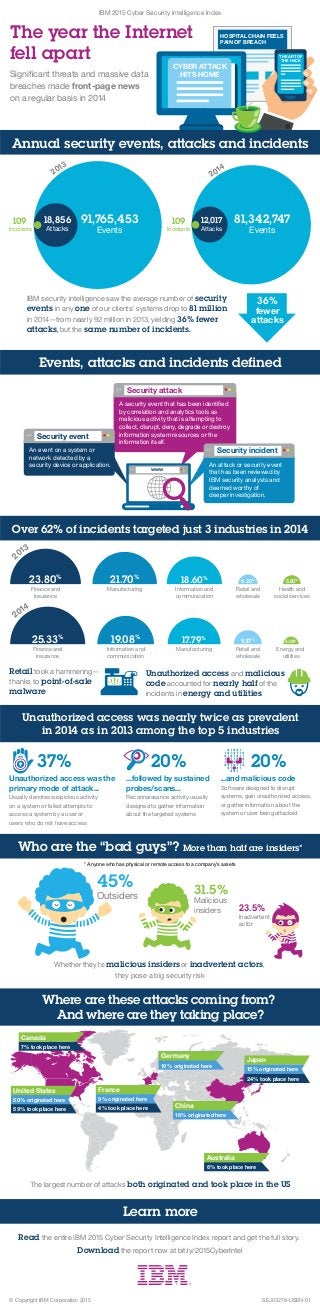
Infographic: IBM 2015 Cyber Security Intelligence Index
•
1 like•7,978 views
Significant threats and massive data breaches made front-page news on a regular basis in 2014. Read the entire IBM 2015 Cyber Security Intelligence Index report and get the full story. Download the report now at bit.ly/2015CyberIntel
Report
Share
Report
Share
Download to read offline
Recommended
Recommended
More Related Content
Viewers also liked
Viewers also liked (9)
Considerations and examples for key performance indicators design

Considerations and examples for key performance indicators design
More from IBM Security
More from IBM Security (20)
Leaders & Laggards: The Latest Findings from the Ponemon Institute’s Study on...

Leaders & Laggards: The Latest Findings from the Ponemon Institute’s Study on...
Bridging the Gap between Privacy and Security: Using Technology to Manage Com...

Bridging the Gap between Privacy and Security: Using Technology to Manage Com...
The Resilient End-of-Year Review: The Top Cyber Security Trends in 2018 and P...

The Resilient End-of-Year Review: The Top Cyber Security Trends in 2018 and P...
Leveraging Validated and Community Apps to Build a Versatile and Orchestrated...

Leveraging Validated and Community Apps to Build a Versatile and Orchestrated...
Accelerating SOC Transformation with IBM Resilient and Carbon Black

Accelerating SOC Transformation with IBM Resilient and Carbon Black
How to Build a Faster, Laser-Sharp SOC with Intelligent Orchestration

How to Build a Faster, Laser-Sharp SOC with Intelligent Orchestration
Orchestrate Your Security Defenses to Optimize the Impact of Threat Intelligence

Orchestrate Your Security Defenses to Optimize the Impact of Threat Intelligence
Your Mainframe Environment is a Treasure Trove: Is Your Sensitive Data Protec...

Your Mainframe Environment is a Treasure Trove: Is Your Sensitive Data Protec...
Meet the New IBM i2 QRadar Offense Investigator App and Start Threat Hunting ...

Meet the New IBM i2 QRadar Offense Investigator App and Start Threat Hunting ...
Understanding the Impact of Today's Security Breaches: The 2017 Ponemon Cost ...

Understanding the Impact of Today's Security Breaches: The 2017 Ponemon Cost ...
How to Improve Threat Detection & Simplify Security Operations

How to Improve Threat Detection & Simplify Security Operations
Orchestrate Your Security Defenses; Protect Against Insider Threats 

Orchestrate Your Security Defenses; Protect Against Insider Threats
Recently uploaded
Recently uploaded (20)
Tech Trends Report 2024 Future Today Institute.pdf

Tech Trends Report 2024 Future Today Institute.pdf
Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...

Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...
IAC 2024 - IA Fast Track to Search Focused AI Solutions

IAC 2024 - IA Fast Track to Search Focused AI Solutions
Axa Assurance Maroc - Insurer Innovation Award 2024

Axa Assurance Maroc - Insurer Innovation Award 2024
Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...

Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...
What Are The Drone Anti-jamming Systems Technology?

What Are The Drone Anti-jamming Systems Technology?
Exploring the Future Potential of AI-Enabled Smartphone Processors

Exploring the Future Potential of AI-Enabled Smartphone Processors
Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff

Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff
Powerful Google developer tools for immediate impact! (2023-24 C)

Powerful Google developer tools for immediate impact! (2023-24 C)
From Event to Action: Accelerate Your Decision Making with Real-Time Automation

From Event to Action: Accelerate Your Decision Making with Real-Time Automation
Apidays Singapore 2024 - Building Digital Trust in a Digital Economy by Veron...

Apidays Singapore 2024 - Building Digital Trust in a Digital Economy by Veron...
08448380779 Call Girls In Friends Colony Women Seeking Men

08448380779 Call Girls In Friends Colony Women Seeking Men
Infographic: IBM 2015 Cyber Security Intelligence Index
- 1. IBM 2015 Cyber Security Intelligence Index The year the Internet fell apart HOSPITAL CHAIN FEELS PAIN OF BREACH Significant threats and massive data breaches made front-page news on a regular basis in 2014 CYBER ATTACK HITS HOME THE ART OF THE HACK Over 62% of incidents targeted just 3 industries in 2014 Who are the “bad guys”? 45% Outsiders 31.5% Malicious insiders 23.5% Inadvertent actor * Anyone who has physical or remote access to a company’s assets Whether they’re malicious insiders or inadvertent actors, they pose a big security risk The largest number of attacks both originated and took place in the US Where are these attacks coming from? And where are they taking place? United States 50% originated here 59% took place here China 16% originated here Japan 15% originated here 24% took place here Canada 7% took place here Germany 10% originated here France 9% originated here 4% took place here Australia 6% took place here IBM security intelligence saw the average number of security events in any one of our clients’ systems drop to 81 million in 2014—from nearly 92 million in 2013, yielding 36% fewer attacks, but the same number of incidents. 36% fewer attacks Finance and insurance 23.80% Manufacturing 21.70% Information and communication 18.60% Health and social services 5.80% Retail and wholesale 6.20% Energy and utilities 5.08% Retail and wholesale 9.37% Finance and insurance 25.33% Information and communication 19.08% Manufacturing 17.79% 2013 2014 Incidents 109 Events 91,765,453 Attacks 18,856 Incidents 109 Events 81,342,747 Attacks 12,017 2013 2014 Annual security events, attacks and incidents www Security attack A security event that has been identified by correlation and analytics tools as malicious activity that is attempting to collect, disrupt, deny, degrade or destroy information system resources or the information itself. Security event An event on a system or network detected by a security device or application. Security incident An attack or security event that has been reviewed by IBM security analysts and deemed worthy of deeper investigation. Events, attacks and incidents defined Unauthorized access and malicious code accounted for nearly half of the incidents in energy and utilities Retail took a hammering— thanks to point-of-sale malware Unauthorized access was nearly twice as prevalent in 2014 as in 2013 among the top 5 industries Who are the “bad guys”? More than half are insiders* Learn more Read the entire IBM 2015 Cyber Security Intelligence Index report and get the full story. Download the report now at bit.ly/2015CyberIntel 37% Unauthorized access was the primary mode of attack... Usually denotes suspicious activity on a system or failed attempts to access a system by a user or users who do not have access 20% ...followed by sustained probes/scans... Reconnaissance activity usually designed to gather information about the targeted systems 20% ...and malicious code Software designed to disrupt systems, gain unauthorized access, or gather information about the system or user being attacked SEJ03278-USEN-01© Copyright IBM Corporation 2015
