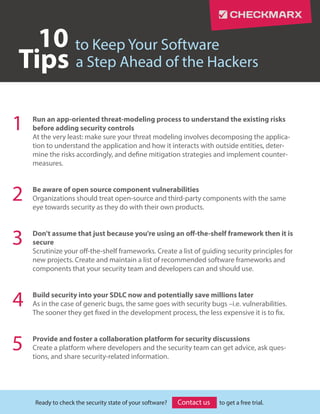
10 Tips to Keep Your Software a Step Ahead of the Hackers
- 1. http://www.checkmarx.com/contact-us/ to Keep Your Software 1 2 3 4 Ready to check the security state of your software? to get a free trial.Contact us a Step Ahead of the HackersTips 10 Run an app-oriented threat-modeling process to understand the existing risks before adding security controls At the very least: make sure your threat modeling involves decomposing the applica- tion to understand the application and how it interacts with outside entities, deter- mine the risks accordingly, and define mitigation strategies and implement counter- measures. Be aware of open source component vulnerabilities Organizations should treat open-source and third-party components with the same eye towards security as they do with their own products. Don't assume that just because you're using an off-the-shelf framework then it is secure Scrutinize your off-the-shelf frameworks. Create a list of guiding security principles for new projects. Create and maintain a list of recommended software frameworks and components that your security team and developers can and should use. Build security into your SDLC now and potentially save millions later As in the case of generic bugs, the same goes with security bugs –i.e. vulnerabilities. The sooner they get fixed in the development process, the less expensive it is to fix. Provide and foster a collaboration platform for security discussions Create a platform where developers and the security team can get advice, ask ques- tions, and share security-related information. 5
- 2. http://www.checkmarx.com/contact-us/ About Checkmarx Checkmarx provides the best way for organizations to introduce security into their Software Development Lifecycle (SDLC). The product enables developers and auditors to easily scan un-compiled code in all major coding languages and identify its security vulnerabilities. Ready to check the security state of your software? to get a free trial. Treat security requirements like checkpoints in the development process Achieve certain benchmarks within various stages of development. Benchmark loca- tions can include: during the coding or build processes, within the source code repos- itories and throughout the QA process. Never perform business-logic security checks on the client-side Don’t assume that the input is ever verified or has not been manipulated. Keeping business logic code verification on the server allows you to ensure the proper input sanitation without the concern of input manipulation. Use whitelisting instead of blacklisting when it comes to input validation Use whitelist validation on user input, defining the requests your application allows. By describing the data that is allowed to be input into the application, you greatly sift out malicious input intent on abusing the app. Always use prepared statements for web application database queries Ensure that an adversary cannot change a query’s intent, thus reducing the risk of an SQL injection, by using prepared statements. Break the build for any "high" or "medium" vulnerability findings in your app If a test comes back with major issues, it’s time to break the build and make sure those vulnerabilities are fixed before the next step. 6 7 8 9 10 Contact us
