What is a Rainbow Table?
•Transferir como PPTX, PDF•
2 gostaram•6,058 visualizações
this presentation introduces you an advanced way of decryption of data
Denunciar
Compartilhar
Denunciar
Compartilhar
Recomendados
Mais conteúdo relacionado
Mais procurados
Mais procurados (20)
Destaque
Destaque (11)
Password Storage And Attacking In PHP - PHP Argentina

Password Storage And Attacking In PHP - PHP Argentina
Mais de Vahid Saffarian
Mais de Vahid Saffarian (12)
Último
Último (20)
Future Visions: Predictions to Guide and Time Tech Innovation, Peter Udo Diehl

Future Visions: Predictions to Guide and Time Tech Innovation, Peter Udo Diehl
UiPath Test Automation using UiPath Test Suite series, part 1

UiPath Test Automation using UiPath Test Suite series, part 1
Behind the Scenes From the Manager's Chair: Decoding the Secrets of Successfu...

Behind the Scenes From the Manager's Chair: Decoding the Secrets of Successfu...
Intro in Product Management - Коротко про професію продакт менеджера

Intro in Product Management - Коротко про професію продакт менеджера
Extensible Python: Robustness through Addition - PyCon 2024

Extensible Python: Robustness through Addition - PyCon 2024
SOQL 201 for Admins & Developers: Slice & Dice Your Org’s Data With Aggregate...

SOQL 201 for Admins & Developers: Slice & Dice Your Org’s Data With Aggregate...
How Red Hat Uses FDO in Device Lifecycle _ Costin and Vitaliy at Red Hat.pdf

How Red Hat Uses FDO in Device Lifecycle _ Costin and Vitaliy at Red Hat.pdf
FDO for Camera, Sensor and Networking Device – Commercial Solutions from VinC...

FDO for Camera, Sensor and Networking Device – Commercial Solutions from VinC...
ASRock Industrial FDO Solutions in Action for Industrial Edge AI _ Kenny at A...

ASRock Industrial FDO Solutions in Action for Industrial Edge AI _ Kenny at A...
Powerful Start- the Key to Project Success, Barbara Laskowska

Powerful Start- the Key to Project Success, Barbara Laskowska
Secure Zero Touch enabled Edge compute with Dell NativeEdge via FDO _ Brad at...

Secure Zero Touch enabled Edge compute with Dell NativeEdge via FDO _ Brad at...
What is a Rainbow Table?
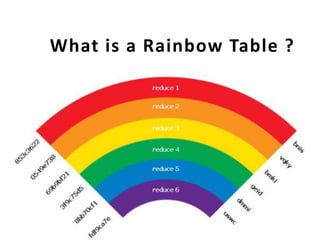
- 1. What is a Rainbow Table ?
- 2. A rainbow table is a precomputed table for reversing cryptographic hash functions, usually for cracking password hashes.
- 3. Tables are usually used in recovering a plaintext password up to a certain length consisting of a limited set of characters.
- 4. It is a practical example of a space/time trade- off, using more computer processing time at the cost of less storage when calculating a hash on every attempt, or less processing time and more storage when compared to a simple lookup table with one entry per hash.
- 6. Use of a key derivation function that employs a salt makes this attack infeasible.
- 7. Rainbow tables are an application of an earlier, simpler algorithm by Martin Hellman
