Vulnerability Management Detection & Response
•
0 gostou•50 visualizações
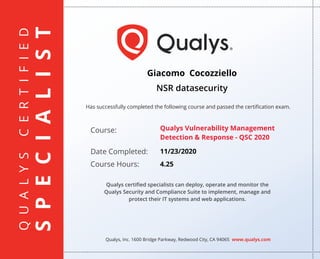
Qualys certified specialists can deploy, operate and monitor the Qualys Security and Compliance Suite to implement, manage and protect their IT systems and web applications.
Denunciar
Compartilhar
Denunciar
Compartilhar
Recomendados
Mais conteúdo relacionado
Mais procurados
Mais procurados (12)
Mais de GiacomoCocozziello
Mais de GiacomoCocozziello (20)
Effective classification of android malware families through dynamic features...

Effective classification of android malware families through dynamic features...
Purple Teaming Fundamentals Cocozziello Giacomo.pdf

Purple Teaming Fundamentals Cocozziello Giacomo.pdf
Practical Industrial Control System Penetration Testing

Practical Industrial Control System Penetration Testing
Mitre attack defender mad attack for cyber threat intelligence

Mitre attack defender mad attack for cyber threat intelligence
Último
Driving Behavioral Change for Information Management through Data-Driven Gree...

Driving Behavioral Change for Information Management through Data-Driven Gree...Enterprise Knowledge
Último (20)
Driving Behavioral Change for Information Management through Data-Driven Gree...

Driving Behavioral Change for Information Management through Data-Driven Gree...
Apidays Singapore 2024 - Building Digital Trust in a Digital Economy by Veron...

Apidays Singapore 2024 - Building Digital Trust in a Digital Economy by Veron...
ProductAnonymous-April2024-WinProductDiscovery-MelissaKlemke

ProductAnonymous-April2024-WinProductDiscovery-MelissaKlemke
Raspberry Pi 5: Challenges and Solutions in Bringing up an OpenGL/Vulkan Driv...

Raspberry Pi 5: Challenges and Solutions in Bringing up an OpenGL/Vulkan Driv...
IAC 2024 - IA Fast Track to Search Focused AI Solutions

IAC 2024 - IA Fast Track to Search Focused AI Solutions
Understanding Discord NSFW Servers A Guide for Responsible Users.pdf

Understanding Discord NSFW Servers A Guide for Responsible Users.pdf
Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...

Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...
Powerful Google developer tools for immediate impact! (2023-24 C)

Powerful Google developer tools for immediate impact! (2023-24 C)
From Event to Action: Accelerate Your Decision Making with Real-Time Automation

From Event to Action: Accelerate Your Decision Making with Real-Time Automation
Boost Fertility New Invention Ups Success Rates.pdf

Boost Fertility New Invention Ups Success Rates.pdf
Automating Google Workspace (GWS) & more with Apps Script

Automating Google Workspace (GWS) & more with Apps Script
Handwritten Text Recognition for manuscripts and early printed texts

Handwritten Text Recognition for manuscripts and early printed texts
08448380779 Call Girls In Diplomatic Enclave Women Seeking Men

08448380779 Call Girls In Diplomatic Enclave Women Seeking Men
Vulnerability Management Detection & Response
- 1. QUALYSCERTIFIED SPECIALIST Has successfully completed the following course and passed the certification exam. Qualys, Inc. 1600 Bridge Parkway, Redwood City, CA 94065 www.qualys.com Course: Date Completed: Course Hours: Qualys certified specialists can deploy, operate and monitor the Qualys Security and Compliance Suite to implement, manage and protect their IT systems and web applications. Giacomo Cocozziello NSR datasecurity Qualys Vulnerability Management Detection & Response - QSC 2020 11/23/2020 4.25