Cryptoparty v1
•Transferir como ODP, PDF•
2 gostaram•908 visualizações
Denunciar
Compartilhar
Denunciar
Compartilhar
Recomendados
Cryptoparty: encryption and data security for journalists

Cryptoparty: encryption and data security for journalistsCentre for Media Pluralism and Media Freedom
Mais conteúdo relacionado
Destaque (8)
Quan nguyen symmetric versus asymmetric cryptography

Quan nguyen symmetric versus asymmetric cryptography
Semelhante a Cryptoparty v1
Cryptoparty: encryption and data security for journalists

Cryptoparty: encryption and data security for journalistsCentre for Media Pluralism and Media Freedom
Semelhante a Cryptoparty v1 (20)
Cryptoparty: encryption and data security for journalists

Cryptoparty: encryption and data security for journalists
CONFidence 2017: Cryptography used for jihadism, from Internet to software (J...

CONFidence 2017: Cryptography used for jihadism, from Internet to software (J...
Security & privacy on the internet: things you should now

Security & privacy on the internet: things you should now
Comparison of Anonymous Communication Networks-Tor, I2P, Freenet

Comparison of Anonymous Communication Networks-Tor, I2P, Freenet
IEEE Standards Impact in IoT and 5G, Day 2 - Architectural Requirements for S...

IEEE Standards Impact in IoT and 5G, Day 2 - Architectural Requirements for S...
New business opportunities in smart societies and industry 4.0

New business opportunities in smart societies and industry 4.0
Is Verge (XVG) About to Blow Up Crypto the Crypto Market?

Is Verge (XVG) About to Blow Up Crypto the Crypto Market?
POC 2018 - whatever talk_ Let's go OSINT using DeepWeb

POC 2018 - whatever talk_ Let's go OSINT using DeepWeb
Privacy Enhancing Technologies: Exploring the Benefits and Recommendations

Privacy Enhancing Technologies: Exploring the Benefits and Recommendations
Último
+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...

+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...?#DUbAI#??##{{(☎️+971_581248768%)**%*]'#abortion pills for sale in dubai@
Último (20)
Six Myths about Ontologies: The Basics of Formal Ontology

Six Myths about Ontologies: The Basics of Formal Ontology
DEV meet-up UiPath Document Understanding May 7 2024 Amsterdam

DEV meet-up UiPath Document Understanding May 7 2024 Amsterdam
"I see eyes in my soup": How Delivery Hero implemented the safety system for ...

"I see eyes in my soup": How Delivery Hero implemented the safety system for ...
ProductAnonymous-April2024-WinProductDiscovery-MelissaKlemke

ProductAnonymous-April2024-WinProductDiscovery-MelissaKlemke
Why Teams call analytics are critical to your entire business

Why Teams call analytics are critical to your entire business
Apidays New York 2024 - APIs in 2030: The Risk of Technological Sleepwalk by ...

Apidays New York 2024 - APIs in 2030: The Risk of Technological Sleepwalk by ...
WSO2's API Vision: Unifying Control, Empowering Developers

WSO2's API Vision: Unifying Control, Empowering Developers
AWS Community Day CPH - Three problems of Terraform

AWS Community Day CPH - Three problems of Terraform
Apidays New York 2024 - The value of a flexible API Management solution for O...

Apidays New York 2024 - The value of a flexible API Management solution for O...
Web Form Automation for Bonterra Impact Management (fka Social Solutions Apri...

Web Form Automation for Bonterra Impact Management (fka Social Solutions Apri...
Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME

Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME
Polkadot JAM Slides - Token2049 - By Dr. Gavin Wood

Polkadot JAM Slides - Token2049 - By Dr. Gavin Wood
ICT role in 21st century education and its challenges

ICT role in 21st century education and its challenges
+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...

+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...
Biography Of Angeliki Cooney | Senior Vice President Life Sciences | Albany, ...

Biography Of Angeliki Cooney | Senior Vice President Life Sciences | Albany, ...
Apidays New York 2024 - Passkeys: Developing APIs to enable passwordless auth...

Apidays New York 2024 - Passkeys: Developing APIs to enable passwordless auth...
Cryptoparty v1
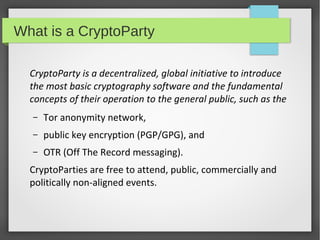
- 1. What is a CryptoParty CryptoParty is a decentralized, global initiative to introduce the most basic cryptography software and the fundamental concepts of their operation to the general public, such as the – Tor anonymity network, – public key encryption (PGP/GPG), and – OTR (Off The Record messaging). CryptoParties are free to attend, public, commercially and politically non-aligned events.
- 2. Why CryptoParty/Cryptography? ● ● When mass surveillance and data mining define our online lives, privacy and data protection acquire a whole new meaning. Citizens should be empowered to take informed decisions and resist such surveillance.
- 3. Some tools ● Lightbeam – To visualise how third parties track you when you access any website. ● Browser extensions – Do Not Track Me, HTTPSEverywhere ● Anonymous Browsing – TOR Browser ● Encrypted Emails – Thunderbird / PGP ● Password Management – Keepass ● Secure Operating Systems – TAILS
- 6. Do Not Track Me www.abine.com
- 7. Do Not Track Me www.abine.com
- 9. TOR Browser www.torproject.org Things to watch out for while using TOR – Internet speed might be reduced – Websites ask you to authenticate again – The last loop is unsecure
- 10. Encrypted Emails How emails work
- 11. Encrypted Emails
- 12. Encrypted Emails Things you need ● Email Client (Thunderbird // Claws etc) ● OpenPGP Steps to Encrypted Emails ● Setup your email client ● Generate your public and private key ● Publish your private key, if you prefer to. ● Encrypt outgoing emails using the receipients' public key ● Decrypt incoming emails using your own private key
- 13. Thank you Presentation by Surendran (@surendranb)
