Csaw research poster_20071204
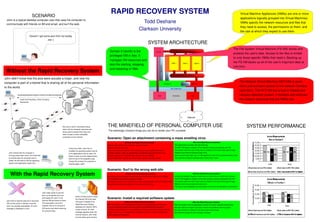
- 1. SCENARIO RAPID RECOVERY SYSTEM Virtual Machine Appliances (VMAs) are one or more applications logically grouped into Virtual Machines. John is a typical desktop computer user that uses his computer to communicate with friends on IM and email, and surf the web. Todd Deshane VMAs specify the network resources and files that they need to access, the permissions on them, and Clarkson University the rate at which they expect to use them. Ooooh! I got some pics from my buddy Joe :) SYSTEM ARCHITECTURE The File System Virtual Machine (FSVM) stores and Domain 0 (dom0) is the protects the user's data. Access to the files is limited privileged VM in Xen. It to only those specific VMAs that need it. Backing up manages VM resources and the FSVM backs up all of the user's important data at also the starting, stopping, one time. Without the Rapid Recovery System and restarting of VMs. John didn't know that the pics were actually a trojan, and now his computer is part of a botnet that is sharing all of his personal information The Network Virtual Machine (NETVM) is given to the world. direct and exclusive access to the network interface card (NIC). The NETVM has a builtin firewall and 010010000100000101000011010010110100010101000100 intrusion detection system. It monitors and enforces Credit Card Numbers, Email Contacts, the network resources that the VMAs use. Passwords Not only is John's information being THE MINEFIELD OF PERSONAL COMPUTER USE SYSTEM PERFORMANCE taken, but his computer resources are being used to spread this trojan and The seemingly innocent things you can do to render your PC unusable other viruses to other vulnerable computers on the Internet. Scenario: Open an attachment containing a mass emailing virus Without the Rapid Recovery System With the Rapid Recovery System Notice a slow down of the machine, unsure of cause. The attachment is written into the email log. Reboot machine, still slow. The NETVM flags a violation of the network contract and pauses the VM. A few hours later, John has re Look in process list, attempt to kill suspicious process, regenerates itself. The system asks the user if they want to rollback to the last known good image. installed his operating system and all John notices that his computer is Call tech support, make an appointment to take the computer into the shop. Rollback and remount personal data store. of his applications that he uses. He running slower than usual. He is told that 3 weeks later get the machine back with the OS reinstalled. Some system data (logs, etc.) in VM appliance is lost, but no personal data is lost. forgot to back up some digital photos he should wipe his computer and re Newest backup is 1 month old, some recent reports and pictures lost. The machine is back in working order in less than 1 hour. that he took of his daughter's play. install. He will need to find his operating Ooops! But at least his computer is system and application install CDs. working again, right? Scenario: Surf to the wrong web site With the Rapid Recovery System Without the Rapid Recovery System A malicious program begins to read over the hard drive for credit card numbers. With the Rapid Recovery System A malicious program begins to read over the hard drive for credit card numbers. The user does not notice any signs of trouble. The FSVM triggers a violation of the data access contract and pauses the VM. The program sends out a small amout of data containing the information discovered. The system asks the user if they want to rollback to the last known good image. The program installs a backdoor for later use by the attacker. Rollback and remount personal data store. The scan is not completed, the information is not sent, the backdoor is prevented. John really wants to see the pics, so he ignores the error Either of these actions cause and copies the “pics” to his the Internet VM to be reset. Scenario: Install a required software update John tries to load the pictures in his photo Internet VM and clicks on them. The builtin firewall of the Without the Rapid Recovery System With the Rapid Recovery System VM, but the action is denied, since the The executable runs and it Rapid Recovery System After the update, several applications cannot find some required components. After the update, several applications cannot find some required components. “pics” are actually executables. An error instantly tries to run its builtin disallows the Internet VM to The user calls tech support and they confirm the problems with this patch. The user calls tech support and they confirm the problems with this patch. message is displayed to John. IRC server and starts scanning create a server. An error The best recommendation is to completely uninstall and reinstall the applications. The user decides to rollback to the last known good image. for personal data. message appears when the It takes a few hours to assemble the installation media, to find the product keys, The machine is back up and running in minutes. Internet restarts. John finds and to follow the instructions. out that these were not pics.
