Document Security
•
0 gostou•37 visualizações
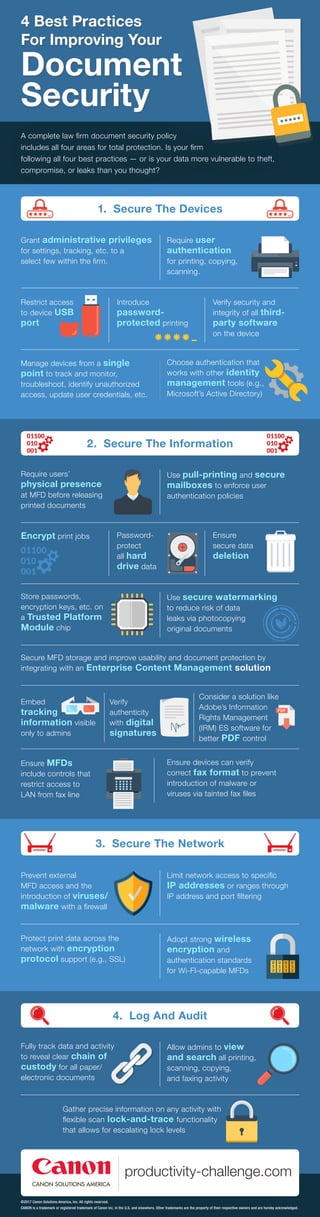
If you are securing documents or intellectual properties everyone should understand how to secure it right and how to restrict certain users.
Denunciar
Compartilhar
Denunciar
Compartilhar
Baixar para ler offline
Recomendados
Recomendados
Mais conteúdo relacionado
Mais procurados
Mais procurados (20)
Security and control in Management Information System

Security and control in Management Information System
Mitre ATT&CK and the Mueller GRU Indictment: Lessons for Organizations

Mitre ATT&CK and the Mueller GRU Indictment: Lessons for Organizations
Semelhante a Document Security
Semelhante a Document Security (20)
Typical system servicesProgram executionIO operationsFile Sy.pdf

Typical system servicesProgram executionIO operationsFile Sy.pdf
Wave 14 - Winodws 7 Security Story Core by MVP Azra Rizal

Wave 14 - Winodws 7 Security Story Core by MVP Azra Rizal
Sallysspecialservices networksecurityproposal2-100305141834-phpapp02

Sallysspecialservices networksecurityproposal2-100305141834-phpapp02
Enterprise Digital Rights Management (Persistent Security)

Enterprise Digital Rights Management (Persistent Security)
Primend praktiline konverents - Office 365 turvalisus

Primend praktiline konverents - Office 365 turvalisus
Mais de Tim O'Leary
Mais de Tim O'Leary (20)
Adopting a 'One Boat' Mindset Will Help with Organizational Change

Adopting a 'One Boat' Mindset Will Help with Organizational Change
Último
Último (20)
Axa Assurance Maroc - Insurer Innovation Award 2024

Axa Assurance Maroc - Insurer Innovation Award 2024
Apidays New York 2024 - The Good, the Bad and the Governed by David O'Neill, ...

Apidays New York 2024 - The Good, the Bad and the Governed by David O'Neill, ...
2024: Domino Containers - The Next Step. News from the Domino Container commu...

2024: Domino Containers - The Next Step. News from the Domino Container commu...
Apidays New York 2024 - Accelerating FinTech Innovation by Vasa Krishnan, Fin...

Apidays New York 2024 - Accelerating FinTech Innovation by Vasa Krishnan, Fin...
Apidays New York 2024 - The value of a flexible API Management solution for O...

Apidays New York 2024 - The value of a flexible API Management solution for O...
Apidays New York 2024 - Scaling API-first by Ian Reasor and Radu Cotescu, Adobe

Apidays New York 2024 - Scaling API-first by Ian Reasor and Radu Cotescu, Adobe
Connector Corner: Accelerate revenue generation using UiPath API-centric busi...

Connector Corner: Accelerate revenue generation using UiPath API-centric busi...
Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff

Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff
Emergent Methods: Multi-lingual narrative tracking in the news - real-time ex...

Emergent Methods: Multi-lingual narrative tracking in the news - real-time ex...
Spring Boot vs Quarkus the ultimate battle - DevoxxUK

Spring Boot vs Quarkus the ultimate battle - DevoxxUK
Apidays New York 2024 - Passkeys: Developing APIs to enable passwordless auth...

Apidays New York 2024 - Passkeys: Developing APIs to enable passwordless auth...
Apidays New York 2024 - APIs in 2030: The Risk of Technological Sleepwalk by ...

Apidays New York 2024 - APIs in 2030: The Risk of Technological Sleepwalk by ...
How to Troubleshoot Apps for the Modern Connected Worker

How to Troubleshoot Apps for the Modern Connected Worker
DEV meet-up UiPath Document Understanding May 7 2024 Amsterdam

DEV meet-up UiPath Document Understanding May 7 2024 Amsterdam
ProductAnonymous-April2024-WinProductDiscovery-MelissaKlemke

ProductAnonymous-April2024-WinProductDiscovery-MelissaKlemke
Polkadot JAM Slides - Token2049 - By Dr. Gavin Wood

Polkadot JAM Slides - Token2049 - By Dr. Gavin Wood
Document Security
- 1. A complete law firm document security policy includes all four areas for total protection. Is your firm following all four best practices — or is your data more vulnerable to theft, compromise, or leaks than you thought? 4 Best Practices For Improving Your Document Security 3. Secure The Network Limit network access to specific IP addresses or ranges through IP address and port filtering Protect print data across the network with encryption protocol support (e.g., SSL) Adopt strong wireless encryption and authentication standards for Wi-FI-capable MFDs Prevent external MFD access and the introduction of viruses/ malware with a firewall 4. Log And Audit Allow admins to view and search all printing, scanning, copying, and faxing activity Gather precise information on any activity with flexible scan lock-and-trace functionality that allows for escalating lock levels Fully track data and activity to reveal clear chain of custody for all paper/ electronic documents 2. Secure The Information Use pull-printing and secure mailboxes to enforce user authentication policies Encrypt print jobs Password- protect all hard drive data Ensure secure data deletion Store passwords, encryption keys, etc. on a Trusted Platform Module chip Require users’ physical presence at MFD before releasing printed documents Use secure watermarking to reduce risk of data leaks via photocopying original documents Embed tracking information visible only to admins Verify authenticity with digital signatures Ensure devices can verify correct fax format to prevent introduction of malware or viruses via tainted fax files Ensure MFDs include controls that restrict access to LAN from fax line Secure MFD storage and improve usability and document protection by integrating with an Enterprise Content Management solution Consider a solution like Adobe’s Information Rights Management (IRM) ES software for better PDF control 1. Secure The Devices Require user authentication for printing, copying, scanning. Restrict access to device USB port Introduce password- protected printing Verify security and integrity of all third- party software on the device Choose authentication that works with other identity management tools (e.g., Microsoft’s Active Directory) Grant administrative privileges for settings, tracking, etc. to a select few within the firm. Manage devices from a single point to track and monitor, troubleshoot, identify unauthorized access, update user credentials, etc. ©2017 Canon Solutions America, Inc. All rights reserved. CANON is a trademark or registered trademark of Canon Inc. in the U.S. and elsewhere. Other trademarks are the property of their respective owners and are hereby acknowledged.