Dp2
•
0 likes•245 views
Definition of personal data and processing
Report
Share
Report
Share
Recommended
Recommended
The General Data Protection Regulation (GDPR) regulates the personal data management whithin companies.
It aims to better protect all citizens of the European Union by harmonizing the protection of personal data in all 28 Member States.GDPR all concerned! Essential Issues of the General Data Protection Regulatio...

GDPR all concerned! Essential Issues of the General Data Protection Regulatio...EnjoyDigitAll by BNP Paribas
More Related Content
Viewers also liked
Viewers also liked (6)
Similar to Dp2
The General Data Protection Regulation (GDPR) regulates the personal data management whithin companies.
It aims to better protect all citizens of the European Union by harmonizing the protection of personal data in all 28 Member States.GDPR all concerned! Essential Issues of the General Data Protection Regulatio...

GDPR all concerned! Essential Issues of the General Data Protection Regulatio...EnjoyDigitAll by BNP Paribas
Similar to Dp2 (20)
GDPR all concerned! Essential Issues of the General Data Protection Regulatio...

GDPR all concerned! Essential Issues of the General Data Protection Regulatio...
Privacy and data protection primer - City of Portland

Privacy and data protection primer - City of Portland
Personally Identifiable Information - GlossaryAggregated Infor.docx

Personally Identifiable Information - GlossaryAggregated Infor.docx
Personally Identifiable Information - GlossaryAggregated Infor.docx

Personally Identifiable Information - GlossaryAggregated Infor.docx
Christopher Millard Legally Compliant Use Of Personal Data In E Social Science

Christopher Millard Legally Compliant Use Of Personal Data In E Social Science
Privacy through Anonymisation in Large-scale Socio-technical Systems: Multi-l...

Privacy through Anonymisation in Large-scale Socio-technical Systems: Multi-l...
Protection and defense against sensitive data leakage problem within organiza...

Protection and defense against sensitive data leakage problem within organiza...
Protection and defense against sensitive data leakage problem within organiza...

Protection and defense against sensitive data leakage problem within organiza...
More from Tommy Vandepitte
More from Tommy Vandepitte (20)
Gegevensbescherming-clausule in (overheids)opdracht

Gegevensbescherming-clausule in (overheids)opdracht
20190131 - Presentation Q&A on legislation's influence (on travel management)

20190131 - Presentation Q&A on legislation's influence (on travel management)
Recently uploaded
VVVIP Call Girls In Greater Kailash ➡️ Delhi ➡️ 9999965857 🚀 No Advance 24HRS Live
Booking Contact Details :-
WhatsApp Chat :- [+91-9999965857 ]
The Best Call Girls Delhi At Your Service
Russian Call Girls Delhi Doing anything intimate with can be a wonderful way to unwind from life's stresses, while having some fun. These girls specialize in providing sexual pleasure that will satisfy your fetishes; from tease and seduce their clients to keeping it all confidential - these services are also available both install and outcall, making them great additions for parties or business events alike. Their expert sex skills include deep penetration, oral sex, cum eating and cum eating - always respecting your wishes as part of the experience
(07-May-2024(PSS)VVVIP Call Girls In Greater Kailash ➡️ Delhi ➡️ 9999965857 🚀 No Advance 24HRS...

VVVIP Call Girls In Greater Kailash ➡️ Delhi ➡️ 9999965857 🚀 No Advance 24HRS...Call Girls In Delhi Whatsup 9873940964 Enjoy Unlimited Pleasure
Recently uploaded (20)
Call Girls In Noida 959961⊹3876 Independent Escort Service Noida

Call Girls In Noida 959961⊹3876 Independent Escort Service Noida
Uneak White's Personal Brand Exploration Presentation

Uneak White's Personal Brand Exploration Presentation
MONA 98765-12871 CALL GIRLS IN LUDHIANA LUDHIANA CALL GIRL

MONA 98765-12871 CALL GIRLS IN LUDHIANA LUDHIANA CALL GIRL
FULL ENJOY Call Girls In Mahipalpur Delhi Contact Us 8377877756

FULL ENJOY Call Girls In Mahipalpur Delhi Contact Us 8377877756
VVVIP Call Girls In Greater Kailash ➡️ Delhi ➡️ 9999965857 🚀 No Advance 24HRS...

VVVIP Call Girls In Greater Kailash ➡️ Delhi ➡️ 9999965857 🚀 No Advance 24HRS...
Quick Doctor In Kuwait +2773`7758`557 Kuwait Doha Qatar Dubai Abu Dhabi Sharj...

Quick Doctor In Kuwait +2773`7758`557 Kuwait Doha Qatar Dubai Abu Dhabi Sharj...
BAGALUR CALL GIRL IN 98274*61493 ❤CALL GIRLS IN ESCORT SERVICE❤CALL GIRL

BAGALUR CALL GIRL IN 98274*61493 ❤CALL GIRLS IN ESCORT SERVICE❤CALL GIRL
Falcon's Invoice Discounting: Your Path to Prosperity

Falcon's Invoice Discounting: Your Path to Prosperity
Insurers' journeys to build a mastery in the IoT usage

Insurers' journeys to build a mastery in the IoT usage
Chandigarh Escorts Service 📞8868886958📞 Just📲 Call Nihal Chandigarh Call Girl...

Chandigarh Escorts Service 📞8868886958📞 Just📲 Call Nihal Chandigarh Call Girl...
👉Chandigarh Call Girls 👉9878799926👉Just Call👉Chandigarh Call Girl In Chandiga...

👉Chandigarh Call Girls 👉9878799926👉Just Call👉Chandigarh Call Girl In Chandiga...
Call Girls Hebbal Just Call 👗 7737669865 👗 Top Class Call Girl Service Bangalore

Call Girls Hebbal Just Call 👗 7737669865 👗 Top Class Call Girl Service Bangalore
B.COM Unit – 4 ( CORPORATE SOCIAL RESPONSIBILITY ( CSR ).pptx

B.COM Unit – 4 ( CORPORATE SOCIAL RESPONSIBILITY ( CSR ).pptx
0183760ssssssssssssssssssssssssssss00101011 (27).pdf

0183760ssssssssssssssssssssssssssss00101011 (27).pdf
Mysore Call Girls 8617370543 WhatsApp Number 24x7 Best Services

Mysore Call Girls 8617370543 WhatsApp Number 24x7 Best Services
Dp2
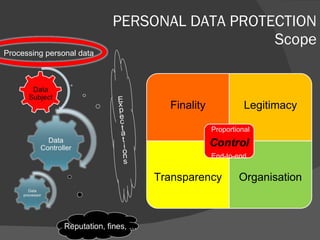
- 1. PERSONAL DATA PROTECTION Scope Processing personal data Finality Legitimacy Transparency Organisation Proportional End-to-end
- 4. Source: 32nd International Conference of Data Protection and Privacy Commissioners (2010)
Editor's Notes
- 05/12/10