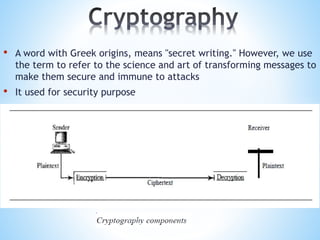
Cryptography
- 1. • A word with Greek origins, means "secret writing." However, we use the term to refer to the science and art of transforming messages to make them secure and immune to attacks • It used for security purpose
- 2. Two Categories We can divide all the cryptography algorithms (ciphers) into two groups: symmetric key (also called secret-key) cryptography algorithms and asymmetric (also called public-key) cryptography algorithms.
- 3. •The same key is used by sender(for encryption ) and the receiver(for decryption ) •The key is shared.
- 4. •Symmetric Key cryptography is sometimes called as secret-key cryptography •Examples of symmetric Key algorithms are DES, 3DES and AES •The most popular symmetric Key system is Data Encryption Standard(DES)
- 5. •DES is a block cipher. It encrypts data in blocks of size 64 bits each. That is, 64 bits of plain text goes as the input to DES, which produces 64 bits of cipher text. The same algorithm and key are used for encryption and decryption, with minor differences. The key length is 56 bits
- 6. Advantages *Simpler *Faster Disadvantages *Two parties must somehow exchange the key in a secure way. *Public key is distributed in a non-secure way between Client/Server. *Easy for hackers to get the key as it is shared in unsecure way.
- 8. • The most common public key algorithm is RSA, named for its inventors Rivest,Shamir,and Adleman (RSA) • Selecting keys • Encryption: 1.Anyone who needs to send a message to Bob can use n and e 2.For example, if Alice needs to send a message to Bob, she can change the message, usually a short one, to an integer. This is the plaintext. She then calculates the ciphertext, using e and n. 3.C=P^e (modn) 4.Alice sends C, the ciphertext, to Bob.
- 9. • Decryption 1.Bob keeps p and d private 2.When he receives the ciphertext, he uses his private key d to decrypt the message 3.P= C^d(modn) 4.Restriction For RSA to work, the value of P must be less than the value of n. If P is a large number, the plaintext needs to be divided into blocks to make P less than n.
- 10. ADVANTAGES • In asymmetric or public key, cryptography there is no need for exchanging keys, thus eliminating the key distribution problem • The primary advantage of public-key cryptography is increased security: the private keys do not ever need to be transmitted or revealed to anyone • Can provide digital signatures that can be repudiated DISADVANTAGES • A disadvantage of using public-key cryptography for encryption is speed: there are popular secret-key encryption methods which are significantly faster than any currently available public-key encryption method.