Wisekeydalian2011presentation
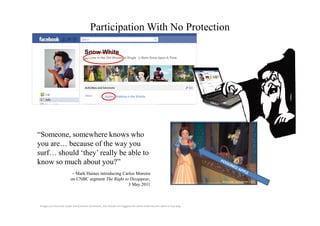
- 1. Participation With No Protection Snow White ↸ Lives in the Old Woods ♥ Single Born Once Upon A Time Apples, Walking in the Woods “Someone, somewhere knows who you are… because of the way you surf… should ‘they’ really be able to know so much about you?” – Mark Haines introducing Carlos Moreira on CNBC segment The Right to Disappear, photo credit: Joe Shlabotnik, Flickr 3 May 2011 Images are licensed under the Creative Commons, use should not suggest the artist endorses this work in any way.
- 2. Protection Allows Participation Personal Data Protection Point-to-point security is oint-to- • Individual control necessary for personal safety • Decentralized • Mobile and efficient business. Strong authentication Transactional Integrity of people, objects and • Safe data transfer products physically and on • Secure payments networks 2011 Copyright WISeKey SA. All Rights Reserved.
- 3. Safe Participation Supports Growth Secure technologies support growth through communications and transactions, without compromising trust and privacy. photo credit: @gueamu, Flickr photo credit: JD Hancock, Flickr Images are licensed under the Creative Commons, use should not suggest the artist endorses this work in any way.
