diagram_sources.pptx
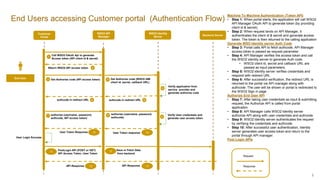
- 1. 1 End Users accessing Customer portal (Authentication Flow) Customer Portal 1 3 Call WSO2 OAuth Api to generate Access token (API client id & secret) Return WSO2 API access token WSO2 API Manager WSO2 Identity Server authcode in redirect URL 4 , Verify application from service provider and generate authorize code authcode in redirect URL End User 5 Get Authorize code (WSO2 IAM client id, secret, callback URL) User Login Success Response Request Get Authorize code (API access token) 2 6 6 7 authorize (username, password, authcode, API access token) 8 authorize (username, password, authcode) User Token response Verify User credentials and generate user access token 9 PostLogin API (POST or GET) API Access Token, User Token Backend Server User Token Response 13 Save or Fetch Data from backend API Response 10 API Response Machine To Machine Authentication (Token API) • Step 1: When portal starts, the application will call WSO2 API Manager OAuth API to generate token (by providing client id & secret). • Step 2: When request lands on API Manager, it authenticates the client id & secret and generate access token. The token is then returned to the calling application Generate WSO Identity server Auth Code • Step 3: Portal calls API to fetch authcode. API Manager access token is passed as request parameter. • Step 4: API Manager verifies the access token and call the WSO2 identity server to generate Auth code. • WSO2 client id, secret and callback URL are passed as input parameters. • Step 5: WSO2 identity server verifies credentials and respond with redirect URL • Step 6: After successful verification, the redirect URL is returned to the portal via API manager along with authcode. The user will be shown or portal is redirected to the WSO2 Sign in page Authorize End User API • Step 7: After taking user credentials as input & submitting request, the Authorize API is called from portal application. • Step 8: API Manager calls WSO2 Identity server authorize API along with user credentials and authcode. • Step 9: WSO2 Identity server authenticates the request by verifying the credentials and authcode. • Step 10: After successful user authentication, Identity server generates user access token and return to the portal through API manager. Post Login APIs 10 11 12 13