Hacking Uncovered V Mware
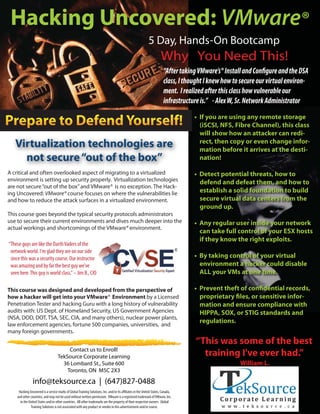
- 1. Hacking Uncovered: VMware® 5 Day, Hands-On Bootcamp Why You Need This! class, I thought I knew how to secure our virtual environ- ment. I realized after this class how vulnerable our infrastructure is.” - Alex W, Sr. Network Administrator • If you are using any remote storage (iSCSI, NFS, Fibre Channel), this class will show how an attacker can redi- rect, then copy or even change infor- Virtualization technologies are mation before it arrives at the desti- not secure “out of the box” nation! A critical and often overlooked aspect of migrating to a virtualized • Detect potential threats, how to environment is setting up security properly. Virtualization technologies defend and defeat them, and how to are not secure “out of the box” and VMware® is no exception. The Hack- ing Uncovered: VMware® course focuses on where the vulnerabilities lie establish a solid foundation to build and how to reduce the attack surfaces in a virtualized environment. secure virtual data centers from the ground up. This course goes beyond the typical security protocols administrators use to secure their current environments and dives much deeper into the • Any regular user inside your network actual workings and shortcomings of the VMware® environment. can take full control of your ESX hosts if they know the right exploits. “These guys are like the Darth Vaders of the network world. I'm glad they are on our side since this was a security course. Our instructor • By taking control of your virtual was amazing and by far the best guy we've environment a hacker could disable seen here. This guy is world class.” – Jim B., CIO ALL your VMs at one time. This course was designed and developed from the perspective of how a hacker will get into your VMware® Environment by a Licensed - Penetration Tester and hacking Guru with a long history of vulnerability mation and ensure compliance with audits with: US Dept. of Homeland Security, US Government Agencies HIPPA, SOX, or STIG standards and (NSA, DOD, DOT, TSA, SEC, CIA, and many others), nuclear power plants, law enforcement agencies, fortune 500 companies, universities, and regulations. many foreign governments. “This was some of the best Contact us to Enroll! TekSource Corporate Learning training I've ever had.” 36 Lombard St., Suite 600 William L. Toronto, ON M5C 2X3 info@teksource.ca | (647)827-0488 and other countries, and may not be used without written permission. VMware is a registered trademark of VMware, Inc. in the United States and/or other countries. All other trademarks are the property of their respective owners. Global © 2009 VMTraining Solutions is not associated with any product or vendor in this advertisement and/or course. Training
- 2. On-Site and Hacking Uncovered: Online Classes Available. Call for More Details! VMware® Covers VMware’s® VI 3 and vSphere 4 Products! CVSE1021 - A Five Day, Hands-on Bootcamp 1 Five Day Hands-on Bootcamp F v ay n o Chapter 1 – Primer and Reaffirming our Knowledge • ESX Networking Components • Virtual Ethernet Adapters and How They Work • Virtual Switches and How They Work • Alternate Data Streams, Encrypted Tunnels , Metasploit, Fuzzers • VLANs in VMWare Infrastructure SaintExploit, Core Impact, Wireshark • Layer 2 Security Features & File System Structure • ARP Cache Poisoning, Hash Algorithm • Managing the Virtual Network with “VirtualCenter” • Kernel, Processes, Account and Groups Chapter 8 – Hardening your ESX Server • Linux and UNIX Permissions • Configuring the ESX/ESXi Host • VirtualCenter, Client Components • The Basics of SAN Security, Part I, Increasing Security Concerns • Security Domains, Switch-to-Switch Domain • What is the Cost of a Hack? • Data Integrity and Security • Current Issues and the Evolving Threat • Security Management Part 2 • Fibre Channel Security Management • Common Management Errors • SAN Access, SAN Security Benefits • Controller-based Mapping, WWN Privileged Access • How traffic is routed between Virtual Machines on ESX hosts • Redundancy, Management • Security Design of the VMware Infrastructure 3 Architecture • VMware Infrastructure Architecture and Security Features • Netcat • Executable Wrappers • BPMTK • Virtualized DMZ Networks Deployment Show that you are an expert at securing Chapter 6 – Remote DataStore Security • Mask and Zone SAN Resources • Securing iSCSI, iFCP and FCIP over IP networks Don’t let your company’s network be a victim of fraud or theft! Contact us to Enroll! TekSource Corporate Learning 36 Lombard St., Suite 600 Toronto, ON M5C 2X3 © 2009 VMTraining
