Distil Networks Protecting the Telephony Industry
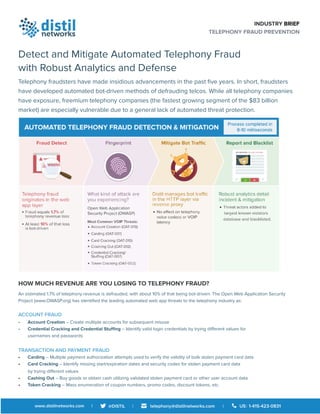
- 1. INDUSTRY BRIEF TELEPHONY FRAUD PREVENTION Detect and Mitigate Automated Telephony Fraud with Robust Analytics and Defense Telephony fraudsters have made insidious advancements in the past five years. In short, fraudsters have developed automated bot-driven methods of defrauding telcos. While all telephony companies have exposure, freemium telephony companies (the fastest growing segment of the $83 billion market) are especially vulnerable due to a general lack of automated threat protection. HOW MUCH REVENUE ARE YOU LOSING TO TELEPHONY FRAUD? An estimated 1.7% of telephony revenue is defrauded, with about 10% of that being bot-driven. The Open Web Application Security Project (www.OWASP.org) has identified the leading automated web app threats to the telephony industry as: ACCOUNT FRAUD • Account Creation – Create multiple accounts for subsequent misuse • Credential Cracking and Credential Stuffing – Identify valid login credentials by trying different values for usernames and passwords TRANSACTION AND PAYMENT FRAUD • Carding – Multiple payment authorization attempts used to verify the validity of bulk stolen payment card data • Card Cracking – Identify missing start/expiration dates and security codes for stolen payment card data by trying different values • Cashing Out – Buy goods or obtain cash utilizing validated stolen payment card or other user account data • Token Cracking – Mass enumeration of coupon numbers, promo codes, discount tokens, etc.
- 2. “Botnets and automated attacks are increasing in both volume and capability. These are revenue generating cybercrime tools, and the motivation for organized criminal factions to steal and monetize anything of value (including data, phone service, and more) isn't going to go away. IoT and the increasing connectedness of everyday devices is already increasing the staging ground for botnets and this will get worse before it gets better. Companies need to obtain visibility into the degree to which they're impacted by this, and then employ strategies and tools to defend themselves, reducing the impact to an acceptable level for their organization.” Michael Machado Chief Security Officer “Any company that does not ensure its software is designed to be securable leaves itself open to attack. According to Veracode, “with more than 20 percent of all web vulnerabilities being attributed to SQL injection” this is a major target for hackers. There are of course multiple other Web application exploits, however at least addressing Injection, Broken Authentication and Session Management, and Cross-Scripting can make a major difference. Hackers have tools that can help them find vulnerabilities and they are looking for the easiest sites to exploit.” Bryan Martin Chief Technology Officer “As an internet telephony service provider for ten years, our company has encountered and learned from occurrences of fraud, some quite costly. This caused us to need to invest significant time and money developing sophisticated proprietary methods to thwart fraud as there were no available solutions on the market.” Koi Lim Chief Executive Officer
- 3. ABOUT DISTIL NETWORKS Distil Networks, the global leader in bot detection and mitigation, is the only easy and accurate way to protect web applications from bad bots, API abuse, and fraud. With Distil, you automatically block 99.9% of malicious traffic without impacting legitimate users. Distil Web Security defends websites against web scraping, brute force attacks, competitive data mining, account takeovers, online fraud, unauthorized vulnerability scans, spam, man-in-the-middle attacks, digital ad fraud, and downtime. Distil API Security protects all types of APIs including those serving web browsers, mobile applications, and Internet of Things (IoT) connected devices. Distil API Security defends APIs against developer errors, integration bugs, automated scraping, and web and mobile hijacking. For more information on Distil Networks, visit us at http://www.distilnetworks.com or follow @DISTIL on Twitter. SOPHISTICATED ATTACKS DEMAND A SOPHISTICATED RESPONSE Relentless automated bot-driven attacks require a powerful security solution that is itself “always-on” and can respond with speed equal to the attackers and provide for instantaneous defense. Distil Networks can be deployed as a physical or virtual appliance to protect VOIP, without interfering with voice traffic or causing latency. The Distil solution integrates with diverse technology stacks including Amazon Web Services AMI, Microsoft Azure, VMWare, Google Cloud Platform, and Akamai. FLEXIBLE DEPLOYMENT OPTIONS Cloud CDN: If VOIP traffic is streamed separately from web traffic on a separate domain, bot mitigation can be deployed using the Distil Public Cloud. Appliance: Customers can configure their load balancer to not route VOIP traffic to Distil but to a separate domain for private deployments. Telephony APIs: Distil’s API Protection is optimal for telephony APIs since they are usually private and Distil API is designed specifically to protect against overload endpoint requests and stolen tokens. CONTACT DISTIL FOR A FREE CONSULTATION AND TRIAL Distil can provide a free in-depth Automated Threat VOIP Revenue Loss Audit to provide you with a holistic view of your telephony fraud landscape. We also offer a 30-day no-cost, no-obligation trial of Bot Mitigation solution for VOIP. “Telephony providers have significantly bigger challenges to overcome in order to support free trials and other freemium models because of their cost structure. The industry is a magnet for fraudsters and freeloaders. Distil is the first tool that evens the odds back in favor of the providers.” Sam Aparicio Chief Executive Officer