BCIT's Technology Management Strategy and Policy Presentation
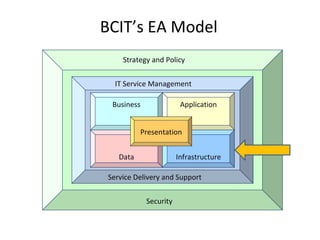
- 1. BCIT’s EA Model IT Service Management Strategy and Policy Business Data Application Infrastructure Presentation Service Delivery and Support Security
- 5. Building a Technology Matrix Sept 2006 Nov 2006 Jan 2007 Feb 2007 Ongoing … Create Technology Matrix Template Pilot With Oracle Technology Establish “ Watcher” Role (Vendor) Add Other Vendor Watchers Migrate Vendor Watchers to Domains
- 6. Technology Lifecycle R & D Invest End of Life Watch
- 7. Technology Lifecycle Definitions Watching (W): includes initiatives and technologies that are being watched for maturity in industry. Research and Development (R): includes initiatives and technologies that are currently under consideration, investigation, or evaluation for future implementation. Investing (I): includes initiatives and technologies that are the target of resources including financial investments and/or investments of human resources.
- 8. Technology Lifecycle Definitions Sustaining (S): includes initiatives and technologies that deliver services identified in the Core Services Catalogue or in Service Level Agreements Containing (C): includes initiatives that have been completed and technologies that are in the process of being phased out. End of Life (E): includes initiatives and Technologies that are retired from service
- 10. Technology Matrix - Oracle Oracle The purpose of this document is to capture BCIT's investment in Oracle technologies. Oracle provides several technology services to the Institute and this document will be made publically available for all BCIT stakeholders access. Watching (W) Research and Development (R) Investing (I) Sustaining (S) Containing (C) End of Life (E) Service Name/Technology Database Comment 2007 S1 2007 S2 2008 S1 2008 S2 2009 S1 2009 S2 Enterprise Manager - DBConsole 10.1.2.02 plan to implement for fall 2007 I I S S S S DataGuard Looking at for Disaster Recovery R R I S S S RDBMS 9.2.0.4 (9i) currently run in production for Autosys job scheduler C C C C E E RDBMS 9.2.0.6 (9i) currently run in production for ERP and BI S S C C E E RDBMS 10.1.2.02 (10G) plan to implement for fall 2007 I I S S S C RDBMS 11 just announced W W W W R R
- 11. Technology Chg Report - Oracle Service Name/Technology Application Development Comment 2007 S1 2007 S2 JDK 1.4.2_12 need to install for DST change R I Business Intelligence and Data Warehouse Comment 2007 S1 2007 S2 Oracle Warehouse Builder 10g rel 2 plan to implement an R&D project W R Client Software Comment 2007 S1 2007 S2 Jinitiator 1.3.1.26 need to install for DST change R I
Editor's Notes
- Prior to 2006, IT Services at BCIT managed applications independently in our various groups. There was little discussion or coordination between groups resulting in several groups implementing many different applications that essentially served the same functional purpose.
- Prior to 2006, IT Services at BCIT managed applications independently in our various groups. There was little discussion or coordination between groups resulting in several groups implementing many different applications that essentially served the same functional purpose.
- Prior to 2006, IT Services at BCIT managed applications independently in our various groups. There was little discussion or coordination between groups resulting in several groups implementing many different applications that essentially served the same functional purpose.
- We began building our first draft portfolio in June 2006. This took some time as there was resistance to creation of the List. By late September, the majority of the list was compiled and we published it internally. An interesting thing occurred, once we published the first version of the portfolio. People at our service desk loved it and could see the value right away. Our identity management team took advantage of the list to identify key applications that we wanted to enable with IDM. Another by-product of publishing the list was, that those people who did not want to give up their “secrets” began to reveal applications that we knew nothing about. The list will continue to be updated and published regularly and will become part of our Enterprise Model.
