Security coding
•
1 like•1,051 views
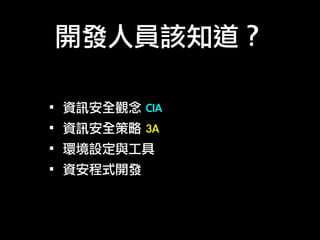
The knowledge programmers need to know!
Report
Share
Report
Share
Download to read offline
Recommended
Recommended
This talk provides an introduction and detailed overview of Java deserialization attacks. You will understand the basic concepts of how Java deserialization exploits (gadget chains) work, what solutions exist and the advantages and disadvantages of each. Finally, a new approach will be presented, using Runtime Virtualization, Compartmentalization and Privilege De-escalation.
This talk was presented by Apostolos Giannakidis at the OWASP London meetup on May 2017.Unsafe Deserialization Attacks In Java and A New Approach To Protect The JVM ...

Unsafe Deserialization Attacks In Java and A New Approach To Protect The JVM ...Apostolos Giannakidis
More Related Content
Similar to Security coding
This talk provides an introduction and detailed overview of Java deserialization attacks. You will understand the basic concepts of how Java deserialization exploits (gadget chains) work, what solutions exist and the advantages and disadvantages of each. Finally, a new approach will be presented, using Runtime Virtualization, Compartmentalization and Privilege De-escalation.
This talk was presented by Apostolos Giannakidis at the OWASP London meetup on May 2017.Unsafe Deserialization Attacks In Java and A New Approach To Protect The JVM ...

Unsafe Deserialization Attacks In Java and A New Approach To Protect The JVM ...Apostolos Giannakidis
Similar to Security coding (20)
What Does a Full Featured Security Strategy Look Like?

What Does a Full Featured Security Strategy Look Like?
Unsafe Deserialization Attacks In Java and A New Approach To Protect The JVM ...

Unsafe Deserialization Attacks In Java and A New Approach To Protect The JVM ...
What is tackled in the Java EE Security API (Java EE 8)

What is tackled in the Java EE Security API (Java EE 8)
Ved du, hvor dine data er - og hvem, der har adgang til dem? Ron Ben Natan, I...

Ved du, hvor dine data er - og hvem, der har adgang til dem? Ron Ben Natan, I...
Vulnerable Active Record: A tale of SQL Injection in PHP Framework

Vulnerable Active Record: A tale of SQL Injection in PHP Framework
Bsidesnova- Pentesting Methodology - Making bits less complicated

Bsidesnova- Pentesting Methodology - Making bits less complicated
More from BITs Information Technology Consultants Co., Ltd.
More from BITs Information Technology Consultants Co., Ltd. (10)
Recently uploaded
💉💊+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHABI}}+971581248768
+971581248768 Mtp-Kit (500MG) Prices » Dubai [(+971581248768**)] Abortion Pills For Sale In Dubai, UAE, Mifepristone and Misoprostol Tablets Available In Dubai, UAE CONTACT DR.Maya Whatsapp +971581248768 We Have Abortion Pills / Cytotec Tablets /Mifegest Kit Available in Dubai, Sharjah, Abudhabi, Ajman, Alain, Fujairah, Ras Al Khaimah, Umm Al Quwain, UAE, Buy cytotec in Dubai +971581248768''''Abortion Pills near me DUBAI | ABU DHABI|UAE. Price of Misoprostol, Cytotec” +971581248768' Dr.DEEM ''BUY ABORTION PILLS MIFEGEST KIT, MISOPROTONE, CYTOTEC PILLS IN DUBAI, ABU DHABI,UAE'' Contact me now via What's App…… abortion Pills Cytotec also available Oman Qatar Doha Saudi Arabia Bahrain Above all, Cytotec Abortion Pills are Available In Dubai / UAE, you will be very happy to do abortion in Dubai we are providing cytotec 200mg abortion pill in Dubai, UAE. Medication abortion offers an alternative to Surgical Abortion for women in the early weeks of pregnancy. We only offer abortion pills from 1 week-6 Months. We then advise you to use surgery if its beyond 6 months. Our Abu Dhabi, Ajman, Al Ain, Dubai, Fujairah, Ras Al Khaimah (RAK), Sharjah, Umm Al Quwain (UAQ) United Arab Emirates Abortion Clinic provides the safest and most advanced techniques for providing non-surgical, medical and surgical abortion methods for early through late second trimester, including the Abortion By Pill Procedure (RU 486, Mifeprex, Mifepristone, early options French Abortion Pill), Tamoxifen, Methotrexate and Cytotec (Misoprostol). The Abu Dhabi, United Arab Emirates Abortion Clinic performs Same Day Abortion Procedure using medications that are taken on the first day of the office visit and will cause the abortion to occur generally within 4 to 6 hours (as early as 30 minutes) for patients who are 3 to 12 weeks pregnant. When Mifepristone and Misoprostol are used, 50% of patients complete in 4 to 6 hours; 75% to 80% in 12 hours; and 90% in 24 hours. We use a regimen that allows for completion without the need for surgery 99% of the time. All advanced second trimester and late term pregnancies at our Tampa clinic (17 to 24 weeks or greater) can be completed within 24 hours or less 99% of the time without the need surgery. The procedure is completed with minimal to no complications. Our Women's Health Center located in Abu Dhabi, United Arab Emirates, uses the latest medications for medical abortions (RU-486, Mifeprex, Mifegyne, Mifepristone, early options French abortion pill), Methotrexate and Cytotec (Misoprostol). The safety standards of our Abu Dhabi, United Arab Emirates Abortion Doctors remain unparalleled. They consistently maintain the lowest complication rates throughout the nation. Our Physicians and staff are always available to answer questions and care for women in one of the most difficult times in their lives. The decision to have an abortion at the Abortion Cl+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...

+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...?#DUbAI#??##{{(☎️+971_581248768%)**%*]'#abortion pills for sale in dubai@
Recently uploaded (20)
Tata AIG General Insurance Company - Insurer Innovation Award 2024

Tata AIG General Insurance Company - Insurer Innovation Award 2024
Bajaj Allianz Life Insurance Company - Insurer Innovation Award 2024

Bajaj Allianz Life Insurance Company - Insurer Innovation Award 2024
2024: Domino Containers - The Next Step. News from the Domino Container commu...

2024: Domino Containers - The Next Step. News from the Domino Container commu...
Repurposing LNG terminals for Hydrogen Ammonia: Feasibility and Cost Saving

Repurposing LNG terminals for Hydrogen Ammonia: Feasibility and Cost Saving
Axa Assurance Maroc - Insurer Innovation Award 2024

Axa Assurance Maroc - Insurer Innovation Award 2024
Strategies for Landing an Oracle DBA Job as a Fresher

Strategies for Landing an Oracle DBA Job as a Fresher
Scaling API-first – The story of a global engineering organization

Scaling API-first – The story of a global engineering organization
The 7 Things I Know About Cyber Security After 25 Years | April 2024

The 7 Things I Know About Cyber Security After 25 Years | April 2024
From Event to Action: Accelerate Your Decision Making with Real-Time Automation

From Event to Action: Accelerate Your Decision Making with Real-Time Automation
Apidays Singapore 2024 - Building Digital Trust in a Digital Economy by Veron...

Apidays Singapore 2024 - Building Digital Trust in a Digital Economy by Veron...
Why Teams call analytics are critical to your entire business

Why Teams call analytics are critical to your entire business
Powerful Google developer tools for immediate impact! (2023-24 C)

Powerful Google developer tools for immediate impact! (2023-24 C)
+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...

+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...
Boost Fertility New Invention Ups Success Rates.pdf

Boost Fertility New Invention Ups Success Rates.pdf
Security coding
- 1. 開發人員該知道? ·•資訊安全觀念 CIA ·•資訊安全策略 3A ·•環境設定與工具 ·•資安程式開發
- 4. Secure Coding Guidelines • Avoid duplication • Restrict privileges • Establish trust boundaries • Minimize the number of permission checks • Encapsulate
- 5. Denial of Service • Release resources in all cases • "Zip bombs" • "Billion laughs attack" • "Log bombs" • Infinite loops: "Messages poison” • Resource limit checks should not suffer from integer overflow
- 6. Confidential Information • Purge sensitive information from exceptions • Do not log highly sensitive information • Consider purging highly sensitive from memory after use
- 7. Injection & Inclusion • Avoid dynamic SQL • SQL Injection • XML and HTML generation requires care • Cross Site Scripting(XSS) • Restrict XML inclusion • XML External Entity (XXE)
- 8. Accessibility & Extensibility • Limit the accessibility of classes, interfaces, methods, and fields. • Limit the accessibility of namespace. • Isolate unrelated code. • Limit the extensibility of classes and methods. • Understand how a superclass can affect subclass behavior.
- 9. Accessibility & Extensibility Reducing the "attack surface" of the code
- 10. Input Validation • Validate inputs • 有效值 • 特殊字元:URL / HTML / XML
- 11. Mutability • Prefer immutability for value types • Create copies of mutable output values • Make public static fields as constants • Do not expose mutable statics
- 12. Object Construction • Avoid exposing constructors of sensitive classes • Prevent the unauthorized construction of sensitive classes • Prevent constructors from calling methods that can be overridden
- 13. Serialization & Deserialization • Avoid serialization for security-sensitive classes • Guard sensitive data during serialization • View deserialization the same as object construction
- 14. Access Control • Understand how permissions are checked • Beware of callback (Lifecycle) methods • Callback methods are generally invoked from the system with FULL permissions • Be careful caching results of potentially privileged operations
- 15. Security Coding 涵蓋了? ·•Authentication & Authorization ·•Session & State management ·•Input & Output ·•File Handling ·•Error Handling ·•Auditing & Logging ·•Cryptography ·•Configuration
- 17. 使⽤用適當⼯工具
- 18. 資訊分級 • ERROR • WARN • INFO • DEBUG • TRACE
- 19. 到底在Log啥? Debug.WriteLine("Returning orders: {0}", orders); if(MyLog.isDebugEnabled()){ MyLog.Debug("It's a secret!”); }
- 20. 避免副作⽤用! try { MyLog.Trace("Id=" + request.getUser().getId() ); MyLog.Trace("Accesses " + manager.getPage().getUrl().toString()); } catch(Exception e) { }
- 21. 簡潔描述! if(message is TextMessage) //... else MyLog.Warn("Unknown message type");
- 22. 精確調整輸出格式! 時戳 等級 程式名稱 訊息 {0:HH:mm:ss} {1} {2} {3}
- 23. 記錄⽅方法參數與回傳值! public String printDocument(Document doc, Mode mode) { MyLog.Debug("Entering printDocument(doc={0}, mode={1})", doc, mode); String id = //... MyLog.Debug("Leaving printDocument(): {0}", id); return id; }
- 24. 記錄例外狀況資訊! MyLog.Error("IO exception", e); throw new MyCustomException(e);
- 25. 易於解讀! MyLog.Debug("Request TTL set to: {0} ({1})", new DateTime(ttl), ttl); // Request TTL set to: Wed Apr 28 20:14:12 CEST 2010 (1272478452437) ! String duration = DurationFormatUtils.formatDurationWords(durationMillis, true, true); MyLog.Info("Importing took: {0}ms ({1})", durationMillis, duration); // Importing took: 123456789ms (1 day 10 hours 17 minutes 36 seconds)
- 26. Summary ·•Use for daily log or tracing ·•Audience ·•Easy to read ·•Easy to analysis ·•Will it cause error? ·•System performance issue
- 27. Why Secure Coding Training is Important? Cost% Cost%of%fixing%security%flaws%during%different%development%phases% Phases% Fixing&bugs&by&releasing&a&patch&costs&60&6mes&more&than&fixing&the&same&bug&during&the&design&stage.& Source:&h"p://www.auto.tuwien.ac.at0
