IBM at RSA 2009 conference
•Transferir como PPT, PDF•
1 gostou•590 visualizações
IBM activities and social networking tools while at RSA 2009.
Denunciar
Compartilhar
Denunciar
Compartilhar
Recomendados
Recomendados
Personal Digital Hygiene is a concept developed by Lars Hilse. It focusses on reducing the risk of high value individuals, and their exposure and footprint on the digital world, making them less susceptible to kidnapping+ransom, and other (cyber) crimesPersonal Digital Hygiene

Personal Digital HygieneLars Hilse Global Thought Leader in #CyberSecurity, #CyberTerrorism, #CyberDefence, #CyberCrime
Mais conteúdo relacionado
Semelhante a IBM at RSA 2009 conference
Personal Digital Hygiene is a concept developed by Lars Hilse. It focusses on reducing the risk of high value individuals, and their exposure and footprint on the digital world, making them less susceptible to kidnapping+ransom, and other (cyber) crimesPersonal Digital Hygiene

Personal Digital HygieneLars Hilse Global Thought Leader in #CyberSecurity, #CyberTerrorism, #CyberDefence, #CyberCrime
Semelhante a IBM at RSA 2009 conference (20)
Agile Chennai 2022 - Shyam Sundar | Everything there is to know about Cyber s...

Agile Chennai 2022 - Shyam Sundar | Everything there is to know about Cyber s...
Using SurfWatch Labs' Threat Intelligence to Understand Dark Web Threats

Using SurfWatch Labs' Threat Intelligence to Understand Dark Web Threats
An Introduction To IT Security And Privacy In Libraries

An Introduction To IT Security And Privacy In Libraries
Cybersecurity Threats Web Developers Must Know.pptx

Cybersecurity Threats Web Developers Must Know.pptx
Protecting Businesses with Top Cybersecurity Companies.pptx

Protecting Businesses with Top Cybersecurity Companies.pptx
Social Media for WSET Engineering Open Day for Girls

Social Media for WSET Engineering Open Day for Girls
Último
Último (20)
JavaScript Usage Statistics 2024 - The Ultimate Guide

JavaScript Usage Statistics 2024 - The Ultimate Guide
Microsoft CSP Briefing Pre-Engagement - Questionnaire

Microsoft CSP Briefing Pre-Engagement - Questionnaire
Introduction to FIDO Authentication and Passkeys.pptx

Introduction to FIDO Authentication and Passkeys.pptx
Portal Kombat : extension du réseau de propagande russe

Portal Kombat : extension du réseau de propagande russe
TrustArc Webinar - Unified Trust Center for Privacy, Security, Compliance, an...

TrustArc Webinar - Unified Trust Center for Privacy, Security, Compliance, an...
Event-Driven Architecture Masterclass: Integrating Distributed Data Stores Ac...

Event-Driven Architecture Masterclass: Integrating Distributed Data Stores Ac...
Continuing Bonds Through AI: A Hermeneutic Reflection on Thanabots

Continuing Bonds Through AI: A Hermeneutic Reflection on Thanabots
State of the Smart Building Startup Landscape 2024!

State of the Smart Building Startup Landscape 2024!
Intro to Passkeys and the State of Passwordless.pptx

Intro to Passkeys and the State of Passwordless.pptx
WebRTC and SIP not just audio and video @ OpenSIPS 2024

WebRTC and SIP not just audio and video @ OpenSIPS 2024
The Zero-ETL Approach: Enhancing Data Agility and Insight

The Zero-ETL Approach: Enhancing Data Agility and Insight
Harnessing Passkeys in the Battle Against AI-Powered Cyber Threats.pptx

Harnessing Passkeys in the Battle Against AI-Powered Cyber Threats.pptx
Frisco Automating Purchase Orders with MuleSoft IDP- May 10th, 2024.pptx.pdf

Frisco Automating Purchase Orders with MuleSoft IDP- May 10th, 2024.pptx.pdf
Design and Development of a Provenance Capture Platform for Data Science

Design and Development of a Provenance Capture Platform for Data Science
Navigating the Large Language Model choices_Ravi Daparthi

Navigating the Large Language Model choices_Ravi Daparthi
IBM at RSA 2009 conference
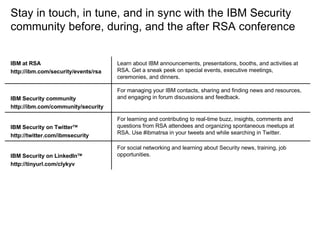
- 1. Stay in touch, in tune, and in sync with the IBM Security community before, during, and the after RSA conference Learn about IBM announcements, presentations, booths, and activities at RSA. Get a sneak peek on special events, executive meetings, ceremonies, and dinners. IBM at RSA http://ibm.com/security/events/rsa For social networking and learning about Security news, training, job opportunities. IBM Security on LinkedIn TM http://tinyurl.com/clykyv For learning and contributing to real-time buzz, insights, comments and questions from RSA attendees and organizing spontaneous meetups at RSA. Use #ibmatrsa in your tweets and while searching in Twitter. IBM Security on Twitter TM http://twitter.com/ibmsecurity For managing your IBM contacts, sharing and finding news and resources, and engaging in forum discussions and feedback. IBM Security community http://ibm.com/community/security
