استخدام خريطة المفاهيم في التعليم
•Download as DOC, PDF•
2 likes•1,048 views
تعليم
Report
Share
Report
Share
Recommended
Recommended
More Related Content
Viewers also liked
Viewers also liked (15)
National subjects دراسات الصف الثانى الإعدادى ترم أول

National subjects دراسات الصف الثانى الإعدادى ترم أول
Recently uploaded
Recently uploaded (20)
Portal Kombat : extension du réseau de propagande russe

Portal Kombat : extension du réseau de propagande russe
Design and Development of a Provenance Capture Platform for Data Science

Design and Development of a Provenance Capture Platform for Data Science
ASRock Industrial FDO Solutions in Action for Industrial Edge AI _ Kenny at A...

ASRock Industrial FDO Solutions in Action for Industrial Edge AI _ Kenny at A...
Event-Driven Architecture Masterclass: Integrating Distributed Data Stores Ac...

Event-Driven Architecture Masterclass: Integrating Distributed Data Stores Ac...
Harnessing Passkeys in the Battle Against AI-Powered Cyber Threats.pptx

Harnessing Passkeys in the Battle Against AI-Powered Cyber Threats.pptx
Intro to Passkeys and the State of Passwordless.pptx

Intro to Passkeys and the State of Passwordless.pptx
UiPath manufacturing technology benefits and AI overview

UiPath manufacturing technology benefits and AI overview
Hyatt driving innovation and exceptional customer experiences with FIDO passw...

Hyatt driving innovation and exceptional customer experiences with FIDO passw...
Event-Driven Architecture Masterclass: Challenges in Stream Processing

Event-Driven Architecture Masterclass: Challenges in Stream Processing
Where to Learn More About FDO _ Richard at FIDO Alliance.pdf

Where to Learn More About FDO _ Richard at FIDO Alliance.pdf
“Iamnobody89757” Understanding the Mysterious of Digital Identity.pdf

“Iamnobody89757” Understanding the Mysterious of Digital Identity.pdf
Choosing the Right FDO Deployment Model for Your Application _ Geoffrey at In...

Choosing the Right FDO Deployment Model for Your Application _ Geoffrey at In...
TrustArc Webinar - Unified Trust Center for Privacy, Security, Compliance, an...

TrustArc Webinar - Unified Trust Center for Privacy, Security, Compliance, an...
Extensible Python: Robustness through Addition - PyCon 2024

Extensible Python: Robustness through Addition - PyCon 2024
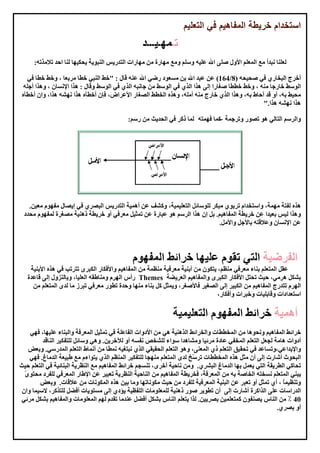
استخدام خريطة المفاهيم في التعليم
- 1. -- Themes
- 4. GIF - JPEG http://bubbl.us/edit.php http://www.mindomo.com Buzan's iMindMap V4http://thinkbuzan.com Edraw Mind Maphttp://edraw-mindmap.en.softonic.com Mind Mappingmapping.org-http://www.mind Cayrahttp://cayranet/download Inspirationhttp://www.inspiration.com SmartDrawhttp://www.smartdraw.com/exp/mim
