0 google submission
•Transferir como PPT, PDF•
0 gostou•288 visualizações
Denunciar
Compartilhar
Denunciar
Compartilhar
Mais conteúdo relacionado
Mais de Attaporn Ninsuwan
Mais de Attaporn Ninsuwan (20)
Chapter3 - Fourier Series Representation of Periodic Signals

Chapter3 - Fourier Series Representation of Periodic Signals
0 google submission
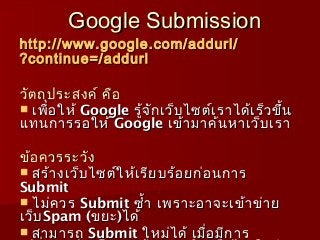
- 1. Google Submission http :// www . google . com / addurl / ?continue =/ addurl วัต ถุป ระสงค์ คือ เพื่อ ให้ Google รู้จ ัก เว็บ ไซต์เ ราได้เ ร็ว ขึ้น แทนการรอให้ Google เข้า มาค้น หาเว็บ เรา ข้อ ควรระวัง สร้า งเว็บ ไซต์ใ ห้เ รีย บร้อ ยก่อ นการ Submit ไม่ค วร Submit ซำ้า เพราะอาจะเข้า ข่า ย เว็บ Spam (ขยะ )ได้ สามารถ Submit ใหม่ไ ด้ เมื่อ มีก าร
- 2. วิธ ีก าร Submit Website
