"Evolving cybersecurity strategies" - Seizing the Opportunity
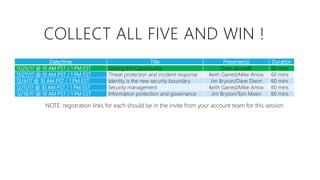
- 1. COLLECT ALL FIVE AND WIN ! Date/time Title Presenter(s) Duration 11/20/17 @ 10 AM PST / 1 PM EST Seizing the Opportunity Dean Iacovelli 60 mins 11/27/17 @ 10 AM PST / 1 PM EST Threat protection and incident response Keith Garred/Mike Amox 60 mins 12/4/17 @ 10 AM PST / 1 PM EST Identity is the new security boundary Jim Bryson/Dave Dixon 60 mins 12/11/17 @ 10 AM PST / 1 PM EST Security management Keith Garred/Mike Amox 60 mins 12/18/17 @ 10 AM PST / 1 PM EST Information protection and governance Jim Bryson/Tom Moen 60 mins NOTE: registration links for each should be in the invite from your account team for this session
- 2. NOTE: THIS SESSION WILL BE RECORDED SO PLEASE DON’T TYPE OR SAY ANYTHING DURING THE SESSION THAT YOU WOULDN'T WANT CAPTURED FOR POSTERITY. ☺
- 3. SEIZING THE OPPORTUNITY Dean Iacovelli Director, Secure Enterprise Microsoft State and Local Government Evolving cybersecurity strategies
- 4. A LITTLE ABOUT ME – DEAN IACOVELLI 12 years working with Microsoft State and Local customers Roles ▪ First Chief Security Advisor for Microsoft State and Local ▪ First Cloud Services Director, incubated team of specialists on what would become Office 365 ▪ Currently Director of Secure Enterprise, managing a team of cybersecurity specialists focused on security for Office 365, Identity, Threat Protection, and Windows security
- 5. ANY OF THESE LOOK FAMILIAR ? ANY FAVORITES ? Source: ICMA survey of top cyber issues for state and local government customers
- 6. LOGIC MAP FOR THIS CONVERSA TION • SLG (ok everyone) can do better on cybersecurity and a conversation on alternative approaches would be useful Problem statement • Move to a “best of breed” security platform approach. Argument #1 • Move to a “cloud first” strategy to leverage hyperscale cloud vendor investments in cyber. Argument #2 • Why my platform, why my cloud • Follow-on sessions discuss/prove this in more detail Argument #3
- 7. WHY DOES SECURITY FEEL LIKE THE MOST FRUSTRATING PROBLEM IN GOVERNMENT IT ?
- 8. THE THREAT IS ASYMMETRICAL "TODAY WE WERE UNLUCKY, BUT REMEMBER WE ONLY HAVE TO BE LUCKY ONCE - YOU WILL HAVE TO BE LUCKY ALWAYS.” – IRISH REPUBLICAN ARMY, 1984 BRIGHTON HOTEL BOMBING TARGETING MARGARET THATCHER TIME ACTIVITY Mobility and Internet- enabled access Security / IT governance improvements Financial and political risk
- 10. THE CHANGING THREAT LANDSCAPE Half of all reported incidents are in pubsec and 41% recently responded they don’t know if/how often they’re breached •Attacks are getting more targeted and are using the transparency of government against us. • What your neighbor isn’t doing IS your problem i.e. we’re all on the SAME network. Solutions must be comprehensive or they fail. •Two typical outcomes – exfiltration of valuable data and/or recruitment of compromised devices into botnet Source: Verizon DBIR 2017 and ICMA survey
- 11. SO WHAT’S THE REAL WORLD COST OF NOT DEALING WITH SECURITY ? Average of 4M per breach $172 per record in public sector Costs ? Forensics (up to $2k/hr) Notification (except AL, SD) Credit monitoring Helpdesk outsourcing The costs do NOT include remediation and are potentially ASYMMETRICAL to org size Sources: Ponemon Institute and NY
- 12. RESOURCING IN GENERAL IS AN UPHILL BATTLE Source: ICMA survey of top cyber issues for state and local government Resource-related challenge in fighting cyber
- 13. AND YOU CAN’T HIRE ENOUGH BODIES TO WORK ON THE PROBLEM. AWESOME. PERCENTAGE OF RESPONDENTS WHO SAY THERE IS A SHORTAGE OF CYBERSECURITY PROFESSIONALS IN THEIR COUNTRY Mexico Australia Japan Germany United States Israel France United Kingdom 90% 80% 70% 60% 50% 40% 30% 20% 10% 0%
- 14. SO IN SHORT… TRYING TO SOLVE THE SECURITY PROBLEM AT AN INDIVIDUAL ORG LEVEL WITH CURRENT APPROACHES AND RESOURCES ISN’T SUFFICENT AND COULD POTENTIALLY BANKRUPT YOUR ORGANIZATION. SO WHAT ARE THE ALTERNATIVES ?
- 15. ARGUMENT #1 Government customers need to transition from “best of breed” point solutions strategy to “best of breed” security PLATFORM strategy.
- 16. COST EFFICIENCY Same or better services at lower cost INTEGRATION Solutions work “better together” for real-time response INNOVATION New approaches to protecting, detecting, responding Best of breed and legacy made this hard Lack of standards made this hard Politics, budget turmoil, and deployment made this hard THE HISTORY OF GOVERNMENT CYBER IN ONE TRIANGLE PICK TWO (IF YOU’RE LUCKY ☺)
- 17. EVOLVING APPROACHES MONO LITHIC PERIMETER BASED BEST OF BREED PRODUCTS BEST OF BREED PLATFORM
- 18. • External Assets Created • 2 BOMs (datasheet, customer deck, sales guide, SOW, FAQ) • 1 Joint announcement blog • 4 teaser videos • 2 Channel 9 interviews • Internal Landing and Awareness • Met Premier Support landing requirements • Strategy, Volta, Governance/Operations • Met MCS landing requirements • Identified communication channels • Training accreditation in progress • BOM posting to Services Portfolio and Phoenix catalog in progress • Seller awareness being developed with MCS landing lead MICROSOFT READY CYBERSECURITY TECHNICAL TRACK • Renamed track from Security and Privacy to Cybersecurity • Curated 64 abstracts as of 05/04 • 35 abstracts at L300 – VERY POSITIVE • Abstract review with stakeholders in progress • Final track will have: 23 Session allocations + 2 labs + 10 online sessions CYBERSECURITY LANDSCAPE IN 2017 – CAN YOU EFFECTIVELY INTEGRATE ? “THE SINGLE BIGGEST ISSUE … IS THE NEED TO SIMPLIFY AND CONSOLIDATE THEIR SECURITY INFRASTRUCTURE” “EVERY DIFFERENT PRODUCT WILL HAVE SEPARATE MANAGEMENT SYSTEMS, OFTEN WITH LIMITED CONNECTIVITY TO WORK ALONGSIDE OTHERS.… THUS SLOWING DOWN RESPONSE AND REMEDIATION TIMES” “THIS RESULTS IN THE IRONIC SITUATION OF ACTUALLY HAVING MORE SECURITY DEVICES IN YOUR NETWORK WHICH ACTUALLY MAKES IT LESS SECURE.” Source: https://www.finextra.com/blogposting/13893/consolidation-and-integration-of-security-solutions-in-financial-services “SOME LARGE ORGANIZATIONS HAVE AS MANY AS 40 OR MORE DIFFERENT SECURITY VENDORS INSIDE THEIR NETWORKS”
- 19. COST/APPROACH CONTINUUM Solution2 Solution1 Solution3 Solution4 Solution5 TIME COST Solution2 Solution1 Solution3 Solution4 Solution5 TIME COST “BEST OF BREED” PRODUCTS “BEST OF BREED” PLATFORM BUT AT LEAST IT’S EXPENSIVE IF YOU DO. Integration cost Software cost Integration becomes more complex, expensive with each solution… Increased leverage and optimization of existing tools, built in integration, consistent policy, infra (AD), IT skills, user training …and eventually, I become afraid of breaking my custom integration if I upgrade this
- 20. Designed Identity Integrated automated Built in “Simplify the scope of EPP by using OS-embedded security features, such as disk encryption and USB device control, especially when migrating to Windows 10” - Gartner “Redefining Endpoint Protection” report, Sep 2017
- 21. OPINION: GARTNER IS CATCHING ON TO OUR PLATFORM VISION Takeaways From the Executive Summary – “2017 Gartner MQ for Endpoint Protection” Microsoft moved significantly to the right on the Vision Axis since 2016. For 2017, rather than submitting for just Windows Defender, we submitted for capabilities that extended across System Center EPP and other security platform technologies as well, while pointing to a broader security vision included in our OS-level protections. The dot placement in the 2017 MQ graphic truly represents all Microsoft capabilities, rather than an individual offering. Gartner referred to Microsoft's future vision as “very forward-thinking and technically elegant” and noted strengths in new security features in Windows 10 that are easily managed centrally through Intune and SCCM
- 22. ARGUMENT #2 In order to deal with the bank-breaking nature and scale of the cybersecurity problem, individual orgs need to standardize on a cloud-first strategy to “buy a slice” of the investment hyperscale cloud vendors are making in security.
- 23. MOVING TO CLOUD IS PART OF A SOUND RISK MANAGEMENT STRATEGY Transfer Move workloads to hyperscale cloud vendor, pooling risk management resources (car insurance analogy) Isolate Federal SIPRnet, NIPRnet separation Mitigate This is 95% of commercial solutions, current effort, and resources. Eliminate Patching a vulnerability, turning off your Internet connection. ☺
- 24. WE’VE COME A LONG WAY, BABY MICROSOFT THOUGHT LEADERSHIP IN CYBERSECURITY Microsoft is “front-and-center in the shifting ground of both politics and nationalism. [Brad Smith’s keynote] “lays a blueprint for an organization that hasn’t yet been created, but which may be called into being through his words.” – ELIZABETH WEISE, USA TODAY “There is a growing threat of cyberattacks from nation-states, and Microsoft wants the tech industry to be at the forefront of protecting the world from hacking and other digital crime.” – MICHELLE CASTILLO, CNBC – JAY GREENE, WSJ “Microsoft found that customers who checked their security settings boosted their scores on average by 18% over those who didn’t visit the security dashboard.” “Companies concerned about cybersecurity have a fleet of new Microsoft tools coming their way. ” “National Security Agency workers can now safely use Microsoft Surface tablets devices for data mining, intelligence gathering, or more humdrum work like checking email.” – JONATHAN VANIAN, THE REGISTER – BLAIR HANLEY FRANK, PCWORLD And don’t forget… Security Development Lifecycle Government Security Program Public/private partnerships Industry alliances
- 25. Threat protection over time Attackers take advantage of periods between releases P R O D U C T R E L E A S E T H R E A T S O P H I S T I C A T I O N T I M E CAPABILITY Game change with Software as a Service Disrupt and out innovate our adversaries by design Protection Gap AGILITY OF HYPERSCALE CLOUD REDUCES ATTACK SURFACE
- 26. OTHER SECURITY ADVANTAGES OF CLOUD ERA TRADITIONAL APPROACH CLOUD-ENABLED SECURITY
- 27. Our most unique global asset in the fight, informed by trillions of feeds. Machine learning helps sort the signal from the noise. This signal is leveraged across all of Microsoft’s security services. 450B monthly authentications 18+B Bing web pages scanned750M+ Azure user accounts Enterprise security for 90% of Fortune 500 Malware data from Windows Defender Shared threat data from partners, researchers and law Enforcement worldwide Botnet data from Microsoft Digital Crimes Unit 1.2B devices scanned each month 400B emails analyzed 200+ global cloud consumer and Commercial services INTELLIGENT SECURITY GRAPH
- 28. NO TOUGH DECISIONS NEEDED IN CHOOSING OUR PLATFORM EITHER. WE ARE AN INDUSTRY LEADER ACROSS 19 ENTERPRISE WORKLOADS. NOTE: we are also Visionary or Challenger in 17 others Why Amazon Won't Catch #1 Microsoft In The Cloud: Because It's All About Software
- 29. THE TRANSFORMATIONAL ECONOMICS OF UTILITY- BASED COMPUTING WORK FOR SECURITY TOO. WE RUN ON TRUST. Our cloud business model simply evaporates without trust – highly motivated to ensure security is handled and resourced to do so. 1B annual investment. 1 GET COMPLIANT – AT HYPERSCALE. Meet all your compliance requirements faster, stay compliant more easily and cost effectively 2 WHAT’S EVEN BETTER THAN A CERT ? A TRACK RECORD. We defend 200+ of the largest cloud services in the world, some since 1998 (Windows Update). Oh yeah and Microsoft itself. 3
- 30. 4MDoD Windows 10 users being deployed for modern security platform 3MUS government users on Office 365 7038Number of state and local agencies using Office 365 31State level CJIS agreements signed AND BY THE WAY, ALL THE KIDS ARE DOING IT 14Other US government and industry certs, including FedRAMP, ISO 27001, CSA STAR 1, FIPS 140-2, NIST 800- 171, ITAR, IRS 1075, HIPAA BAA, PCI DSS L1
- 31. Apps and Data SaaS THE BREADTH OF OUR VISION AND CAPABILITIES IS UNIQUE. Malware Protection Center Cyber Hunting Teams Security Response Center DeviceInfrastructure CERTs PaaS IaaS Identity INTELLIGENT SECURITY GRAPH Cyber Defense Operations Center Digital Crimes Unit Antivirus NetworkIndustry Partners
- 32. BRAKES ARE WHAT ALLOW THE CAR TO GO FASTER. FINALLY, PLEASE REMEMBER…
- 33. NEXT STEPS“Evolving Cybersecurity Strategies” customer webcast series 1 Windows 10 deployment workshop 2 Security CIE (Customer immersion experience) 3 Cybersecurity POCs/trials 4 MCS risk assessment (NIST- based) 5
- 34. COMING UP NEXT ! Date/time Title Presenter(s) Duration 11/27/17 @ 10 AM PST / 1 PM EST Threat protection and incident response Keith Garred/Mike Amox 60 mins 12/4/17 @ 10 AM PST / 1 PM EST Identity is the new security boundary Jim Bryson/Dave Dixon 60 mins 12/11/17 @ 10 AM PST / 1 PM EST Security management Keith Garred/Mike Amox 60 mins 12/18/17 @ 10 AM PST / 1 PM EST Information protection and governance Jim Bryson/Tom Moen 60 mins
- 35. THANK YOU !
- 36. APPENDIX
- 37. 1-3 Weeks Initial Assessment/Training 1-3 Months Secure Enterprise Foundation – Identity Administration & Privileged Access 6+ Months Secure Identity / Device Pillars Cyber Security Advisor (CSA) Architectural Oversight and Technical Leadership – Best Practices for Security Investments – Security Strategy Red Forest - ESAE (Enhanced Security Administration Environment) AD Hardening/Remediation Tiered Administration Just Enough Admin AD Hardening and Account Rationalization COS Security Operations Services (PADS) Windows 10 Security (Defender/ATP, Windows Client Hardening) WorkshopPLUS Windows Client Security Review/Plan POP-ADD AD Delegation Review / Plan POP-ATA Advanced Threat Analytics Review/Plan POP – SLAM Secure Lateral Account Movement Review /Plan POP-SUM Patch Management Review / Plan AADIS / MFA Azure AD Implementation Services Secure Productive Enterprise Enterprise Mobility & Security Designated Security Engineer (DSE) Operational Integration, Training, Readiness & Troubleshooting Data Loss Protection Azure Info Protection PAW Privileged Account Workstation OMS Microsoft Operations Management Service Workshop/Tuning/Optimization MIM PAM Privileged Access Management MCS CYBERSECURITY OFFERINGS
- 38. PLAN ENTER TRAVERSE EXECUTE MISSION 4 Threat Actors exfiltrate PII and other sensitive business data Threat Actor targets employee(s) via phishing campaign1 Workstation compromised, threat actor gathers credentials2a Threat Actors use stolen credentials to move laterally 3a Employee B opens infected email (Mobile or PC). Attacker disables antivirus 2b Compromised credentials/ device used to access cloud service / enterprise environment 3bc Credentials harvested when employee logs into fake website 2c A. Enter and Navigate Any employee opens attack email Access to most/all corporate data B. Device Compromise Targeted employee opens attack email Access to same data as employee C. Remote Credential Harvesting Targeted employee(s) enter credentials in website Access to same data as employee(s) Common Attacks Office 365 Technology • Advanced Threat Protection (requires E5) EMS Technology • Cloud App Security (CASB) (requires E5) Office 365 Technology • Advanced Security Management (basic CASB) (requires E5) Azure Technology • Multi-Factor Authentication • Azure Identity Protection Microsoft Incident Response Teams can be engaged to investigate any incident type as well as to assess your organization for existing compromises Windows 10 Technology • Smartscreen URL and App reputation EMS Technology • Azure Information Protection (requires E5) Office 365 Technology • Data Loss Prevention Windows 10 Technology • Windows Information Protection Azure Technology • Disk, Storage, SQL Encryption • Key Vault • … Any Windows 10 Technology • Device Guard • Credential & App Guard • Defender Advanced Threat Protection (requires E5) Managed Detection and Response (MDR) • Enterprise Threat Detection Published Guidance • Securing Privileged Access Roadmap Professional Services • Security Foundation • Enhanced Security Admin Environment (ESAE) Technology • Advanced Threat Analytics (in EMS E3) • Azure Security Center & Operations Management Suite (OMS) • …and more EMS Technology • Intune conditional access Managed Detection and Response (MDR) • Enterprise Threat Detection (PCs only)
- 39. Internet of Things Unmanaged & Mobile Clients Sensitive Workloads CYBERSECURITY REFERENCE ARCHITECTURE Extranet Azure Key Vault Azure Security Center • Threat Protection • Threat Detection System Center Configuration Manager + Intune Microsoft Azure On Premises Datacenter(s) NGFW Nearly all customer breaches that Microsoft’s Incident Response team investigates involve credential theft 63% of confirmed data breaches involve weak, default, or stolen passwords (Verizon 2016 DBR) Colocation $ EPP - Windows Defender EDR - Windows Defender ATP Mac OS Multi-Factor Authenticatio n MIM PAMAzure App Gateway Network Security Groups Azure AD PIM Azure Antimalware Disk & Storage Encryption SQL Encryption & Firewall Hello for Business Windows Info Protection Enterprise Servers VPN VPN VMs VMs Certification Authority (PKI) Incident Response Vulnerability Managemen t Enterprise Threat Detection Analytic s Managed Security Provider OMS ATA SIEM Security Operations Center (SOC) Logs & Analytics Active Threat Detection Hunting Teams Investigation and Recovery WE F SIEM Integration IoT Identity & AccessUEBA Windows 10 Windows 10 Security • Secure Boot • Device Guard • Application Guard • Credential Guard • Windows Hello Managed Clients Windows Server 2016 Security Shielded VMs, Device Guard, Credential Guard, Just Enough Admin, Hyper-V Containers, Nano server, … Software as a Service ATA Privileged Access Workstations (PAWs) • Device Health Attestation • Remote Credential Guard Intune MDM/MAM Conditional Access Cloud App Security Azure Information Protection (AIP) • Classify • Label • Protect • Report Office 365 DLP Endpoint DLP Structured Data & 3rd party Apps DDoS attack mitigation ClassificationLabels ASM Lockbo x Office 365 Information Protection Legacy Window s Backup and Site Recovery Shielded VMs Domain Controllers Office 365 ATP • Email Gateway • Anti-malware Hold Your Own Key (HYOK) ESAE Admin Forest PADS 80% + of employees admit using non-approved SaaS apps for work (Stratecast, December 2013) IPS Edge DLP SSL Proxy Security Development Lifecycle (SDL) Azure AD Identity Protection Security Appliances
- 41. CLOUD SERVICES FOR GOVERNMENT The cloud platform designed to meet U.S. government demands Government community and compliance Screened US personnel Physical, network and logical isolation in US locations http://azure.microsoft.com/en-us/features/gov/
- 42. COMMITMENT TO INDUSTRY-LEADING COMPLIANCE ECSB FedRAMP HIPAA IRS 1075 More than just adhering to compliance standards, Microsoft has been actively engaged in designing and testing compliance standards, establishing itself as an integral part of the government assurance and security ecosystem. CJIS Microsoft is the first and only hyperscale cloud provider to meet CJIS security requirements for infrastructure and productivity. 42 FIPS 140-2SOC 1 SOC 2
- 43. CJIS Status in the United States KS WV
- 44. Physical Security Security Best Practices Secure Network Layer Data Encryption Data Loss Prevention (DLP) Office Message Encryption (OME) Mobile Device Management (MDM) Multi Factor Authentication (MFA) Rights Management (RMS) Account Mgmt. Incident Monitoring Data Encryption Encryption of stored data and more… Data Minimization & Retention Access Control Audits 1000+ controls Service Capabilities Built-in Customer Controls Why Office 365 for the Chief Security Officer? ECSB FedRAMP HIPAA IRS 1075 CJIS Office 365 Service What? Master GRC Control Sets How? Certifications Says who? ISO Advanced Threat Protection (ATP) Enterprise Security Suites (EMS) Extensions
- 45. Strategic Entities to Secure with Hybrid Cloud Services Identity
- 46. THE INTELLIGENT SECURITY GRAPH IN ACTION
- 47. Mobile device & app management Information protection Identity and access management Threat protection HOLISTIC AND INNOVATIVE SOLUTIONS FOR PROTECTION ACROSS USERS, DEVICES, APPS AND DATA Protect at the front door Detect & remediate attacks Protect your data anywhere
- 48. EXTEND ACCESS TO ALL APPLICATIONS WITH ONE IDENTITY Cloud HR Web apps (Azure Active Directory Application Proxy) Integrated custom apps SaaS apps HR and other directories 2500+ popular SaaS apps Connect and sync on-premises directories with Azure Easily publish on-premises web apps via Application Proxy + Custom apps through a rich standards-based platform Microsoft Azure AD
- 49. Common identity Single sign-on and Multi-Factor Auth (MFA) Self-service experiences Comprehensive security & governance Breadth of applications Desktop Virtualization Information protection Mobile device & application management Identity and Access Management