Me, M.Tech, BE, B.Tech, M.Sc, MCA, Project titles IEEE 2012 Software Project titles, Java, J2EE project titles, Dotnet Project titles, CSE, IT project titles 2012 13.pdf
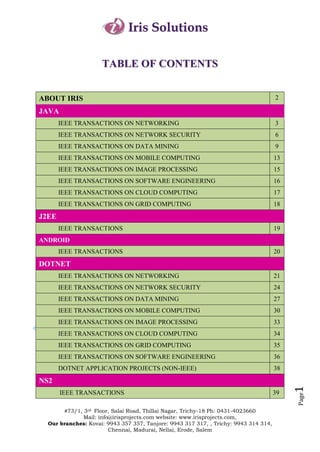
- 1. Iris Solutions TABLE OF CONTENTS ABOUT IRIS 2 JAVA IEEE TRANSACTIONS ON NETWORKING 3 IEEE TRANSACTIONS ON NETWORK SECURITY 6 IEEE TRANSACTIONS ON DATA MINING 9 IEEE TRANSACTIONS ON MOBILE COMPUTING 13 IEEE TRANSACTIONS ON IMAGE PROCESSING 15 IEEE TRANSACTIONS ON SOFTWARE ENGINEERING 16 IEEE TRANSACTIONS ON CLOUD COMPUTING 17 IEEE TRANSACTIONS ON GRID COMPUTING 18 J2EE IEEE TRANSACTIONS 19 ANDROID IEEE TRANSACTIONS 20 DOTNET IEEE TRANSACTIONS ON NETWORKING 21 IEEE TRANSACTIONS ON NETWORK SECURITY 24 IEEE TRANSACTIONS ON DATA MINING 27 IEEE TRANSACTIONS ON MOBILE COMPUTING 30 IEEE TRANSACTIONS ON IMAGE PROCESSING 33 IEEE TRANSACTIONS ON CLOUD COMPUTING 34 IEEE TRANSACTIONS ON GRID COMPUTING 35 IEEE TRANSACTIONS ON SOFTWARE ENGINEERING 36 DOTNET APPLICATION PROJECTS (NON-IEEE) 38 NS2 1 IEEE TRANSACTIONS 39 Page #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
- 2. Iris Solutions About Iris "Iris Solutions - A Boon for Young Technocrats" Global presence of technocrats is no more a dream in this world. We make it possible by ensuring all the quality standards within an individual which has to be the identity of a successful technocrat. Irrespective of the technologies and the domain in which a particular project gets shaped, we support all kind of student needs in terms of monetary values as well as the time factor. Students apart from doing a particular project should know how the project is getting shaped. We are aware in making this thing to happen. Research and Development plays a vital role in enhancing one’s self development in terms of up gradation and moving forward. When you are searching for a good channel to inhibit yourself with such a platform, IRIS comes handy. Apart from providing simulation based training, we also provide industrial experts in sharing their valuable suggestions and even Industry oriented training at required cases. In short we strive hard to fulfill the student requirements in terms of each and every department of the developing their skills. 2 Page #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
- 3. Iris Solutions CONTACT DETAILS Trichy: Iris Solutions, #73/1, 3rd Floor, Salai Road, Thillai Nagar, [Near Hotel Kannappa] Trichy-18. Ph: 0431- 4023660, Mob: 9943 314 314 Kovai: Iris Solutions, #165, 5th Street, [Near Hotel LALA] Gandhipuram, Coimbatore-12. Ph: 0422- 4372816 Mob: 9943 357 357 Tanjore: Iris Solutions, #1520,South Rampart, [ Near Siva Siva Chidambaram Jewellery] Tanjore -1. Ph : 04362-300609 Mob : 9943 317 317 3 Page #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
- 4. Iris Solutions JAVA TECHNOLOGY: JAVA DOMAIN : IEEE TRANSACTIONS ON NETWORKING SNO P.CODE TITLES DESCRIPTION YEAR 1 ISJNW01 Balancing the Trade-Offs In This Project, we propose schemes to 2012 between Query Delay and Data balance the trade-offs between data Availability in MANETs availability and query delay under different system settings and requirements. Mobile nodes in one partition are not able to access data hosted by nodes in other partitions, and hence significantly degrade the performance of data access. To deal with this problem, We apply data replication techniques 2 ISJNW02 MeasuRouting: A Framework In this paper we present a theoretical 2012 for Routing Assisted Traffic framework for MeasuRouting. Monitoring. Furthermore, as proofs-of-concept, we present synthetic and practical monitoring applications to showcase the utility enhancement achieved with MeasuRouting. 3 ISJNW03 Cooperative Profit Sharing in We model Optimal cooperation using 2012 Coalition-Based Resource the theory of transferable payoff Allocation in Wireless coalitional games. We show that the Networks. optimum cooperation strategy, which involves the acquisition, deployment, and allocation of the channels and base stations (to customers), can be computed as the solution of a concave or an integer optimization. We next show that the grand coalition is stable in many different settings. 4 ISJNW04 Bloom Cast: Efficient Full-Text In this paper we propose Bloom Cast, 2012 Retrieval over Unstructured an efficient and effective full-text P2Ps with Guaranteed Recall retrieval scheme, in unstructured P2P networks. Bloom Cast is effective because it guarantees perfect recall rate with high probability. 4 Page #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
- 5. Iris Solutions 5 ISJNW05 On Optimizing Overlay We propose a novel overlay formation 2012 Topologies for Search in algorithm for unstructured P2P Unstructured Peer-to-Peer networks. Based on the file sharing Networks. pattern exhibiting the power-law property, our proposal is unique in that it poses rigorous performance guarantees. 6 ISJNW06 An MDP-Based Dynamic In this paper, we propose an automated Optimization Methodology for Markov Decision Process (MDP)-based Wireless Sensor Networks methodology to prescribe optimal sensor node operation to meet application requirements and adapt to changing environmental stimuli. 2012 Numerical results confirm the optimality of our proposed methodology and reveal that our methodology more closely meets application requirements compared to other feasible policies. 7 ISJNW07 Obtaining Provably Legitimate In this paper, we address The Internet Internet Topologies Topology Problems by providing a framework to generate small, realistic, and policy-aware topologies. We propose HBR, a novel sampling method, which exploits the inherent 2012 hierarchy of the policy-aware Internet topology. We formally prove that our approach generates connected and legitimate topologies, which are compatible with the policy-based routing conventions and rules. 8 ISJNW08 Extrema Propagation: Fast This paper introduces Extrema Distributed Estimation of Sums Propagation, a probabilistic technique and Network Sizes. for distributed estimation of the sum of positive real numbers. The technique relies on the exchange of duplicate insensitive messages and can be applied in flood and/or epidemic settings, where multipath routing occurs; it is tolerant of message loss; it is fast, as the number of 2012 message exchange steps can be made just slightly above the theoretical minimum; and it is fully distributed, with no single point of failure and the result produced at every node. 5 Page #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
- 6. Iris Solutions 9 ISJNW09 Latency Equalization as a New We propose a Latency Equalization Network Service Primitive. (LEQ) service, which equalizes the perceived latency for all clients participating in an interactive network 2012 application. To effectively implement the proposed LEQ service, network support is essential. 10 ISJNW10 Grouping-Enhanced Resilient This paper proposes a scheme, referred Probabilistic En-Route Filtering to as Grouping-enhanced Resilient of Injected False Data in WSNs Probabilistic En-route Filtering (GRPEF). In GRPEF, an efficient distributed algorithm is proposed to group nodes without incurring extra 2012 groups, and a multi axis division based approach for deriving location-aware keys is used to overcome the threshold problem and remove the dependence on the sink immobility and routing protocols 11 ISJNW11 On Achieving Group-Strategy A multicast scheme is stragegyproof if proof Multicast. no receiver has incentive to lie about her true valuation. It is further group strategyproof if no group of colluding 2012 receivers has incentive to lie. We study multicast schemes that target group strategyproofness, in both directed and undirected networks. 12 ISJNW12 Distributed -Optimal User In this paper, we develop a framework Association and Cell Load for user association in infrastructure- Balancing in Wireless based wireless networks, specifically Networks. focused on flow-level cell load balancing under spatially in homogeneous traffic distributions. Our 2012 work encompasses several different user association policies: rate-optimal, throughput-optimal, delay-optimal, and load-equalizing, which we collectively denote α-optimal user association 13 ISJNW13 Opportunistic Flow-Level In this paper, we propose Consistent Latency Estimation Using Net Flow (CNF) architecture for Consistent Net Flow measuring per-flow delay measurements within routers. CNF utilizes the existing Net Flow 2012 architecture that already reports the first and last timestamps per flow, and it proposes hash-based sampling to ensure 6 that two adjacent routers record the Page same flows. #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
- 7. Iris Solutions 14 ISJNW14 Metadata Distribution and This paper makes two contributions. Consistency Techniques for First, we present a dynamic metadata Large-Scale Cluster File distribution policy (DDG) to improve Systems the metadata throughput by using a triple-defined distribution. Second, 2011 S2PC-MP reduces the overhead of failure-free execution and ensures quick recovery in the presence of metadata server failures or client failures. 15 ISJNW15 Self-Reconfigurable Wireless Cooperative Cache can improve the Mesh Networks system performance in wireless P2P networks. We propose a novel asymmetric cooperative cache 2011 approach, where the data requests are transmitted to the cache layer on every node. TECHNOLOGY: JAVA DOMAIN : IEEE TRANSACTIONS ON NETWORK SECURITY SNO P.CODE TITLES DESCRIPTION YEAR 16 ISJNS01 Design and Implementation of We have designed and implemented 2012 TARF: A Trust-Aware Routing TARF, a robust trust-aware routing Framework for WSNs framework for dynamic wireless sensor networks (WSN). Without tight time synchronization or known Geographic information, TARF provides trustworthy and energy-efficient route. Most importantly, TARF proves effective against those harmful attacks developed out of identity deception; the resilience of TARF is verified through extensive evaluation with both simulation and empirical experiments on large-scale WSNs under various scenarios including mobile and RF- shielding network conditions. 17 ISJNS02 Risk-Aware Mitigation for In this paper, we propose a risk-aware 2012 MANET Routing Attacks response mechanism to systematically Cope with the identified routing attacks. Our risk-aware approach is based on an extended Dempster-Shafer mathematical theory of Evidence introducing a notion of importance factors. 7 Page #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
- 8. Iris Solutions 18 ISJNS03 Survivability Experiment and In this paper, we study survivability 2012 Attack Characterization for issues for RFID. We first present an RFID. RFID survivability experiment to define a foundation to measure the degree of survivability of an RFID system under varying attacks. Then we model a series of malicious scenarios using stochastic process algebras and study the different effects of those attacks on the ability of the RFID system to provide critical services even when parts of the system have been damaged. 19 ISJNS04 Detecting and Resolving In this paper, we represent an 2012 Firewall Policy Anomalies innovative policy anomaly management framework for firewalls, adopting a rule-based segmentation technique to identify policy anomalies and derive effective anomaly resolutions. In particular, we articulate a grid-based representation technique, providing an intuitive cognitive sense about policy anomaly. 20 ISJNS05 Automatic Reconfiguration for In this paper, we present a complete 2012 Large-Scale Reliable Storage solution for dynamically changing Systems system membership in a large-scale Byzantine-fault-tolerant system. We present a service that tracks system membership and periodically notifies other system nodes of changes. 21 ISJNS06 Detecting Anomalous Insiders In this paper, we introduce the 2012 in Collaborative Information community anomaly detection system Systems. (CADS), an unsupervised learning framework to detect insider threats based on the access logs of collaborative environments. The framework is based on the observation that typical CIS users tend to form community structures based on the subjects accessed 22 ISJNS07 An Extended Visual Conventional visual secret sharing 2012 Cryptography Algorithm for schemes generate noise-like random General Access Structures. pixels on shares to hide secret images. It suffers a management problem. In this paper, we propose a general approach to solve the above- mentioned problems; the approach can be used for binary 8 secret images in non computer-aided Page decryption environments. #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
- 9. Iris Solutions 23 ISJNS08 Mitigating Distributed Denial of In this paper, we extend port-hopping to 2012 Service Attacks in Multiparty support multiparty applications, by Applications in the Presence of proposing the BIGWHEEL algorithm, Clock Drift for each application server to communicate with multiple clients in a port-hopping manner without the need for group synchronization. Furthermore, we present an adaptive algorithm, HOPERAA, for enabling hopping in the presence of bounded asynchrony, namely, when the communicating parties have clocks with clock drifts. 24 ISJNS09 On the Security and Efficiency Content distribution via network coding 2012 of Content Distribution via has received a lot of attention lately. Network Coding However, direct application of network coding may be insecure. In particular, attackers can inject "bogus” data to corrupt the content distribution process so as to hinder the information dispersal or even deplete the network resource. Therefore, content verification is an important and practical issue when network coding is employed. 25 ISJNS10 Packet-Hiding Methods for In this paper, we address the problem 2012 Preventing Selective Jamming of selective jamming attacks in wireless Attacks. networks. In these attacks, the adversary is active only for a short period of time, selectively targeting messages of high importance. 26 ISJNS11 Stochastic Model of Multi virus In this paper, we study multi virus 2012 Dynamics spreading dynamics, where multiple viruses attempt to infect computers while possibly combating against each other because, for example, they are controlled by multiple botmasters. 27 ISJNS12 Peering Equilibrium Multipath Our scheme relies on a game theory 2012 Routing: A Game Theory modeling, with a non-cooperative Framework for Internet Peering potential game considering both routing Settlements and congestions costs. We compare different PEMP policies to BGP Multipath schemes by emulating a realistic peering scenario. 28 ISJNS13 Modeling and Detection of Our scheme uses the Power Spectral 2011 Camouflaging Worm Density (PSD) distribution of the scan traffic volume and its corresponding Spectral Flatness Measure (SFM) to 9 distinguish the C-Worm traffic from Page background traffic. The performance #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
- 10. Iris Solutions data clearly demonstrates that our scheme can effectively detect the C- Worm propagation.two heuristic algorithms for the two sub problems. 29 ISJNS14 Analysis of a Botnet Takeover We present the design of an advanced 2011 hybrid peer-to-peer botnet. Compared with current botnets, the proposed botnet is harder to be shut down, monitored, and hijacked. It provides individualized encryption and control traffic dispersion. 30 ISJNS15 Efficient Network Modification As real-time traffic such as video or 2011 to Improve QoS Stability at voice increases on the Internet, ISPs are Failures required to provide stable quality as well as connectivity at failures. For ISPs, how to effectively improve the stability of these qualities at failures with the minimum investment cost is an important issue, and they need to effectively select a limited number of locations to add link facilities. TECHNOLOGY: JAVA DOMAIN : IEEE TRANSACTIONS ON DATA MINING SNO P.CODE TITLES DESCRIPTION YEAR 31 ISJDM01 A Survival Modeling Approach In this paper, we propose a survival 2012 to Biomedical modeling approach to promoting Search Result Diversification ranking diversity for biomedical Using Wikipedia information retrieval. The proposed approach concerns with finding relevant documents that can deliver more different aspects of a query. First, two probabilistic models derived from the survival analysis theory are proposed for measuring aspect novelty. 32 ISJDM02 A Fuzzy Approach for In this paper, we propose a new fuzzy 2012 Multitype Relational clustering approach for multitype Data Clustering relational data (FC-MR). In FC-MR, different types of objects are clustered simultaneously. An object is assigned a large membership with respect to a cluster if its related objects in this cluster have high rankings. 10 Page #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
- 11. Iris Solutions 33 ISJDM03 Anonimos: An LP-Based We present Anonimos, a Linear 2012 Approach for Programming-based technique for Anonymizing Weighted Social anonymization of edge weights that Network Graphs preserves linear properties of graphs. Such properties form the foundation of many important graph-theoretic algorithms such as shortest paths problem, k-nearest neighbors, minimum cost spanning Tree and maximizing information spread. 34 ISJDM04 A Methodology for Direct and In this paper, we tackle discrimination 2012 Indirect Discrimination prevention in data mining and propose Prevention in Data Mining new techniques applicable for direct or indirect Discrimination prevention individually or both at the same time. We discuss how to clean training datasets and outsourced datasets in such a way that direct and/or indirect discriminatory decision rules are converted to legitimate (non- discriminatory) Classification rules. 35 ISJDM05 Mining Web Graphs for In this paper, aiming at providing a 2012 Recommendations general framework on mining Web graphs for recommendations, (1) we first propose a novel diffusion method which propagates similarities between different nodes and generates recommendations; (2) then we illustrate how to generalize different recommendation problems into our graph diffusion framework. 36 ISJDM06 Prediction of User’s Web- Predicting user's behavior while serving 2012 Browsing Behavior: the Internet can be applied effectively in Application of Markov Model various critical applications. Such application has traditional tradeoffs between modeling complexity and prediction accuracy. In this paper, we analyze and study Markov model and all- Kth Markov model in Web prediction. We propose a new modified Markov model to alleviate the issue of scalability in the number of paths. 37 ISJDM07 Prototype Selection for Nearest This paper provides a survey of the 2012 Neighbor prototype selection methods proposed Classification: Taxonomy and in the literature from a theoretical and 11 Empirical Study empirical point of view. Considering a theoretical point of view, we propose a Page taxonomy based on the main #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
- 12. Iris Solutions characteristics presented in prototype selection and we analyze their advantages and drawbacks, the nearest neighbor classifier suffers from several drawbacks such as high storage requirements, low efficiency in classification response, and low noise Tolerance. 38 ISJDM08 Query Planning for Continuous We present a low-cost, scalable 2012 Aggregation technique to answer continuous Queries over a Network of Data aggregation queries using a network of Aggregators aggregators of dynamic data items. In such a network of data aggregators, each data aggregator serves a set of data items at specific coherencies. 39 ISJDM09 Revealing Density-Based In this paper, we introduce a novel 2012 Clustering Structure density-based network clustering from the Core-Connected Tree method, called gSkeletonClu (graph- of a Network skeleton based clustering). By projecting an undirected network to its core-connected maximal spanning tree, the clustering problem can be converted to detect core connectivity components on the tree. 40 ISJDM10 Scalable Learning of Collective This study of collective behavior is to 2012 Behavior understand how individuals behave in a social networking environment. Oceans of data generated by social media like Facebook, Twitter, Flickr, and YouTube present opportunities and challenges to study collective behavior on a large scale. In this work, we aim to learn to predict collective behavior in social media 41 ISJDM11 Weakly Supervised Joint This paper proposes a novel 2012 Sentiment-Topic probabilistic modeling framework Detection from Text called joint sentiment-topic (JST) model based on latent Dirichlet allocation (LDA), which detects sentiment and topic simultaneously from text. A reparameterized version of the JST model called Reverse-JST, obtained by reversing the sequence of sentiment and topic generation in the modeling process, is also studied. 12 Page #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
- 13. Iris Solutions 42 ISJDM12 Effective Navigation of Query Ranking and categorization, which can 2011 Results Based on Concept also be combined, have been proposed Hierarchies to alleviate this information overload problem. Results categorization for biomedical databases is the focus of this work. A natural way to organize biomedical citations is according to their MeSH annotations. 43 ISJDM13 Automatic Discovery of We propose a novel, automatically 2011 Personal Name Aliases from the extracted lexical pattern-based approach Web to efficiently extract a large set of candidate aliases from snippets retrieved from a web search engine. We define numerous ranking scores to evaluate candidate aliases using three approaches: lexical pattern frequency, word co-occurrences in an anchor text graph, and page counts on the web 44 ISJDM14 IR-Tree: An Efficient Index for Given a geographic query that is 2011 Geographic Document Search composed of query keywords and a location, a geographic search engine retrieves documents that are the most textually and spatially relevant to the query keywords and the location, respectively, and ranks the retrieved documents according to their joint textual and spatial relevances to the query. 45 ISJDM15 Anonymous Publication of The problem of anonymizing sparse, 2011 Sensitive Transactional Data high dimensional transactional data is solved through methods based on 1) local NN-search and 2) global data reorganization. 46 ISJDM16 Managing Multidimensional A P2P-based framework supporting the 2011 Historical Aggregate Data in extraction of aggregates from historical Unstructured P2P Networks multidimensional data is proposed, which provides efficient robust query evaluation 13 Page #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
- 14. Iris Solutions TECHNOLOGY: JAVA DOMAIN : IEEE TRANSACTIONS ON MOBILE COMPUTING SNO P.CODE TITLES DESCRIPTION YEAR 47 ISJMC01 The Boomerang Protocol: We present the boomerang protocol to 2012 Tying Data to Geographic efficiently retain information at a Locations in Mobile particular geographic location in a Disconnected Networks sparse network of highly mobile nodes without using infrastructure networks. To retain information around certain physical location, each mobile device passing that location will carry the information for a short while. 48 ISJMC02 Nature-Inspired Self- In this paper, we present new models 2012 Organization, Control, and and algorithms for control and Optimization in Heterogeneous optimization of a class of next Wireless Networks generation communication networks: Hierarchical Heterogeneous Wireless Networks (HHWNs), under real-world physical constraints. Two biology- inspired techniques, a Flocking Algorithm (FA) and a Particle Swarm Optimizer (PSO), are investigated in this context. 49 ISJMC03 A Cost Analysis Framework for In this paper, we have developed 2012 NEMO analytical framework to measure the Prefix Delegation-Based costs of the basic protocol for Network Schemes Mobility (NEMO), and four representative prefix delegation-based schemes. Our results show that cost of packet delivery through the partially optimized route dominates over other costs. 50 ISJMC04 OMAN: A Mobile Ad Hoc In this paper, we present a high-level 2012 Network Design System view of the OMAN architecture, review specific mathematical models used in the network representation, and show how OMAN is used to evaluate tradeoffs in MANET design. Specifically, we cover three case studies of optimization. 1-robust power control under uncertain channel information for a single physical layer snapshot. 2- scheduling with the availability of directional radiation patterns. 3- 14 optimizing topology through movement Page planning of relay nodes. #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
- 15. Iris Solutions 51 ISJMC05 Energy-Efficient Cooperative In this paper, we formulate the resource 2012 Video Distribution with allocation problem for general multihop Statistical QoS Provisions over multicast network flows and derive the Wireless Networks optimal solution that minimizes the total energy consumption while guaranteeing a statistical end-to-end delay bound on each network path. 52 ISJMC06 Leveraging the Algebraic In this paper, we consider the 2012 Connectivity implications of spectrum heterogeneity of a Cognitive Network for on connectivity and routing in a Routing Design Cognitive Radio Ad Hoc Network (CRAHN). We study the Laplacian spectrum of the CRAHN graph when the activity of primary users is considered. We introduce the cognitive algebraic connectivity, i.e., the second smallest eigenvalue of the Laplacian of a graph, in a cognitive scenario. 53 ISJMC07 Efficient Virtual Backbone In this paper, we will study a directional 2012 Construction virtual backbone (VB) in the network with Routing Cost Constraint in where directional antennas are used. Wireless When constructing a VB, we will take Networks Using Directional routing and broadcasting into account Antennas since they are two common operations in wireless networks. Hence, we will study a VB with guaranteed routing costs, named α Minimum rOuting Cost Directional VB (α-MOC-DVB). 54 ISJMC08 Stateless Multicast Protocol for In this paper, we have developed a 2012 Ad Hoc Networks. stateless receiver-based multicast (RBMulticast) protocol that simply uses a list of the multicast members' (e.g., sinks') addresses, embedded in packet headers, to enable receivers to decide the best way to forward the multicast traffic. 55 ISJMC09 Detection of Selfish CCA tuning can be exploited by selfish 2012 Manipulation of Carrier nodes to obtain an unfair share of the Sensing in 802.11 Networks available bandwidth. Specifically, a selfish entity can manipulate the CCA threshold to ignore ongoing transmissions; this increases the probability of accessing the medium and provides the entity a higher, unfair share of the bandwidth. 15 56 ISDMC10 Message-Efficient Location A better prediction model can 2011 Prediction for Mobile Objects in significantly reduce power consumption Page Wireless Sensor Networks in a wireless sensor network because #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
- 16. Iris Solutions Using a Maximum Likelihood fewer redundant sensors will be Technique activated to keep monitoring the object. The Gauss-Markov mobility model is best mobility models to describe object trajectory because it can capture the correlation of object velocity in time. TECHNOLOGY: JAVA DOMAIN : IEEE TRANSACTIONS ON IMAGE PROCESSING SNO P.CODE TITLES DESCRIPTION YEAR 57 ISJIP01 Anomaly Detection and The popular RX anomaly detector is 2012 Reconstruction from Random derived for the case in which global Projections anomalies are to be identified directly in the random-projection domain, and it is determined via both random simulation, as well as empirical observation that strongly anomalous vectors are likely to be identifiable by the projection-domain RX detector even in low-dimensional projections. 58 ISJIP02 Web and Personal Image In this paper, we propose a new 2012 Annotation by Mining Label inductive algorithm for image Correlation with Relaxed Visual annotation by integrating label Graph Embedding correlation mining and visual similarity mining into a joint framework. We first construct a graph model according to image visual features. A multilabel classifier is then trained by simultaneously uncovering the shared structure common to different labels and the visual graph embedded label prediction matrix for image annotation. 59 ISJIP03 An Alternating Minimization In this paper, we propose a new 2012 Algorithm for Binary Image minimization model by making use of a Restoration new variable to enforce the image to be binary. Based on the proposed minimization model, we present a fast alternating minimization algorithm for binary image restoration. We prove the convergence of the proposed alternating minimization algorithm 60 ISJIP04 Efficient Relevance Feedback Content-based image retrieval is the 2011 mainstay of image retrieval systems. Relevance feedback techniques were 16 incorporated into CBIR such that more Page precise results can be obtained by taking user’s Feedbacks into account. #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
- 17. Iris Solutions 61 ISJIP05 High-quality Reflection Deal with a problem of separating the 2011 Separation using Polarized effect of reflection from images Images captured behind glass. The input consists of multiple polarized images captured from the same view point but with different polarizer angles. The output is the high quality separation of the reflection layer and the background layer from the images. TECHNOLOGY: JAVA DOMAIN : IEEE TRANSACTIONS ON SOFTWARE ENGINEERING SNO P.CODE TITLES DESCRIPTION YEAR 62 ISJSE01 Automated Behavioral Testing We present a technique to test Java 2012 of Refactoring Engines refactoring engines. It automates test input generation by using a Java program generator that exhaustively generates programs for a given scope of Java declarations. The refactoring under2test is applied to each generated program. The technique uses SAFEREFACTOR, a tool for detecting behavioral changes, as oracle to evaluate the correctness of these transformations. 63 ISJSE02 Towards Comprehensible This study contributes to the literature 2012 Software Fault Prediction by considering 15 different Bayesian Models Using Bayesian Network (BN) classifiers and Network Classifiers comparing them to other popular machine learning techniques. Furthermore, the applicability of the Markov blanket principle for feature selection, which is a natural extension to BN theory, is investigated. 64 ISJSE03 Using Dependency Structures In this paper, we present a family of test 2012 for Prioritisation of Functional case prioritisation techniques that use Test Suites the dependency information from a test suite to prioritise that test suite. The nature of the techniques preserves the dependencies in the test ordering. 65 ISJSE04 Genetic Algorithms for A system which uses a genetic 2011 Randomized Unit Testing algorithm to find parameters for randomized unit testing that optimize test coverage. Designing GAs is 17 somewhat of a black art. We therefore use a feature subset selection tool to Page assess the size and content of the #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
- 18. Iris Solutions representations within the GA. TECHNOLOGY: JAVA DOMAIN : IEEE TRANSACTIONS ON CLOUD COMPUTING SNO P.CODE TITLES DESCRIPTION YEAR 66 ISJCC01 pCloud: A Distributed System In this paper we present pCloud, a 2012 for Practical PIR distributed system that constitutes the first attempt towards practical cPIR. Our approach assumes a disk-based architecture that retrieves one page with a single query. Using a striping technique, we distribute the database to a number of cooperative peers, and leverage their computational resources to process cPIR queries in parallel. We implemented pCloud on the PlanetLab network, and experimented extensively with several system parameters. results 67 ISJCC02 A Gossip Protocol for Dynamic We address the problem of dynamic 2012 Resource Management in Large resource management for a large-scale Cloud Environments. cloud environment. Our contribution includes outlining a distributed middleware architecture and presenting one of its key elements: a gossip protocol that (1) ensures fair resource allocation among sites/applications, (2) dynamically adapts the allocation to load changes and (3) scales both in the number of physical machines and sites/applications. 68 ISJCC03 A Novel Process Network In this paper, we explore a novel 2012 Model for Interacting Context- approach to model dynamic behaviors aware Web Services of interacting context-aware web services. It aims to effectively process and take advantage of contexts and realize behavior adaptation of web services, further to facilitate the development of context-aware application of web services. 69 ISJCC04 Multicloud Deployment of We deploy a computing cluster on the 2011 Computing Clusters for Loosely top of a multicloud infrastructure, for Coupled MTC Applications solving loosely coupled Many-Task Computing applications. In this way, 18 the cluster nodes can be provisioned with resources from different clouds to Page improve the cost effectiveness of the #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
- 19. Iris Solutions deployment, or to implement high- availability strategies. 70 ISJCC05 Enabling Public Auditability To achieve efficient data dynamics, we 2011 and Data Dynamics for Storage improve the existing proof of storage Security in Cloud Computing models by manipulating the classic Merkle Hash Tree construction for block tag authentication. To support efficient handling of multiple auditing tasks, the technique of bilinear aggregate signature to extend our main result into a multiuser setting, where TPA can perform multiple auditing tasks simultaneously. TECHNOLOGY: JAVA DOMAIN : IEEE TRANSACTIONS ON GRID COMPUTING SNO P.CODE TITLES DESCRIPTION YEAR 71 ISJGC01 Business-OWL (BOWL)—A This paper introduces the Business- 2012 Hierarchical Task Network OWL (BOWL), an ontology rooted in Ontology for Dynamic Business the Web Ontology Language (OWL), Process Decomposition and and modeled as a Hierarchical Task Formulation Network (HTN) for the dynamic formation of business processes 72 ISJGC02 Detecting And Resolving The advent of emerging computing 2012 Firewall Policy Anomalies technologies such as service-oriented architecture and cloud computing has enabled us to perform business services more efficiently and effectively. 73 ISJGC03 Online System for Grid In this paper, we present the design and 2012 Resource Monitoring and evaluation of system architecture for Machine Learning-Based grid resource monitoring and prediction. Prediction We discuss the key issues for system implementation, including machine learning-based methodologies for modeling and optimization of resource prediction models. 74 ISJGC04 SOAP Processing Performance SOAP communications produce 2011 and Enhancement considerable network traffic, making them unfit for distributed, loosely coupled and heterogeneous computing environments such as the open Internet. They introduce higher latency and processing delays than other 19 technologies, like Java RMI & CORBA. WS research has recently focused on Page SOAP performance enhancement. #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
- 20. Iris Solutions 75 ISJGC05 Weather data sharing system: Intelligent agents can play an important 2011 an agent-based distributed data role in helping achieve the ‘data grid’ management vision. In this study, the authors present a multi-agent-based framework to implement manage, share and query weather data in a geographical distributed environment, named weather data sharing system J2EE TECHNOLOGY: J2EE DOMAIN : IEEE TRANSACTIONS SNO P.CODE TITLES DESCRIPTION YEAR 1 ISJ2EE1 A Link-Based Cluster Ensemble The paper presents an analysis that 2012 Approach for Categorical Data suggests this problem degrades the Clustering quality of the clustering result, and it presents a new link-based approach, which improves the conventional matrix by discovering unknown entries through similarity between clusters in an ensemble. 2 ISJ2EE2 Low-Rank Kernel Matrix In this paper, we propose ECKF, a 2012 Factorization for Large-Scale general framework for evolutionary Evolutionary Clustering clustering large-scale data based on low-rank kernel matrix factorization. To the best of our knowledge, this is the first work that clusters large evolutionary data sets by the amalgamation of low-rank matrix approximation methods and matrix factorization-based clustering. 3 ISJ2EE3 Prediction of User’s Web- In this paper, we analyze and study 2012 Browsing Behavior: Markov model and all- Kth Markov Application of Markov Model model in Web prediction. We propose a new modified Markov model to alleviate the issue of scalability in the number of paths. 4 ISJ2EE4 Integrating Visual Saliency and Visual saliency. From visual aspect, it is 2011 Consistency for Re-ranking obvious that salient images would be Image Search Results easier to catch users eyes and it is observed that these visually salient 20 images in the front pages are often Page relevant to the users query. #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
- 21. Iris Solutions 5 ISJ2EE5 Matching Estimates of the We compare the use of OLS regression 2011 Effect of College Attendance on and propensity score matching methods, Individual Income and incorporate the role of ldquo common support .rdquo Using data from the CHFLS 6 ISJ2EE6 Research on B2B E-Business The model to B2B E-Business System 2010 System of Bookshop Based on of Bookshop, which includes the Web Service management subsystem of order, book information, bookshop information, bill information, and customer relations. ANROID TECHNOLOGY: ANROID DOMAIN : IEEE TRANSACTIONS SNO P.CODE TITLES DESCRIPTION YEAR 1 ISAI01 Proteus: Multi-flow Diversity A novel approach to achieve co- 2012 Routing for Wireless Networks operative transmission links in VMISO with Cooperative Transmissions (Virtual Multi Input and Single Output), here we use a proteus an adaptive diversity routing protocol to overcome the number transmitter for each and its diversity. 2 ISAI02 A Framework for Personal A technique to mining and prediction of 2012 Mobile Commerce mobile users behavior in order to Pattern Mining and Prediction recommend the stores with a Personal Mobile Commerce Pattern Mine (PMCP-Mine) algorithm. 3 ISAI03 Privacy control in smart phones This framework shows by embedding a 2012 using semantically semantically rich policy based on a rich reasoning and context device context in the smart phone modeling framework, a policy based system that reasons over a user’s dynamic context and constrains the information flow among applications by extending the open source Android framework 21 Page #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
- 22. Iris Solutions DOTNET TECHNOLOGY: DOTNET DOMAIN : IEEE TRANSACTIONS ON NETWORKING SNO P.CODE TITLES DESCRIPTION YEAR 1 ISDNW01 An Efficient Adaptive A deadlock-free minimal routing 2012 Deadlock-Free Routing algorithm called clue is first proposed Algorithm for Torus for VCT (virtual cut-through)-switched Networks. tori. Only two virtual channels are required. One channel is applied in the deadlock-free routing algorithm for the mesh sub network based on a known base routing scheme, such as, negative- first or dimension-order routing. 2 ISDNW02 The Three-Tier Security This Paper describes a three-tier general 2012 Scheme in Wireless Sensor framework that permits the use of any Networks with Mobile Sinks pairwise key predistribution scheme as its basic component. The new frame- work requires two separate key pools, one for the mobile sink to access the network, and one for pairwise key establishment between the sensors. 3 ISDNW03 Efficient Error Estimating This paper proposes the novel concept 2012 Coding: Feasibility and of error estimating coding (EEC). Applications Without correcting the errors in the packet, EEC enables the receiver of the packet to estimate the packet’s bit error rate, which is perhaps the most important meta-information of a partially correct packet. 4 ISDNW04 Independent Directed Acyclic In this paper. Link-independent (node- 2012 Graphs for Resilient Multipath independent) DAGs satisfy the property Routing that any path from a source to the root on one DAG is link-disjoint (node- disjoint) with any path from the source to the root on the other DAG. Given a network, we develop polynomial-time algorithms to compute link-independent and node-independent DAGs. 5 ISDNW05 Modeling and Analysis of Multi cluster systems have emerged as a 2012 22 Communication Networks in promising infrastructure for Page Multicluster Systems under provisioning of cost-effective high- #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
- 23. Iris Solutions Spatio-Temporal Bursty Traffic performance computing and communications. Analytical models of communication networks in cluster systems have been widely reported. 6 ISDNW06 Improving End-to-End Routing We propose a topology aware routing 2012 Performance of Greedy (TAR) protocol that efficiently encodes Forwarding in Sensor Networks a network topology into a low- dimensional virtual coordinate space where hop distances between pairwise nodes are preserved. Based on precise hop distance comparison, TAR can assist greedy forwarding to find the right neighbor that is one hop closer to the destination and achieve high success ratio of packet delivery without location information. 7 ISDNW07 DCS: Distributed In this paper, we propose distributed 2012 Asynchronous Clock asynchronous clock synchronization Synchronization in Delay (DCS) protocol for Delay Tolerant Tolerant Networks Networks (DTNs). Different from existing clock synchronization protocols, the proposed DCS protocol can achieve global clock synchronization among mobile nodes within the network over asynchronous and intermittent connections with long delays. 8 ISDNW08 Semantic-Aware Metadata This paper proposes a novel 2012 Organization Paradigm in decentralized semantic-aware metadata Next-Generation File Systems organization, called Smart Store, which exploits semantics of files’ metadata to judiciously aggregate correlated files into semantic-aware groups by using information retrieval tools. 9 ISDNW09 A Greedy Link Scheduler for In this paper, we address the problem of 2012 Wireless Networks With link scheduling in multihop wireless Gaussian Multiple-Access and networks containing nodes with BC and Broadcast Channels MAC capabilities. We first propose an interference model that extends protocol interference models, originally designed for point-to-point channels, to include the possibility of BCs and MACs. 10 ISDNW10 Finding Cheap Routes in Prot- In this paper, we explore the economic 2012 23 Driven Opportunistic Spectrum aspects of routing/relaying in a profit- Access Networks: A Truthful driven opportunistic spectrum access Page Mechanism (OSA) network. In this network, #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
- 24. Iris Solutions Design Approach primary users lease their licensed spectrum to secondary radio (SR) providers, who in turn provide opportunistic routing/relaying service to end-users if this service is portable. 11 ISDNW11 MeasuRouting: A Framework In this paper we present a theoretical 2012 for Routing Assisted Traffic framework for MeasuRouting. Monitoring Furthermore, as proofs-of-concept, we present synthetic and practical monitoring applications to showcase the utility enhancement achieved with MeasuRouting. 12 ISDNW12 AMPLE: An Adaptive Traffic In this article, we introduce AMPLE - 2012 Engineering System Based on an efficient traffic engineering and Virtual Routing Topologies management system that performs adaptive traffic control by using multiple virtualized routing topologies 13 ISDNW13 Research on cloud computing A traditional method of using load 2011 application in the peer-to-peer balancing and multiple buffer servers based video–on-demand we found that the performance of systems Hadoop framework was improved significantly in feasibility and efficiency when dealing with large data. 14 ISDNW14 A Secure Communication A four terminal network with a source, 2011 Game with a Relay Helping the a destination, an eavesdropper and a Eavesdropper jammer relay is investigated. The source and the jammer relay have conflicting interests. This problem is formulated as a non-cooperative two- player zero sum continuous game. Two cases are studied: 1) the jammer relay does not hear the source, and 2) the jammer relay is given the source signal. 15 ISDNW15 Optical Layer Security in Fiber- Our goal is the security threats in an 2011 Optic Networks optical network as well as present several existing optical techniques to improve the security. In the first part of this paper, we discuss various types of security threats that could appear in the optical layer of an optical network, including jamming, physical infrastructure attacks, eavesdropping and interception. 16 ISDNW16 Predictive Resource The monitoring system preserves a high 2011 24 Management of Multiple degree of flexibility, increasing the Monitoring Application range of applications and network Page scenarios where it can be used. We #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
- 25. Iris Solutions implemented our load-shedding-based resource management scheme in an existing network monitoring system and deployed it in a large research and educational network. 17 ISDNW17 Active Monitoring and Alarm It focuses the error locations 2010 Management for Fault (Localization) which is occurring on the Localization in Transparent Optical Networks and when we All-Optical Networks monitoring the fault localization, we arrange the alarm to make active the users. 18 ISDNW18 Logoot-Undo: Distributed This project presents the Logoot-Undo 2010 Collaborative Editing System Commutative Replicated Data Type on P2P Networks algorithm, which integrates the “undo anywhere, anytime” feature on the replicated data’s in peer to peer network for reducing the cost of undo feature. 19 ISDNW19 Multiuser Diversity Gain in An large cognitive networks granted 2010 Cognitive Networks concurrent spectrum access with license-holding users and Dynamic allocation of resources to the best link in multiuser n/w. TECHNOLOGY: DOTNET DOMAIN : IEEE TRANSACTIONS ON NETWORK SECURITY SNO P.CODE TITLES DESCRIPTION YEAR 20 ISDNS01 Extending Attack Graph-Based The attack graph is an abstraction that 2012 Security Metrics and reveals the ways an attacker can Aggregating Their Application leverage vulnerabilities in a network to violate a security policy. When used with attack graph-based security metrics, the attack graph may be used to quantitatively assess security relevant aspects of a network. 21 ISDNS02 Secured Trust: A Dynamic We present in this paper a dynamic trust 2012 Trust Computation Model for computation model called Secured Communication "SecuredTrust.” In this paper, we first in Multi agent Systems analyze the different factors related to evaluating the trust of an agent and then propose a comprehensive quantitative model for measuring such trust. We also propose a novel load-balancing algorithm based on the different factors defined in our model. 25 22 ISDNS03 Persuasive Cued Click-Points: This paper presents an integrated 2012 Page Design, Implementation, and evaluation of the Persuasive Cued #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, , Trichy: 9943 314 314, Chennai, Madurai, Nellai, Erode, Salem
