com Page 1
