Salander v bond 2600
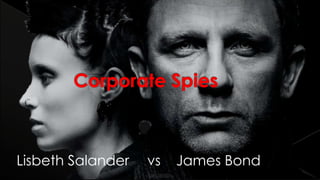
- 1. Lisbeth Salander vs James Bond
- 2. The 4 principal motivators of betrayals Espionage Tactics Famous Spies in History
- 3. Every fortune 500 organization has an intelligence program under some other title › Competitive intelligence, corporate intel, business analysis Corporate spies are almost never caught, and almost never convicted, and never serve more than 1 year in a “corporate spy” prison.
- 4. MI6 operative Relies on Humans as sources of intel Somehow explodes everything Makes love to pretty ladies
- 5. Works as a PI Socially unacceptable Intelligence comes through technical means Also makes love to pretty ladies
- 6. Government Employees: › CIA, Marines, Homeland security › Provide intel and counter intel services Corporate Competitive Intelligence employees › Work for an organization to provide intel on their competitors › Mostly ethical practices Private Corporate Spies › Individuals or private organizations that sell secrets between companies › Focused, well paid, completely illegal
- 8. Break into network steal documents Phishing campaign steals creds Malware targeting a company
- 9. BenefitsCosts Direct unfettered access to intelligence No middlemen Limited risk of inflation, lying Lower risk of being caught More defense measures are in place compared to HUMINT Clearly defined laws regarding IP, hacking, etc
- 10. Turning a secretary to tell you who the CEO is meeting with Paying a VP for financial information Convincing a QA dept to give you access to products
- 11. BenefitsCosts Information directly from the source Can be the “fall guy” Can circumvent any network security measures Context for intelligence The most sensitive information is in small circles Possibility for betrayal, lying, or inflating information Humans need coddling
- 12. Money: I will pay you $50,000. Ideology: Do it for the greater good of your country! Coersion: If you don’t do this, your wife will find out about your mistress. Ego: I’ve been watching you and you’re the best in the business. I need your help.
- 14. Peter is going through a divorce Alex – Russian spy – hangs out in bars and coffee shops near targeted areas of DC Alex becomes Peter’s friend over 2 months Alex pays Peter for phone number of people inside his company Tradecraft: › Used pass phrases to leave messages and confirm the identity while trading information › Make a chalk mark on the mailbox Alex gets one of his other ops to exchange information about “Star Wars” Peter social engineers an IT admin fixing the wiring closet Peter steals the documents off the network and exfiltrates it back to Moscow
- 15. Primary Motivator: Money Spies are friendly Tradecraft › Chalk mailbox › Pass phrases
- 17. Started working for AMD in 1979 Walks up to the Cuban embassy in 1982 and says “I want to be spy” 1989 communism is boring 1992 he turns himself into the CIA becomes a double agent 1992 he goes to work for Intel 1994 he flies to South America and sells Pentium secrets Tries to sell the secrets to North Korea, China, Iran, and AMD
- 18. Walked around picking up random documents and photo copying them Used lots of photo copiers so security would never notice Guards only looked for green or blue paper Charismatic › Access to new tech was just because his friends gave it to him › Offered to do favors for everyone › Always befriended secretaries
- 19. Primary Motivation: Ideology Good employees make good spies Security theatre
Notas do Editor
- Side affect is your girlfriend will appreciate it
- 5/14/2013 – 45 minutes long (without specific opsec stuff) http://www.slideshare.net/earl675/corporate-espionage 5/23/2013 – 50-55 minutes long. Skipping last parts
- 53 minutes long – spoke very fast 46 mins – spoke kind of fast. Some slides didn’t flow. 58 minutes – spoke slowly but well. … need to shorten.. 48 minutes – out of breath, kind of a good pace though. Spoke too loudly and high 44 minutes – good speed. Not out of breath. Ready to go