Flipping the Economics of Attacks
•
3 gostaram•5,432 visualizações
Flipping the Economics of Attacks
Denunciar
Compartilhar
Denunciar
Compartilhar
Baixar para ler offline
Recomendados
Recomendados
Estudio de Russell Reynolds Associates sobre ciberseguridad que explora la importancia de la relación entre el Chief Information Security Officer y el Consejo de Administración. Cyber security: Five leadership issues worthy of board and executive attention

Cyber security: Five leadership issues worthy of board and executive attentionRamón Gómez de Olea y Bustinza
Mais conteúdo relacionado
Mais procurados
Estudio de Russell Reynolds Associates sobre ciberseguridad que explora la importancia de la relación entre el Chief Information Security Officer y el Consejo de Administración. Cyber security: Five leadership issues worthy of board and executive attention

Cyber security: Five leadership issues worthy of board and executive attentionRamón Gómez de Olea y Bustinza
Mais procurados (18)
Cybersecurity Disrupters and Cybersecurity Insurance in the COVID-19 Era – Is...

Cybersecurity Disrupters and Cybersecurity Insurance in the COVID-19 Era – Is...
Why Startups Need to Strengthen Application Security

Why Startups Need to Strengthen Application Security
Cybersecurity Risk Management for Financial Institutions

Cybersecurity Risk Management for Financial Institutions
Improving Cyber Security Literacy in Boards & Executives

Improving Cyber Security Literacy in Boards & Executives
Business Continuity, Data Privacy, and Information Security: How do they link?

Business Continuity, Data Privacy, and Information Security: How do they link?
Cyber security: Five leadership issues worthy of board and executive attention

Cyber security: Five leadership issues worthy of board and executive attention
MasterSnacks: Cybersecurity - Playing Offense: A Proactive Approach to Cybers...

MasterSnacks: Cybersecurity - Playing Offense: A Proactive Approach to Cybers...
TRU Snacks Webinar Series - Navigating Cybersecurity Risk in the Age of COVID-19

TRU Snacks Webinar Series - Navigating Cybersecurity Risk in the Age of COVID-19
Cybersecurity: Cyber Risk Management for Banks & Financial Institutions

Cybersecurity: Cyber Risk Management for Banks & Financial Institutions
Semelhante a Flipping the Economics of Attacks
Semelhante a Flipping the Economics of Attacks (20)
Before the Breach: Using threat intelligence to stop attackers in their tracks

Before the Breach: Using threat intelligence to stop attackers in their tracks
Security - intelligence - maturity-model-ciso-whitepaper

Security - intelligence - maturity-model-ciso-whitepaper
PandaLabs Reveals its Predictions for Cybersecurity Trends in 2018

PandaLabs Reveals its Predictions for Cybersecurity Trends in 2018
White Paper :- Spear-phishing, watering hole and drive-by attacks :- The New ...

White Paper :- Spear-phishing, watering hole and drive-by attacks :- The New ...
Executive Summary of the 2016 Scalar Security Study

Executive Summary of the 2016 Scalar Security Study
Cyber Threat Intelligence − How to Get Ahead of Cybercrime

Cyber Threat Intelligence − How to Get Ahead of Cybercrime
Cyber Threat Intelligence − How to Get Ahead of Cybercrime

Cyber Threat Intelligence − How to Get Ahead of Cybercrime
Mais de PaloAltoNetworks
Mais de PaloAltoNetworks (10)
Pro Tips for Power Users – Palo Alto Networks Live Community and Fuel User Gr...

Pro Tips for Power Users – Palo Alto Networks Live Community and Fuel User Gr...
2016 Cybersecurity Predictions for Asia Pacific from Palo Alto Networks VP, C...

2016 Cybersecurity Predictions for Asia Pacific from Palo Alto Networks VP, C...
EVOLUTION DES MENACES QUI PESENT SUR LES CENTRES DE DONNEES

EVOLUTION DES MENACES QUI PESENT SUR LES CENTRES DE DONNEES
Último
Último (20)
Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...

Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...
Apidays New York 2024 - Scaling API-first by Ian Reasor and Radu Cotescu, Adobe

Apidays New York 2024 - Scaling API-first by Ian Reasor and Radu Cotescu, Adobe
Powerful Google developer tools for immediate impact! (2023-24 C)

Powerful Google developer tools for immediate impact! (2023-24 C)
Tata AIG General Insurance Company - Insurer Innovation Award 2024

Tata AIG General Insurance Company - Insurer Innovation Award 2024
What Are The Drone Anti-jamming Systems Technology?

What Are The Drone Anti-jamming Systems Technology?
Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...

Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...
AWS Community Day CPH - Three problems of Terraform

AWS Community Day CPH - Three problems of Terraform
Strategies for Landing an Oracle DBA Job as a Fresher

Strategies for Landing an Oracle DBA Job as a Fresher
How to Troubleshoot Apps for the Modern Connected Worker

How to Troubleshoot Apps for the Modern Connected Worker
TrustArc Webinar - Stay Ahead of US State Data Privacy Law Developments

TrustArc Webinar - Stay Ahead of US State Data Privacy Law Developments
Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...

Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...
TrustArc Webinar - Unlock the Power of AI-Driven Data Discovery

TrustArc Webinar - Unlock the Power of AI-Driven Data Discovery
Flipping the Economics of Attacks
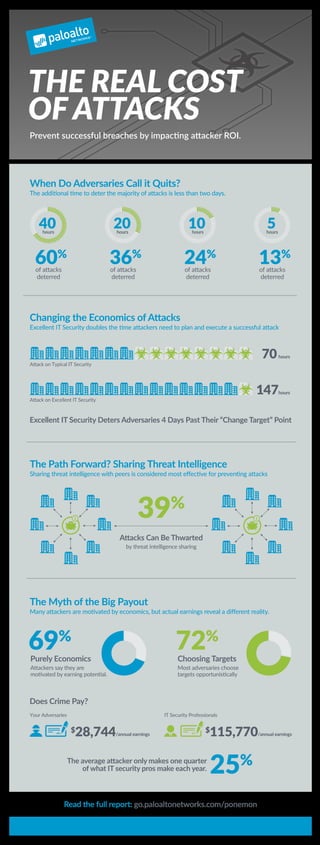
- 1. When Do Adversaries Call it Quits? The additional time to deter the majority of attacks is less than two days. The Myth of the Big Payout Many attackers are motivated by economics, but actual earnings reveal a different reality. Does Crime Pay? Purely Economics Attackers say they are motivated by earning potential. Excellent IT Security Deters Adversaries 4 Days Past Their “Change Target” Point The average attacker only makes one quarter of what IT security pros make each year. Changing the Economics of Attacks Excellent IT Security doubles the time attackers need to plan and execute a successful attack The Path Forward? Sharing Threat Intelligence Sharing threat intelligence with peers is considered most effective for preventing attacks Read the full report: go.paloaltonetworks.com/ponemon 69% 25% Choosing Targets Most adversaries choose targets opportunistically 72% 39% Attacks Can Be Thwarted by threat intelligence sharing $28,744/annual earnings 70hours 147hours i i Your Adversaries IT Security Professionals Attack on Typical IT Security Attack on Excellent IT Security $115,770/annual earnings 60% of attacks deterred 40hours hours hours hours 20 36% of attacks deterred 10 24% of attacks deterred 5 13% of attacks deterred THE REAL COST OF ATTACKS Prevent successful breaches by impacting attacker ROI.
