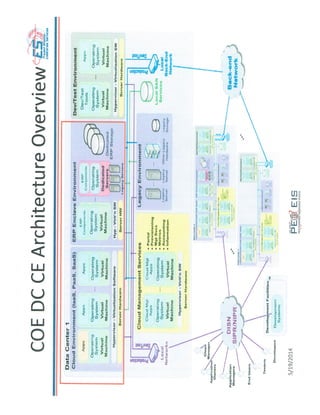
Army PEO EIS Cloud Architecture
•
0 likes•1,900 views
Army PEO EIS Cloud Architecture
Report
Share
Report
Share
Download to read offline
Recommended
Recommended
More Related Content
Viewers also liked
Viewers also liked (8)
Deep Organisational Transformation a model for a higher Agility

Deep Organisational Transformation a model for a higher Agility
Converged IoT Systems: Bringing the Data Center to the Edge of Everything

Converged IoT Systems: Bringing the Data Center to the Edge of Everything
DevOps and Continuous Delivery reference architectures for Docker

DevOps and Continuous Delivery reference architectures for Docker
Grafana is not enough: DIY user interfaces for Prometheus

Grafana is not enough: DIY user interfaces for Prometheus
More from GovCloud Network
More from GovCloud Network (20)
Vets 360 Services - Military Dedication - Corporate Success

Vets 360 Services - Military Dedication - Corporate Success
DoD Business Capability Lifecycle (BCL) Guide (Draft)

DoD Business Capability Lifecycle (BCL) Guide (Draft)
PM ISE Information Interoperability Presentation -agile sourcing brief

PM ISE Information Interoperability Presentation -agile sourcing brief
Intrusion Detection on Public IaaS - Kevin L. Jackson

Intrusion Detection on Public IaaS - Kevin L. Jackson
A Framework for Cloud Computing Adoption in South African Government

A Framework for Cloud Computing Adoption in South African Government
Paving the Way to the Cloud: Cloud Services Brokerage for Highly Secure, Dem...

Paving the Way to the Cloud: Cloud Services Brokerage for Highly Secure, Dem...
Government cloud deployment lessons learned final (4 4 2013)

Government cloud deployment lessons learned final (4 4 2013)
Kevin jackson cloud service brokerage for datacenter service providers for we...

Kevin jackson cloud service brokerage for datacenter service providers for we...
Texas Dept of Information Resources Agency Strategic Plan

Texas Dept of Information Resources Agency Strategic Plan
Recently uploaded
Recently uploaded (20)
08448380779 Call Girls In Friends Colony Women Seeking Men

08448380779 Call Girls In Friends Colony Women Seeking Men
The Role of Taxonomy and Ontology in Semantic Layers - Heather Hedden.pdf

The Role of Taxonomy and Ontology in Semantic Layers - Heather Hedden.pdf
Tata AIG General Insurance Company - Insurer Innovation Award 2024

Tata AIG General Insurance Company - Insurer Innovation Award 2024
Presentation on how to chat with PDF using ChatGPT code interpreter

Presentation on how to chat with PDF using ChatGPT code interpreter
Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...

Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...
Breaking the Kubernetes Kill Chain: Host Path Mount

Breaking the Kubernetes Kill Chain: Host Path Mount
Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...

Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...
Advantages of Hiring UIUX Design Service Providers for Your Business

Advantages of Hiring UIUX Design Service Providers for Your Business
Scaling API-first – The story of a global engineering organization

Scaling API-first – The story of a global engineering organization
[2024]Digital Global Overview Report 2024 Meltwater.pdf![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[2024]Digital Global Overview Report 2024 Meltwater.pdf
What Are The Drone Anti-jamming Systems Technology?

What Are The Drone Anti-jamming Systems Technology?
08448380779 Call Girls In Greater Kailash - I Women Seeking Men

08448380779 Call Girls In Greater Kailash - I Women Seeking Men
Factors to Consider When Choosing Accounts Payable Services Providers.pptx

Factors to Consider When Choosing Accounts Payable Services Providers.pptx
Powerful Google developer tools for immediate impact! (2023-24 C)

Powerful Google developer tools for immediate impact! (2023-24 C)
