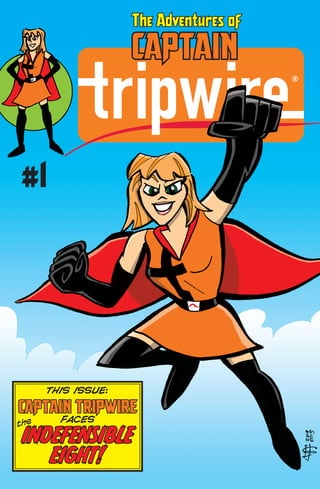
The Adventures of Captain Tripwire #1: Captain Tripwire Faces the Indefensible Eight!
•
1 gostou•1,833 visualizações
The Adventures of Captain Tripwire #1: Captain Tripwire Faces the Indefensible Eight!
Denunciar
Compartilhar
Denunciar
Compartilhar
Recomendados
We shared our landing page in a few Facebook groups to test our startup idea and gain feedbacks. In the next days we ended up on Product Hunt, Fast Company and Gizmodo. We weren't ready for it and ... we'd like to share with you what we learned during the unplanned launch of Earlyclaim.comUnplanned startup launch: Product Hunt vs Fast Company vs Gizmodo. Source eff...

Unplanned startup launch: Product Hunt vs Fast Company vs Gizmodo. Source eff...Alessandro Marchesini
Recomendados
We shared our landing page in a few Facebook groups to test our startup idea and gain feedbacks. In the next days we ended up on Product Hunt, Fast Company and Gizmodo. We weren't ready for it and ... we'd like to share with you what we learned during the unplanned launch of Earlyclaim.comUnplanned startup launch: Product Hunt vs Fast Company vs Gizmodo. Source eff...

Unplanned startup launch: Product Hunt vs Fast Company vs Gizmodo. Source eff...Alessandro Marchesini
Mais conteúdo relacionado
Mais de Tripwire
Mais de Tripwire (20)
Tripwire Energy Working Group: Keynote w/Patrick Miller 

Tripwire Energy Working Group: Keynote w/Patrick Miller
World Book Day: Cybersecurity’s Quietest Celebration

World Book Day: Cybersecurity’s Quietest Celebration
Tripwire Retail Security 2020 Survey: Key Findings

Tripwire Retail Security 2020 Survey: Key Findings
Key Findings: Tripwire COVID-19 Cybersecurity Impact Report

Key Findings: Tripwire COVID-19 Cybersecurity Impact Report
The Adventures of Captain Tripwire: Coloring Book!

The Adventures of Captain Tripwire: Coloring Book!
Industrial Cybersecurity: Practical Tips for IT & OT Collaboration

Industrial Cybersecurity: Practical Tips for IT & OT Collaboration
A Look Back at 2018: The Most Memorable Cyber Moments

A Look Back at 2018: The Most Memorable Cyber Moments
Time for Your Compliance Check-Up: How Mercy Health Uses Tripwire to Pass Audits

Time for Your Compliance Check-Up: How Mercy Health Uses Tripwire to Pass Audits
Tripwire State of Cyber Hygiene 2018 Report: Key Findings

Tripwire State of Cyber Hygiene 2018 Report: Key Findings
Defend Your Data Now with the MITRE ATT&CK Framework

Defend Your Data Now with the MITRE ATT&CK Framework
Defending Critical Infrastructure Against Cyber Attacks

Defending Critical Infrastructure Against Cyber Attacks
Jumpstarting Your Cyberdefense Machine with the CIS Controls V7

Jumpstarting Your Cyberdefense Machine with the CIS Controls V7
Hunting for Cyber Threats Using Threat Modeling & Frameworks 

Hunting for Cyber Threats Using Threat Modeling & Frameworks
Most RSAC Attendees Favor Shorter Vulnerability Disclosure Timelines

Most RSAC Attendees Favor Shorter Vulnerability Disclosure Timelines
Protecting Your POS Systems from the Next Big Ransomware Threat

Protecting Your POS Systems from the Next Big Ransomware Threat
2017 in Review: Infosec Pros Look Back on the Year

2017 in Review: Infosec Pros Look Back on the Year
Último
Último (20)
DEV meet-up UiPath Document Understanding May 7 2024 Amsterdam

DEV meet-up UiPath Document Understanding May 7 2024 Amsterdam
Spring Boot vs Quarkus the ultimate battle - DevoxxUK

Spring Boot vs Quarkus the ultimate battle - DevoxxUK
Apidays New York 2024 - The value of a flexible API Management solution for O...

Apidays New York 2024 - The value of a flexible API Management solution for O...
"I see eyes in my soup": How Delivery Hero implemented the safety system for ...

"I see eyes in my soup": How Delivery Hero implemented the safety system for ...
Web Form Automation for Bonterra Impact Management (fka Social Solutions Apri...

Web Form Automation for Bonterra Impact Management (fka Social Solutions Apri...
Polkadot JAM Slides - Token2049 - By Dr. Gavin Wood

Polkadot JAM Slides - Token2049 - By Dr. Gavin Wood
Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME

Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME
How to Troubleshoot Apps for the Modern Connected Worker

How to Troubleshoot Apps for the Modern Connected Worker
Axa Assurance Maroc - Insurer Innovation Award 2024

Axa Assurance Maroc - Insurer Innovation Award 2024
Modular Monolith - a Practical Alternative to Microservices @ Devoxx UK 2024

Modular Monolith - a Practical Alternative to Microservices @ Devoxx UK 2024
Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff

Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff
Why Teams call analytics are critical to your entire business

Why Teams call analytics are critical to your entire business
Navigating the Deluge_ Dubai Floods and the Resilience of Dubai International...

Navigating the Deluge_ Dubai Floods and the Resilience of Dubai International...
The Adventures of Captain Tripwire #1: Captain Tripwire Faces the Indefensible Eight!
- 1. CAPTAIN The Adventures of #1 THIS ISSUE: CAPTAIN TRIPWIRE FACES INDEFENSIBLE EIGHT! the
- 2. ALL NODES LEAD TO TRIPWIRE Gain total visibility across your IT/OT environment www.tripwire.com
