Problems with biometric authentication
•
1 gostou•1,852 visualizações
This note outlines some of the conceptual cha
Denunciar
Compartilhar
Denunciar
Compartilhar
Baixar para ler offline
Recomendados
An emerging approach to the problem of identity theft is represented by
the adoption of biometric authentication systems. Such systems however present
several challenges, related to privacy, reliability and security of the biometric data.
Inter-operability is also required among the devices used for authentication. Moreover,
very often biometric authentication in itself is not sufficient as a conclusive
proof of identity and has to be complemented with multiple other proofs of identity
such as passwords, SSN, or other user identifiers. Multi-factor authentication mechanisms
are thus required to enforce strong authentication based on the biometric
and identifiers of other nature.
In this paper we propose a two-phase authentication mechanism for federated
identity management systems. The first phase consists of a two-factor biometric
authentication based on zero knowledge proofs. We employ techniques from the
vector-space model to generate cryptographic biometric keys. These keys are kept
secret, thus preserving the confidentiality of the biometric data, and at the same
time exploit the advantages of biometric authentication. The second phase combines
several authentication factors in conjunction with the biometric to provide a
strong authentication. A key advantage of our approach is that any unanticipated
combination of factors can be used. Such authentication system leverages the information
of the user that are available from the federated identity management
system.(2007) Privacy Preserving Multi-Factor Authentication with Biometrics

(2007) Privacy Preserving Multi-Factor Authentication with BiometricsInternational Center for Biometric Research
Mais conteúdo relacionado
Semelhante a Problems with biometric authentication
An emerging approach to the problem of identity theft is represented by
the adoption of biometric authentication systems. Such systems however present
several challenges, related to privacy, reliability and security of the biometric data.
Inter-operability is also required among the devices used for authentication. Moreover,
very often biometric authentication in itself is not sufficient as a conclusive
proof of identity and has to be complemented with multiple other proofs of identity
such as passwords, SSN, or other user identifiers. Multi-factor authentication mechanisms
are thus required to enforce strong authentication based on the biometric
and identifiers of other nature.
In this paper we propose a two-phase authentication mechanism for federated
identity management systems. The first phase consists of a two-factor biometric
authentication based on zero knowledge proofs. We employ techniques from the
vector-space model to generate cryptographic biometric keys. These keys are kept
secret, thus preserving the confidentiality of the biometric data, and at the same
time exploit the advantages of biometric authentication. The second phase combines
several authentication factors in conjunction with the biometric to provide a
strong authentication. A key advantage of our approach is that any unanticipated
combination of factors can be used. Such authentication system leverages the information
of the user that are available from the federated identity management
system.(2007) Privacy Preserving Multi-Factor Authentication with Biometrics

(2007) Privacy Preserving Multi-Factor Authentication with BiometricsInternational Center for Biometric Research
Semelhante a Problems with biometric authentication (20)
Biometric Authentication: The Evolution, Applications, Benefits and Challenge...

Biometric Authentication: The Evolution, Applications, Benefits and Challenge...
Multi-factor Implicit Biometric Authentication: Analysis and Approach

Multi-factor Implicit Biometric Authentication: Analysis and Approach
Privacypreservingauthenticationbiometrics 100228075830-phpapp02

Privacypreservingauthenticationbiometrics 100228075830-phpapp02
The Rise of Behavioral Biometrics and Its Potential Applications.pdf

The Rise of Behavioral Biometrics and Its Potential Applications.pdf
(2007) Privacy Preserving Multi-Factor Authentication with Biometrics

(2007) Privacy Preserving Multi-Factor Authentication with Biometrics
An Efficient User VErification System via Mouse Movements

An Efficient User VErification System via Mouse Movements
Fingerprint Authentication Using Biometric And Aadhar Card Fingerprint

Fingerprint Authentication Using Biometric And Aadhar Card Fingerprint
74560 computer controlled biometric based access control

74560 computer controlled biometric based access control
Seminar report on Error Handling methods used in bio-cryptography

Seminar report on Error Handling methods used in bio-cryptography
Mais de ArrayShield Technologies Private Limited (6)
Último
Último (20)
HTML Injection Attacks: Impact and Mitigation Strategies

HTML Injection Attacks: Impact and Mitigation Strategies
Top 10 Most Downloaded Games on Play Store in 2024

Top 10 Most Downloaded Games on Play Store in 2024
TrustArc Webinar - Unlock the Power of AI-Driven Data Discovery

TrustArc Webinar - Unlock the Power of AI-Driven Data Discovery
Powerful Google developer tools for immediate impact! (2023-24 C)

Powerful Google developer tools for immediate impact! (2023-24 C)
ProductAnonymous-April2024-WinProductDiscovery-MelissaKlemke

ProductAnonymous-April2024-WinProductDiscovery-MelissaKlemke
Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME

Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME
How to Troubleshoot Apps for the Modern Connected Worker

How to Troubleshoot Apps for the Modern Connected Worker
Boost Fertility New Invention Ups Success Rates.pdf

Boost Fertility New Invention Ups Success Rates.pdf
Tata AIG General Insurance Company - Insurer Innovation Award 2024

Tata AIG General Insurance Company - Insurer Innovation Award 2024
From Event to Action: Accelerate Your Decision Making with Real-Time Automation

From Event to Action: Accelerate Your Decision Making with Real-Time Automation
Understanding Discord NSFW Servers A Guide for Responsible Users.pdf

Understanding Discord NSFW Servers A Guide for Responsible Users.pdf
Bajaj Allianz Life Insurance Company - Insurer Innovation Award 2024

Bajaj Allianz Life Insurance Company - Insurer Innovation Award 2024
AWS Community Day CPH - Three problems of Terraform

AWS Community Day CPH - Three problems of Terraform
The 7 Things I Know About Cyber Security After 25 Years | April 2024

The 7 Things I Know About Cyber Security After 25 Years | April 2024
Top 5 Benefits OF Using Muvi Live Paywall For Live Streams

Top 5 Benefits OF Using Muvi Live Paywall For Live Streams
Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...

Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...
Problems with biometric authentication
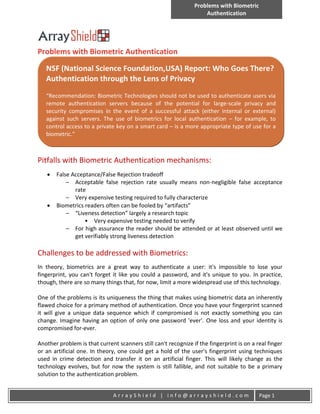
- 1. Problems with Biometric Authentication Problems with Biometric Authentication NSF (National Science Foundation,USA) Report: Who Goes There? Authentication through the Lens of Privacy “Recommendation: Biometric Technologies should not be used to authenticate users via remote authentication servers because of the potential for large-scale privacy and security compromises in the event of a successful attack (either internal or external) against such servers. The use of biometrics for local authentication – for example, to control access to a private key on a smart card – is a more appropriate type of use for a biometric.” Pitfalls with Biometric Authentication mechanisms: False Acceptance/False Rejection tradeoff – Acceptable false rejection rate usually means non-negligible false acceptance rate – Very expensive testing required to fully characterize Biometrics readers often can be fooled by “artifacts” – “Liveness detection” largely a research topic • Very expensive testing needed to verify – For high assurance the reader should be attended or at least observed until we get verifiably strong liveness detection Challenges to be addressed with Biometrics: In theory, biometrics are a great way to authenticate a user: it's impossible to lose your fingerprint, you can't forget it like you could a password, and it's unique to you. In practice, though, there are so many things that, for now, limit a more widespread use of this technology. One of the problems is its uniqueness the thing that makes using biometric data an inherently flawed choice for a primary method of authentication. Once you have your fingerprint scanned it will give a unique data sequence which if compromised is not exactly something you can change. Imagine having an option of only one password 'ever'. One loss and your identity is compromised for-ever. Another problem is that current scanners still can't recognize if the fingerprint is on a real finger or an artificial one. In theory, one could get a hold of the user's fingerprint using techniques used in crime detection and transfer it on an artificial finger. This will likely change as the technology evolves, but for now the system is still fallible, and not suitable to be a primary solution to the authentication problem. ArrayShield | info@arrayshield.com Page 1
